What if you have a need for running Windows Server 2019 as a remote desktop services server but you are not running a domain? If your Windows Server 2019 server is in a workgroup in an edge environment possibly and you need to run remote desktop services, is this possible? Also, what about setting up Windows Server 2019 remote desktop gateway with a workgroup? Is that possible? Can you install both on the same server in a workgroup? In this post, we will take a look at the use case of running Windows Server 2019 remote desktop services without domain services running and answer these other questions regarding the workgroup configuration with RDS and Windows Server 2019.
Remote Desktop Services without Domain use cases
First of all, before you know how to do something, it is good to know why you would want to do it. Especially in production, we don’t simply want to do something just because we can without a good reason.
We all know that Windows Server in an Active Directory domain has access to many more powerful ways of doing things, centralized management, and security model.
However, there are use cases when you may want to configure Windows Server 2016 or Windows Server 2019 in a workgroup and utilize remote desktop services.
One of the strongest use cases I can think of is in an edge environment where you may not have the infrastructure setup to run a full Active Directory environment, yet still need to provide more than two connections to an application server, perhaps running a legacy application.
Another use case may be for a simple jumpbox that is used to monitor hardware or perform other low-level duties that do not require the server to be joined to an Active Directory domain.
While AD is more powerful, it is also more to maintain and takes more resources to spin up. It also requires the technical expertise to configure, manage, and troubleshoot.
Workgroup configurations by contrast, are fairly simple. Everything is contained on the same box, including the user accounts you authenticate with. So, as mentioned for certain environments, I can see this as a potential use case for this type of configuration.
Windows Remote Desktop Services and Licensing in a Workgroup
First, let’s setup the basics to connect to a single Windows Server 2019 server that is running Remote Desktop Services (RDS) for user connectivity. Launch Server Manager and install the Remote Desktop Services role.
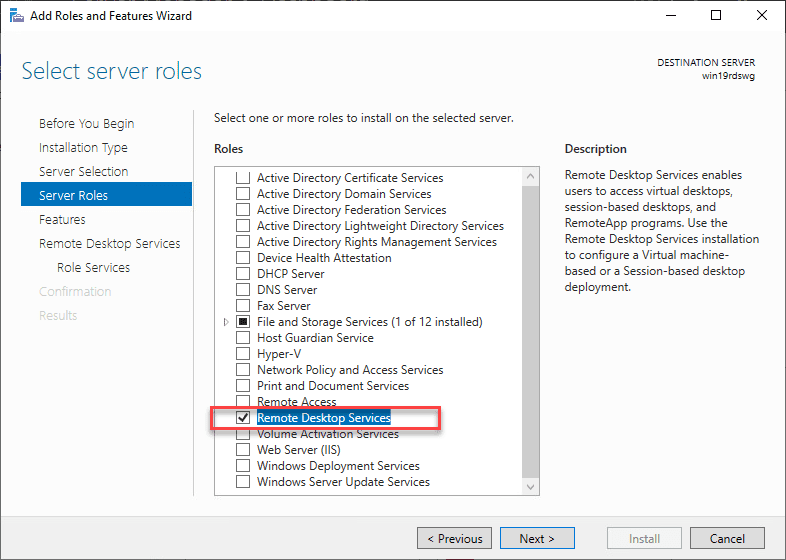
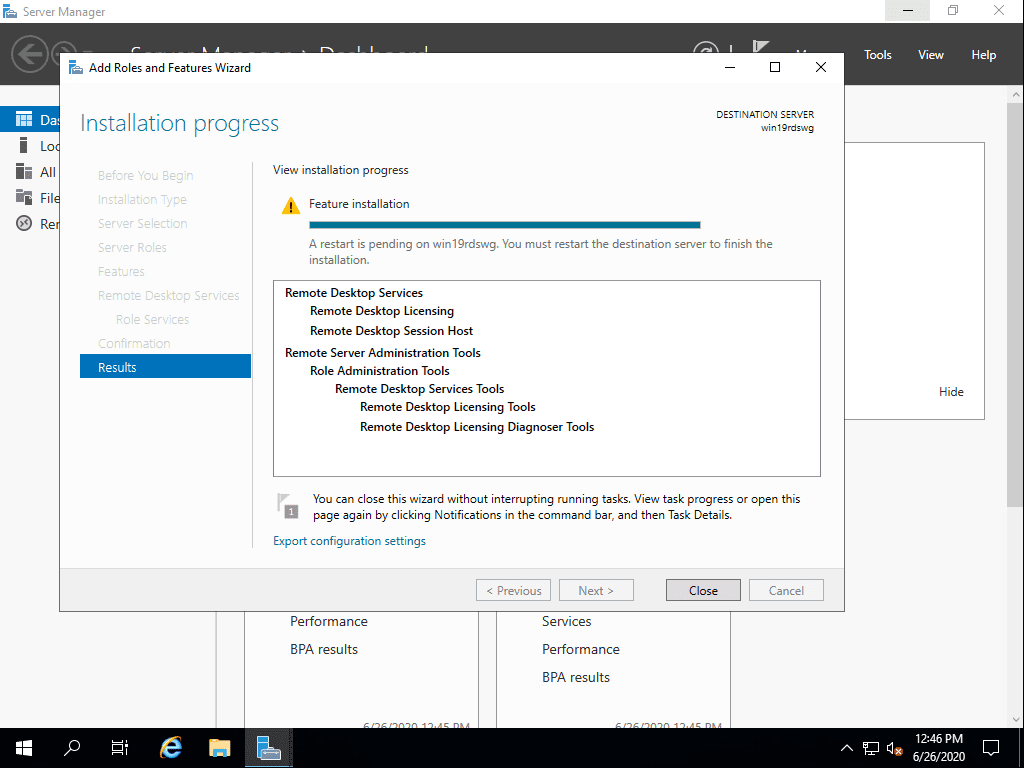
Select the Role Services that will be installed with the role installation. For a simple Windows Server 2019 remote desktop services without domain installation, you simply need to add the Remote Desktop Licensing and Remote Desktop Session Host role services.

After installation, you will need to reboot your server to finish the role installation.
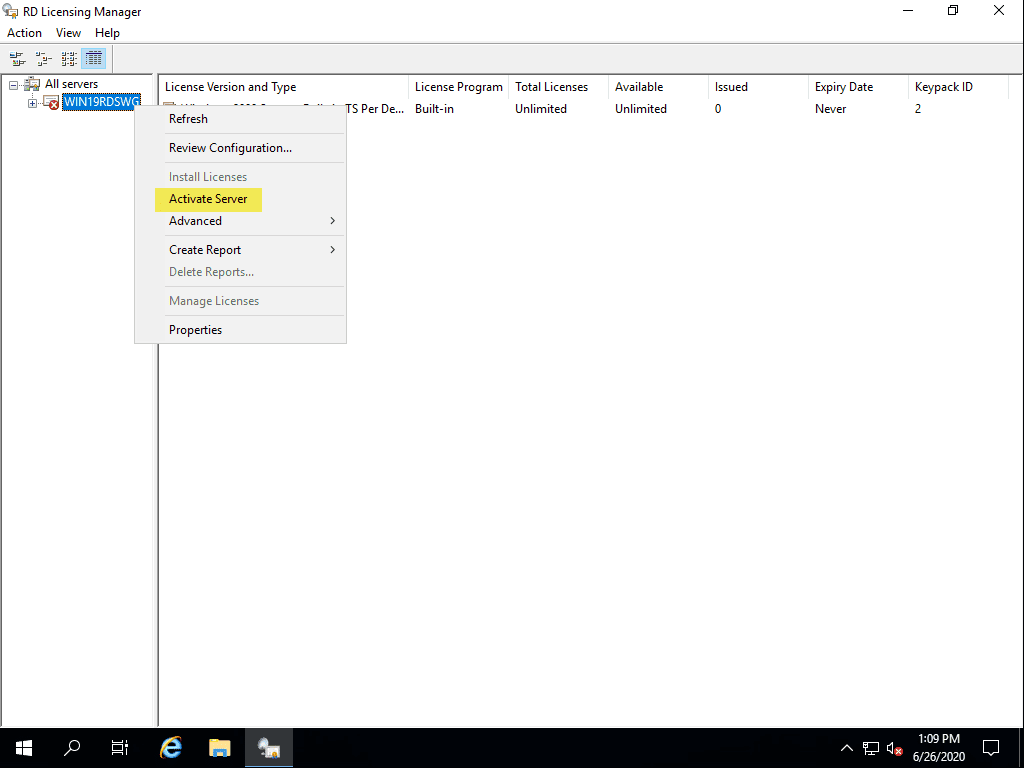
After reboot, you can activate your Remote Desktop Licensing. Launch the RD Licensing Manager console and right-click on your server and select Activate Server.
