Recently, I added a cool piece of networking gear to the home lab environment – a Palo Alo PA-220 next generation firewall. I have always been a fan of Palo Alto firewalls as the integration and nextgen capabilities they offer are some of the best out there. I will be writing up a detailed initial configuration and setup post soon, so look for that in the next few days. The focus of this post, using the PA-220, is to show how to setup a TAP or mirror port on a switch for use with the TAP functionality in Palo Alto. What is a TAP or mirror port? What is it used for and what are the considerations when creating the port mirror/TAP. Let’s take a look at how to Monitor Network Traffic with Port Mirror and TAP Port with Palo Alto.
What is a Mirror or TAP port?
A mirror or TAP port as it is called allows “mirroring” the traffic on one port over to the other port of your choosing. This allows you to take a device and “see” all the network traffic on one port using another port. This comes in handy when you want to use another device like a Palo Alto to have a second set of “eyes” so to speak on network traffic to identify any risks on the network perhaps at the gateway level. Often this is used when testing a new firewall appliance. The new firewall (Palo in this case) is placed on a mirrored port and is able to see what if any malicious or application specific traffic is leaking through another vendor’s solution perhaps.
Configuring a Mirror or TAP port
Creating a mirror or TAP port on a switch is pretty similar across vendors, however, make sure to follow your vendor specific documentation when you go about configuring your mirrored port on the switch. In my home lab, I am using a Cisco SG300-20 switch as my network core, so the screenshots are related to this specific device. Again, most are similar to this and usually provide a way to configure the mirrored port via the GUI as well as the CLI. Here I will simply show the GUI configuration of the port. Note below, I have already created the mirror configuration, so it is already listed.
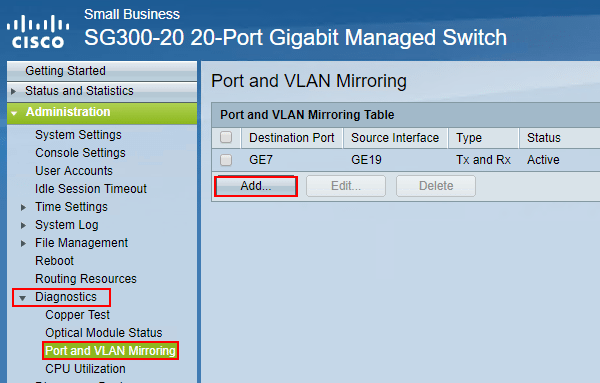
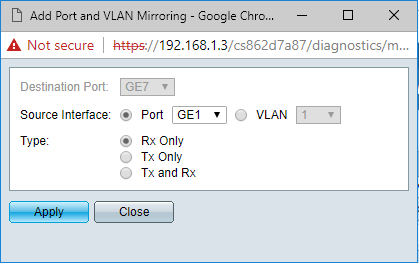
As mentioned, I have the mirror created, but in the Cisco web GUI, it is as simple as selecting the destination port and the source interface for the mirror. You also have the choice to mirror certain aspects of traffic or all traffic such as Rx Only, Tx Only, or both Tx and Rx. For the most visibility, choose to mirror Tx and Rx.
For the most part, this is all there is to creating a mirror port. However, there are a few things to note with mirror ports.
- They are special purpose only and do not carry network traffic of their own
- The port cannot be configured to be a member of any user created VLANs
- At least the SG300 you receive an error if the port is a member of any VLAN besides VLAN 1
Monitor Network Traffic with Port Mirror and TAP Port with Palo Alto
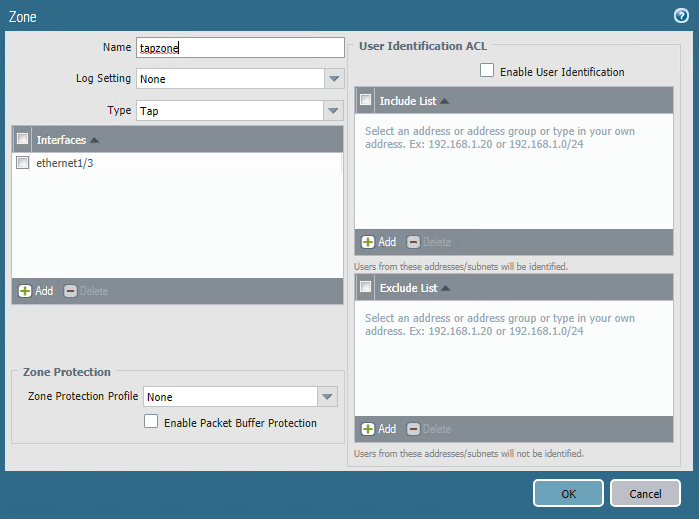
In order to monitor network traffic using the Palo Alto firewall, you need to create the mirrored port. There are just a few steps needed to configure a TAP port on a Palo Alto device. The first thing you need to do is create a TAP zone. Click the Network tab and then click Zones Create the named zone and select Tap for the Type.
