When configuring today’s servers for modern workloads, there is really no place any longer for running a web server without an SSL certificate. Encrypting web traffic is a basic requirement for security. There are many different tools available for SSL certificates, including LetsEncrypt. LetsEncrypt is a free SSL certificate authority that allows easily adding SSL certs to your server without any cost. In this post, we will take a look at LetsEncrypt Windows Server 2019 configuration and see how you can add a LetsEncrypt certificate to your Windows Server 2019 server.
What is LetsEncrypt?
What is Let’s Encrypt? Most likely, by now, you have already heard about LetsEncrypt certificates and maybe have even used them before. LetsEncrypt is a public nonprofile certificate authority (CA) that has issued over a billion certificates so far and protects 225 million websites.
So, as far as being tried and true, it has thus far proven itself with the number of certs in production currently used. I have seen some criticize using LetsEncrypt certs for production servers, however, in my opinion, if there was a major flaw here, it would have been exploited by now.
What I like about LetsEncrypt is that it is free and provides the tools to automate certificate installation and renewals.
The thing to note about LetsEncrypt is it is a bit more involved in your SSL certificate lifecycle management. LetsEncrypt certificates expire after 90 days.
This means that you will have the need to renew your certificates much more often than a pay-for SSL certificate. However, LetsEncrypt has automated options to perform the auto-renewal using automation.
Install LetsEncrypt SSL Certificates in Windows Server 2019
So, getting right down to business, how do you install LetsEncrypt SSL certificates in Windows Server 2019? There is a specialized tool that is used for LetsEncrypt for Windows called the win-acme tool.
The easiest way to grab a copy of win-acme is to visit the official site for the open source tool and download the latest version. You can do that here:
Win-acme has many really great features built into the tool including the following:
- Simple interface that allows a wizard-driven approach to creating and installing certificates on a Windows Server 2012, 2016, or 2019 IIS server
- Advanced options for use with Apache or Exchange Server running on a Windows Server 2012, 2016, or 2019 server
- The tool also automatically creates the needed Windows scheduled tasks for automatic certificate renewal
- You can create SSL certificates with wildcards, international names, OCSP must staple extension, and other advanced operations such as reusing private keys, EC crypto or using your own CSR
- Advanced tools for Azure, Route53, Cloudflare and others
- Unattended and automated operation
- Easily used with custom PowerShell scripts as well as building your own plugins using C#
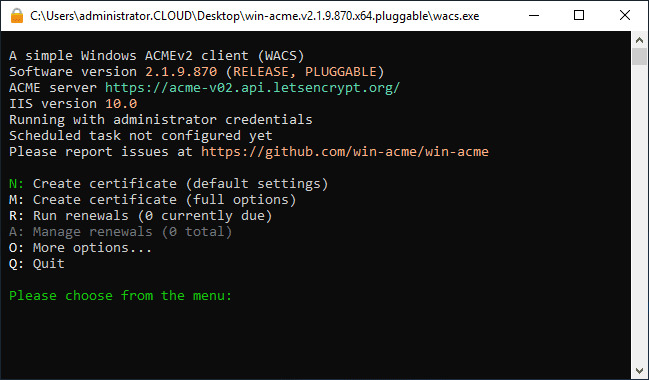
Let’s run through some of the menus of the LetsEncrypt win-acme tool. When you first launch the tool, you will see a fairly wizard-driven menu that allows you to choose what you are trying to accomplish.
The options that are highlighted in green are the defaults. So, if you just go down through the menu hitting enter, these are the options that will be selected.
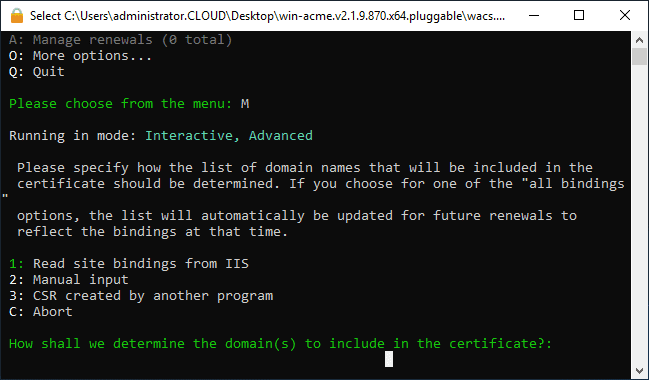
Just to show some of the options that can be set, here I have select to Create certificate (full options) for a more verbose set of configuration.