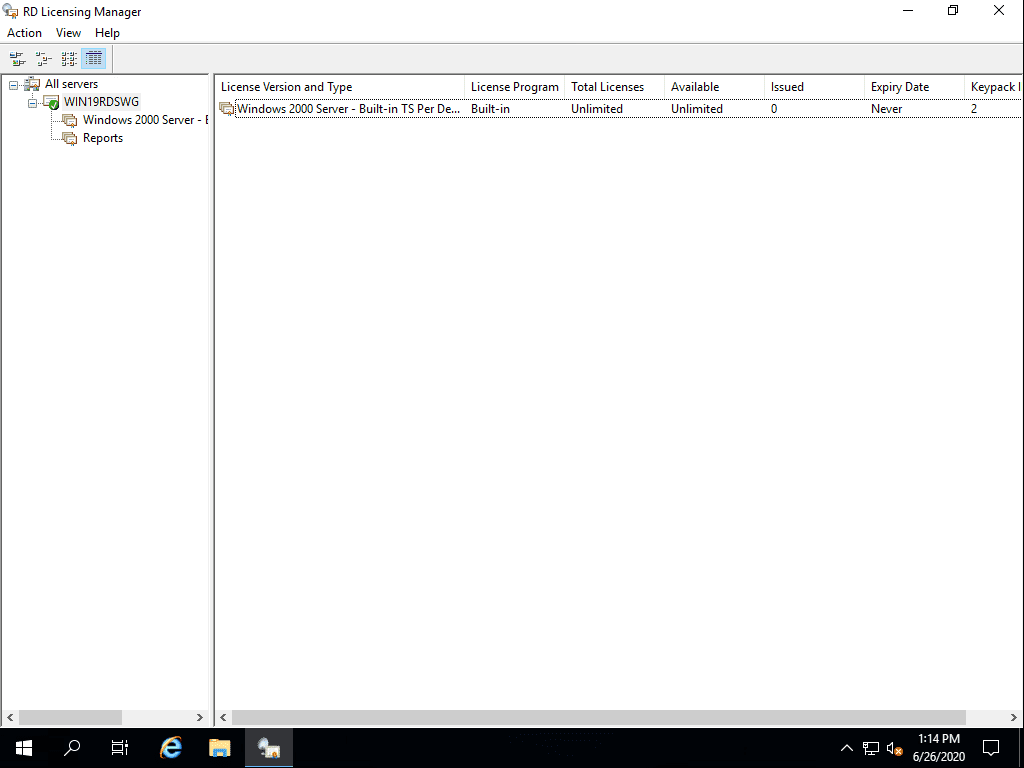
After you go through the wizard to install your licensing, you should see your server activated. Note, below, I haven’t added any additional licensing for the demo.
Now, create your local user(s) that will be used to connect to the Windows Server 2019 Workgroup remote desktop services server.