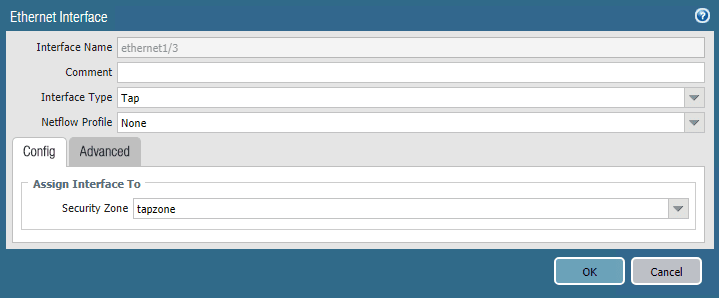
Next, configure a Palo Alto interface as a Tap interface type. Go to Network >> Interfaces to configure this.
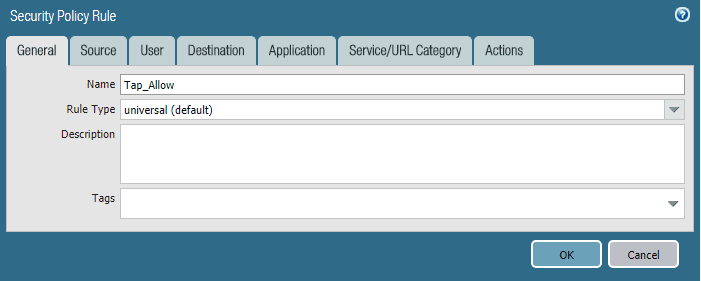
Finally, create a new Security Policy for the TAP interface. Basically, it is an any/any/any/any allow rule. The Rule Type can stay as universal.
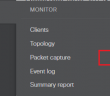
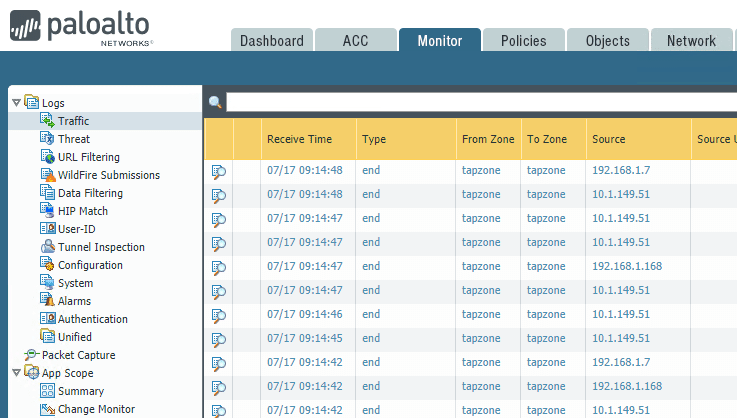
The Monitor >> Traffic area will start displaying traffic information that is coming across the mirrored port. In this case, it is a mirrored port with my current firewall that is in home lab production.
Palo Alto has a good walk through of the process in their official documentation – https://live.paloaltonetworks.com/t5/Configuration-Articles/How-to-Configure-a-Palo-Alto-Networks-Device-for-Tap-Mode/ta-p/59438
Takeaways
The ability to Monitor Network Traffic with Port Mirror and TAP Port with Palo Alto demonstrates how you can create a mirrored network port that duplicates all network traffic from a single network port over to another network port on a switch that supports port mirroring. This effectively allows a device sitting on the mirrored port to see all the network traffic that are traversing the source port. This is a great way to gain visibility for security purposes or to audit current network firewall capabilities or firewall rules. Using the Palo Alto firewall to listen to traffic on the mirrored port allows Palo to audit the threats coming across current gateways. Stay tuned for future posts with my experiences using the Palo Alto PA-220 in my home lab configuration.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.