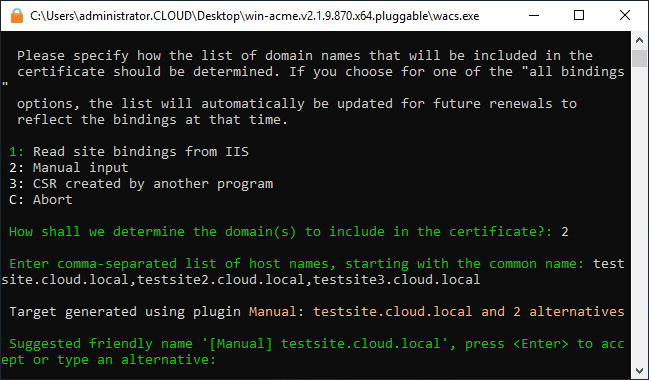
The first thing you will see and be able to configure is how you want to read the bindings. You can have the tool read the bindings automatically from what you have configured in IIS. This is the easiest option. You can also manually configure the options.
Below, I have chosen to manually configure the bindings. I am entering a subject name and several alternate names.
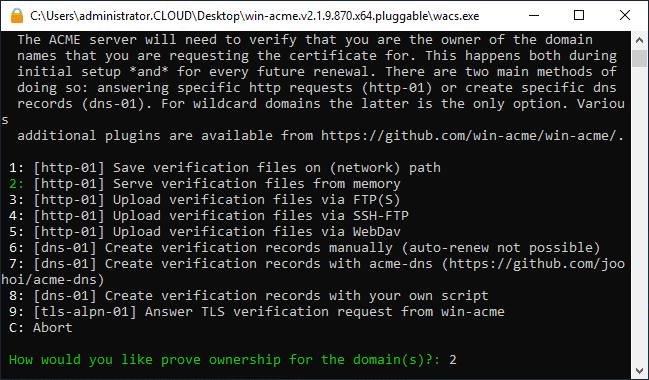
Next, you choose how you want to verify the ownership of the domain that you are keying the certificate for. The ACME server needs to be able to verify you are the owner of the domain. As is noted in the wizard, this happens both during the initial setup and for all renewals in the future.
You will need to consider the method you choose her for autorenewal purposes. As noted, with some of the methods such as the Create verification records manually, the auto-renew option is not possible.
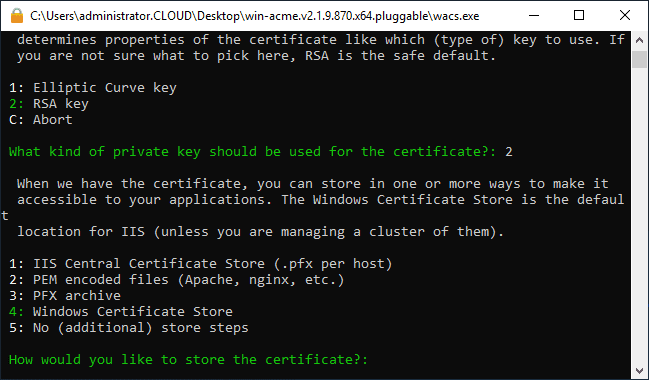
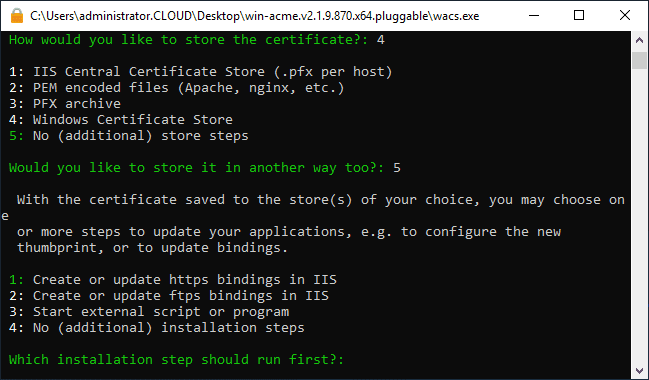
Next, you can select what kind of private key is used for the certificate. There are several options to choose from:
- IIS Central Certificate store (.pfx per host)
- PEM encoded files for Apache, Nginx, and other Linux servers
- PFX archive
- Windows Certificate Store (default)
- No additional store steps
You can also choose a secondary method of storing the private key. YOu can choose basically the same options as a secondary storage method.