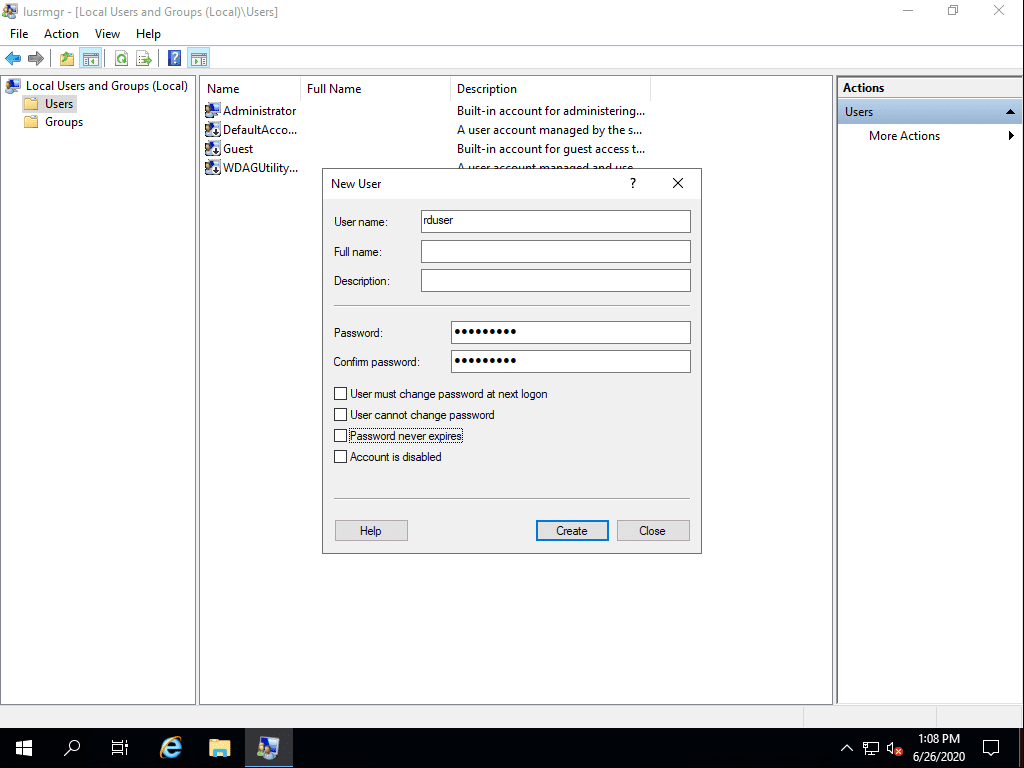
Add this user or multiple users you have created into the Remote Desktop Users group which allows the local user to remote desktop into the Windows Server 2019 remote desktop services server.
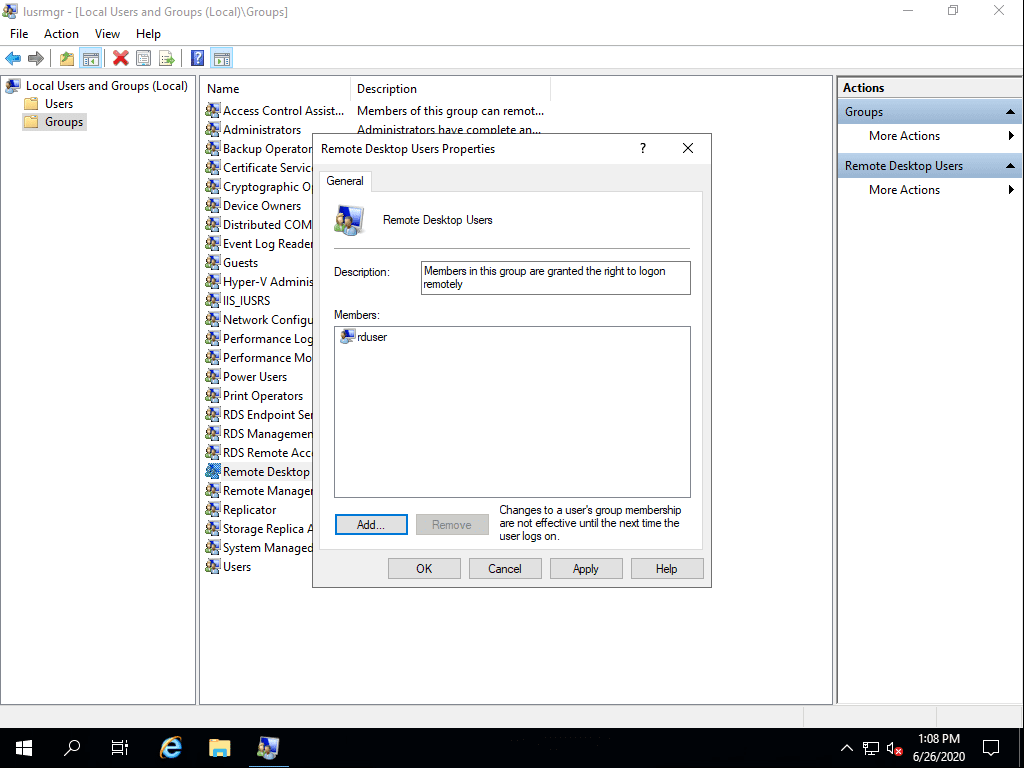
At this point, you will have a functional remote desktop session host that multiple remote users will be able to remote into to run applications or use as a jump host.
Remote Desktop Services Gateway without Domain
We all know that placing an RDP server in the DMZ or forward facing to the Internet is a dangerous thing to do. Microsoft’s RDP implementation has been historically riddled with security vulnerabilities. If not properly patched it can easily lead to data breach or ransomware infection in your environment.
Using a Remote Desktop Gateway server strengthens your security since it allows a secure tunnel over SSL 443 to your RDP endpoint. This allows one of your remote workers coming across the Internet to securely tunnel to their RDP server over port 443 without exposing RDP to the outside world.
Can this be setup on a workgroup server? Yes. Also, you can do this on the same workgroup server, pretty cool! By installing on the same server as is the target of the RDP connections, you can simply open up port 443 to the outside and use the same address for the gateway as you do for the target of the RDP connection.
Simply go back on the same server and Add Role services. Add the Remote Desktop Gateway role service to your installation. It does not require a reboot.
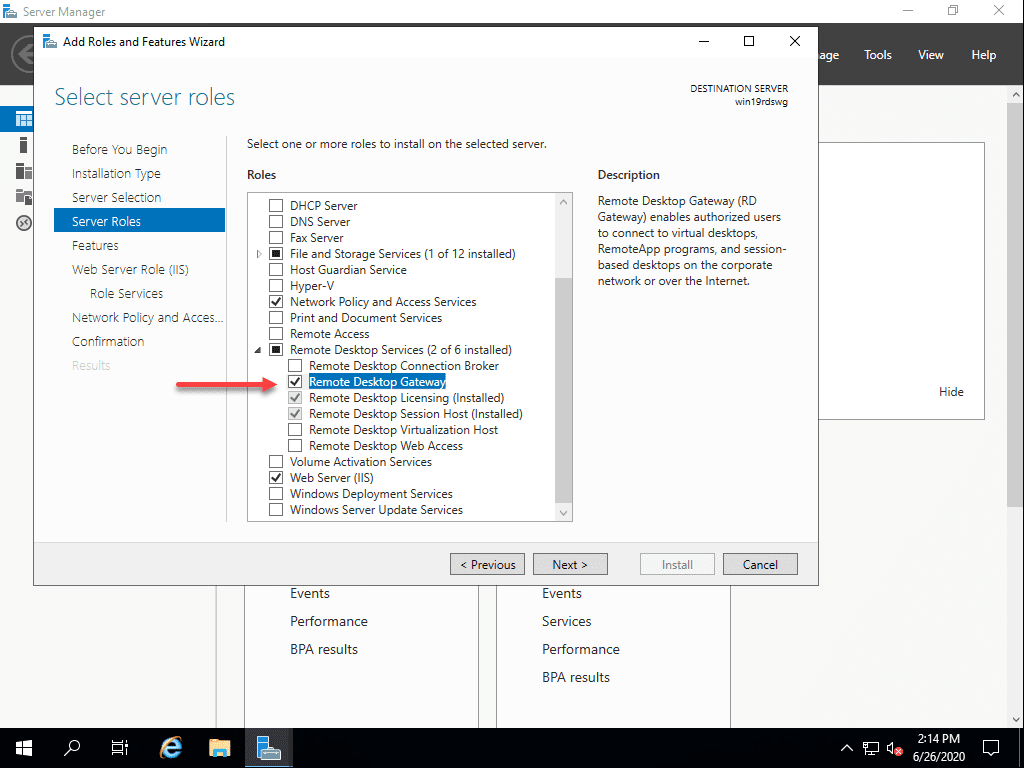
After installing the role service, launch the RD Gateway Manager console and create both the Connection Authorization Policy and the Resource Authorization Policy.