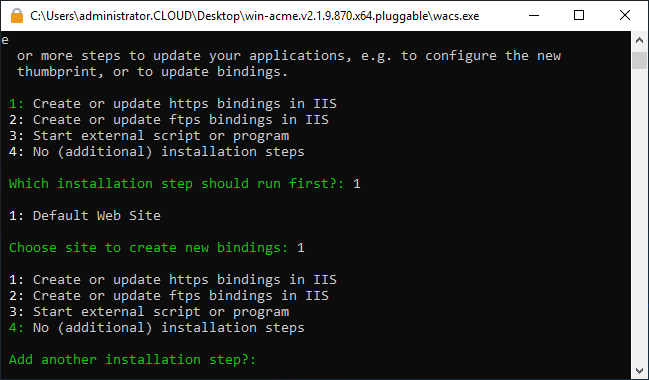
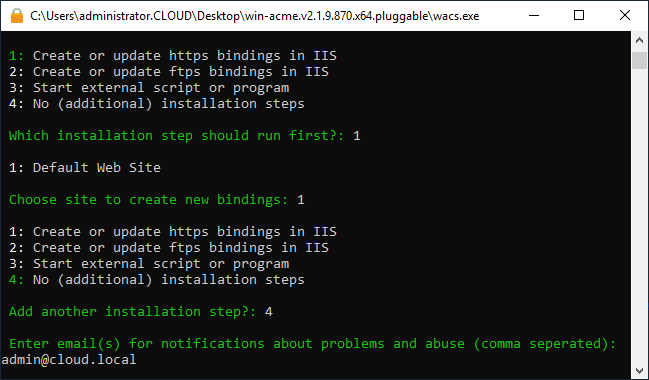
Next, you choose how you want the win-acme tool to update the bindings. You can choose to:
- Create or update https bindings in IIS
- Create or update ftps bindings in IIS
- Start external script or program
- No additional installation steps
You can enter emails for notifications about problems and abuse as well in the final step before the updates happen.
LetsEncrypt Automatic Renewal options in Windows Server 2019
As shown, LetsEncrypt allows you to perform automated SSL cert renewals.
- Take a look at the page here: https://www.win-acme.com/manual/automatic-renewal
Scheduled task
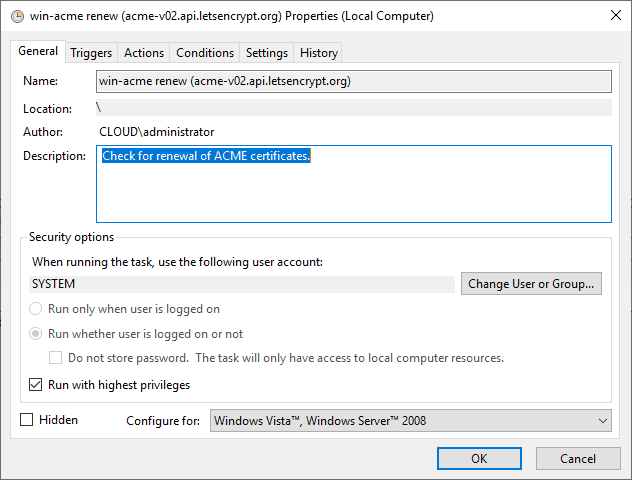
LetsEncrypt automatically creates a Windows scheduled task that automatically checks for renewal and performs renewal.
A single scheduled task is responsible to renew all certificates created by the program, but will only do so when it’s actually neccessary.
The task runs every day and checks two conditions to determine if it should renew:
- If the certificate is aging. This is based on the known history stored in the file.
- If any bindings changes have been made in the IIS site bindings. This may be the case if an additional binding has been added to the server.
Configuring Renewals
The renewal period that is set to 55 days by default, is configurable in the settings.json file. Other properties of the scheduled task can also be changed that way, or from the Task Scheduler itself, as long as its name left unmodified. By default it runs at 9:00 am using the built-in SYSTEM account
Monitoring Win-Acme Renewals
The renewal process and tasks are written to the Windows Event Viewer. You can also take a look at the log files for the process. These are located at c:%programdata%win-acmelogs.
As shown in the screenshot above, you can also set up email notifications. The first step to do this is to configure a mail server in the settings.json file. Then when setting up the certificate, you can enter the email address that you want to be notified.
Wrapping Up
LetsEncrypt is a great way to have free SSL certificates that are fully valid and serve as a great option for organizations looking to ensure they have all HTTPS traffic secured with a proper certificate.
While the lifecycle management of LetsEncrypt certificates are a bit more involved, the automation options take the heavy lifting out of this process. As shown, an automatic scheduled task is created in Windows Server that helps to take care of the renewal process.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.