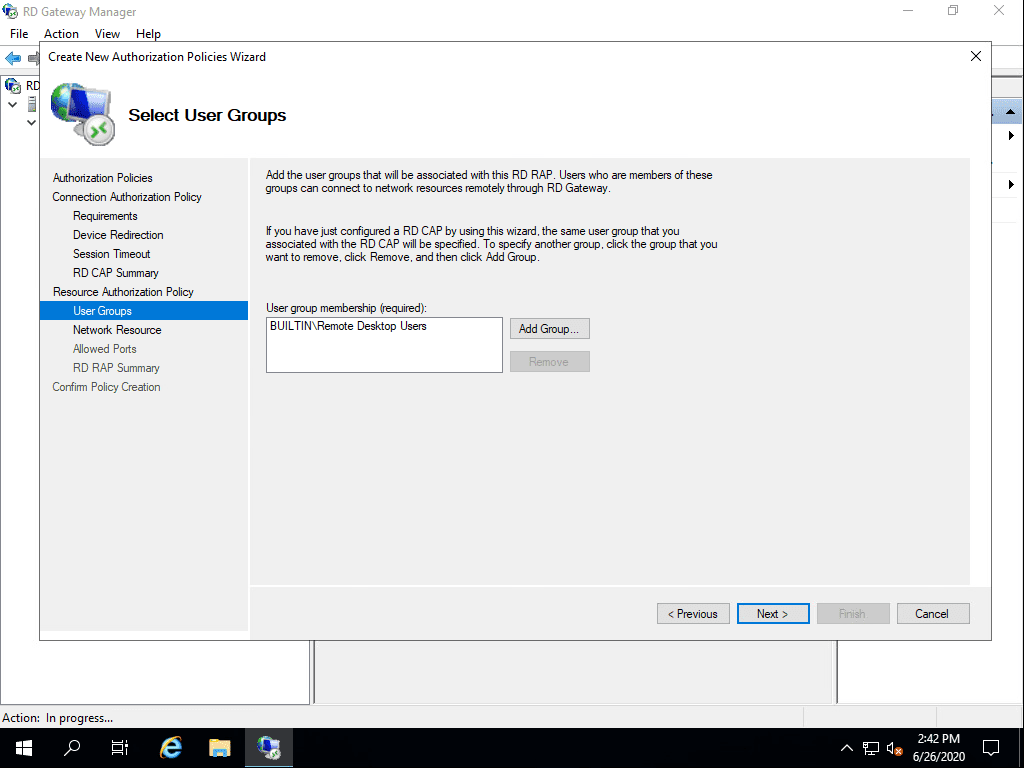
You can easily use the wizard to create both at the same time. Basically, in a workgroup configuration, you can simply add the BUILTINRemote Desktop Users group to the RD CAP and the RD RAP.
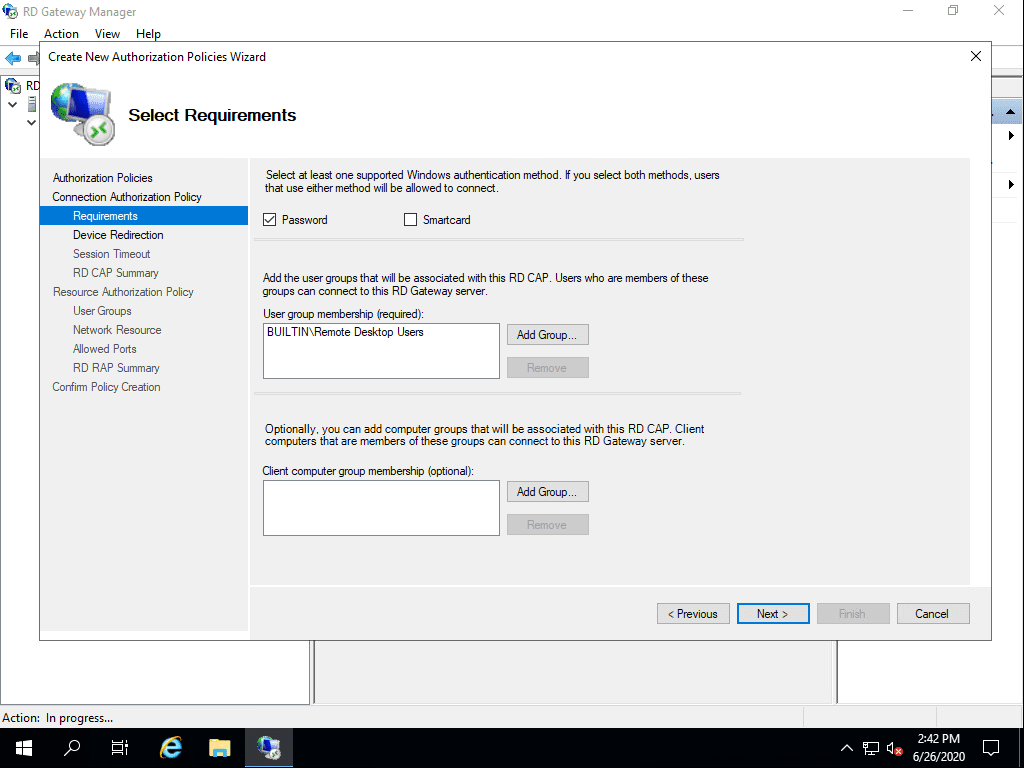
Adding the group in the RAP as well.
Now, configure your self-signed certificate for your Windows Server 2019 remote desktop services without domain box. Right-click on the server. Under SSL Certificate, use the Create a self-signed certificate button.
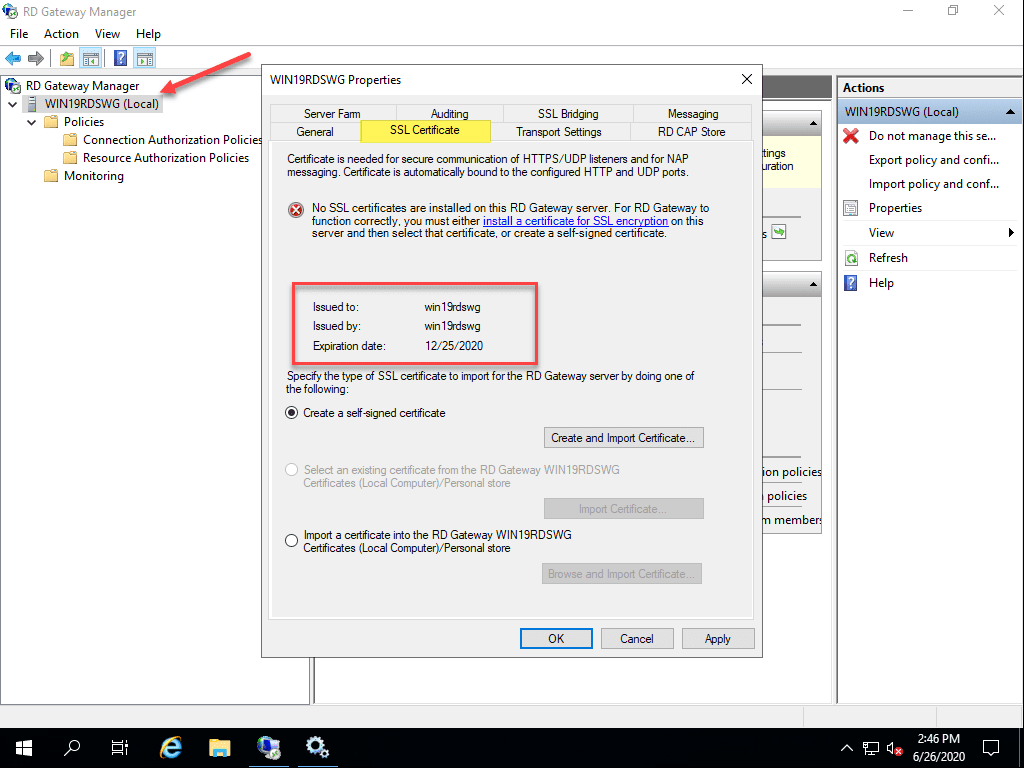
If this is just going to be a standalone server that only a couple or more users will be connecting to, you can get away with the self-signed certificate. However, keep in mind, you will have to import the certificate on the client workstations that will be connecting to the RD Gateway Server.

Thoughts
There are several use cases that may call for using a Windows Server 2019 remote desktop services no domain configuration where the server is in a workgroup and not domain joined.
This can help to simply a configuration to some degree in a remote location or edge environment that may lack a connection back to a central Active Directory database.
Using the workgroup configuration you can setup a remote desktop services box and a remote desktop gateway server all on the same server. By doing this, you will be able to expose only SSL 443 to the outside world for end users to make connections.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.




Do we need CALs to use RDP LAtter in future? Things mentioned above worked for me perfectly .
But do I need to buy CALs in future ?or I can do unlimited RDP sessions?
Yes you need a CALs license for RDP sessions, for users, or for devices, it is up to you, which one you are going to select, as well as you, can choose CALs for 25/50/ and more users
Shahzad,
Thank you for your comment and definitely good to keep licensing in mind with RDS solutions!
Brandon
Hi Brandon,
Well written!
Just a small note about device/user CALLs
When RDP server is installed without local AD, user CALLs licenses will not work.
For that you’ll need per device CALLs.
The wrong license model will end in Temporary RDS Connections.
CALL it Right,
Thank you for your comment. Great note as well on the user/device CALs. Licensing is always a critical aspect of spinning up RDS infrastructure.
Brandon
Hi Brandon. I am setting up a standalone server 2019 for RDP without a domain or AD, I have followed your excellent guide and I can connect to the server however I get a message that the session will be disconnected in 60 minutes because of a RDP license issue (no explanation). I’m also faced with the limitations of not being on a domain where use of the licensing diagnostic isn’t supported, I get the “you are logged in as a local administrator, you must be logged in as a domain user to manage servers and collections”. I have tried setting the licensing mode to overcome this limitation but in this instance it hasn’t worked. If you, or somebody you can recommend, could walk me through this configuration I would be happy to pay for a single incident support, it’s driving me a little crazy getting it to work without issues. I hope you can see my email address on the back-end of this message system. Thanks in advance for your consideration!
Fred,
Thank you for your comment. Were you able to make it past your issue? I found a couple of links here that may be helpful with a workgroup configuration. Take a look here and see if these are helpful and let me know: https://learn.microsoft.com/en-us/answers/questions/1183875/how-to-install-rds-in-workgroup-or-without-domain
Brandon