Ansible is a well-known configuration management solution that can be used for automating many different things. One thing you can do very well with Ansible is using it for updates and software patching. Let’s see how.
Table of contents
Setting up Ansible patching
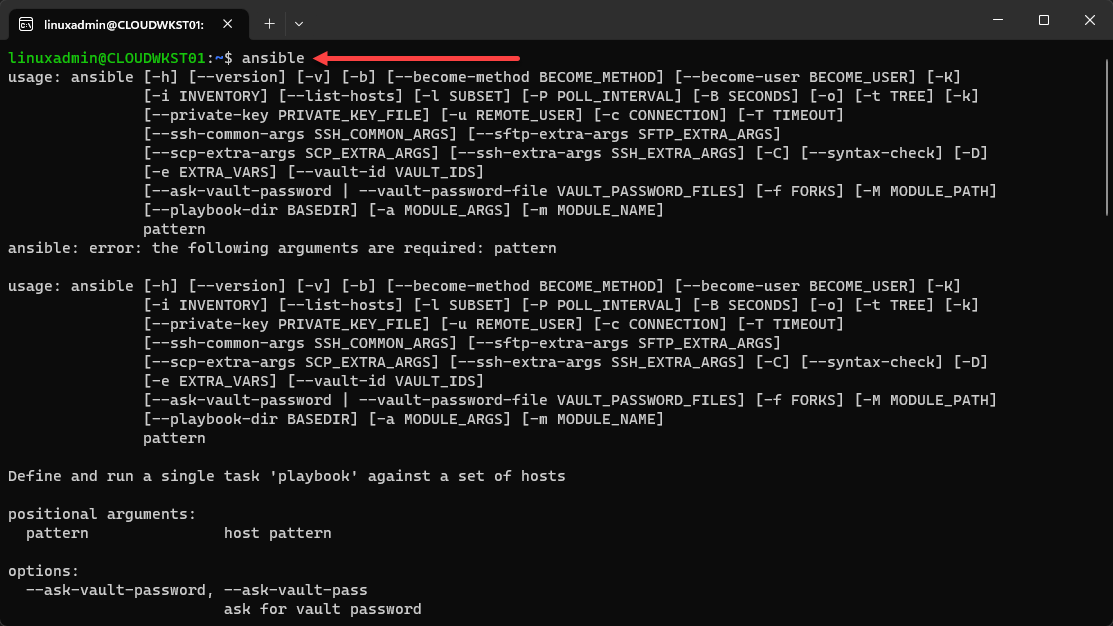
Before diving into Ansible software patching, setting up your environment is important. You’ll need to have Ansible installed, along with access to your Linux servers and the necessary packages.
Installing Ansible on Ubuntu
Before you can use Ansible for patching, you’ll need to install it on your system. If you’re using Ubuntu, follow these steps to install Ansible:
Update the package list and install required dependencies:
sudo apt-get update sudo apt-get install software-properties-commonAdd the Ansible repository to your system:
sudo apt-add-repository --yes --update ppa:ansible/ansibleInstall Ansible:
sudo apt-get install ansibleNow that Ansible is installed on your Ubuntu system, you can create playbooks for patching.
Basic Ansible Software Patching Code for Linux and Windows
To demonstrate basic Ansible software patching, we’ll create two simple playbooks: one for Linux and one for Windows. These can be executed as shell scripts using Ansible open-source tool.
For Linux (using the apt module):
---
- name: Update Linux packages using apt
hosts: debian_servers
become: yes
tasks:
- name: Update package cache
apt:
update_cache: yes
cache_valid_time: 3600
- name: Upgrade all packages to their latest version
apt:
name: '*'
state: latest
force_apt_get: yes
- name: Reboot the server if necessary
reboot:
test_command: uptime
reboot_timeout: 300For Linux (using the Yum module):
---
- name: Update Linux packages
hosts: linux_servers
become: yes
tasks:
- name: Update all packages
yum:
name: '*'
state: latest
- name: Reboot the server if necessary
reboot:
test_command: uptime
reboot_timeout: 300For Windows (using the Win_updates module):
---
- name: Update Windows packages
hosts: windows_servers
tasks:
- name: Install all updates
win_updates:
category_names: ['CriticalUpdates', 'SecurityUpdates', 'UpdateRollups']
state: installed
- name: Reboot the server if necessary
win_reboot:
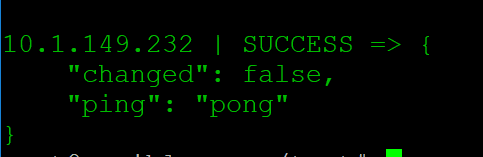
reboot_timeout: 300These playbooks will update packages on your Linux and Windows systems, and reboot the servers if required. To run the playbooks, save them as separate files (e.g., patch_linux.yml and patch_windows.yml) and execute the following commands:
ansible-playbook -i inventory.ini patch_linux.yml ansible-playbook -i inventory.ini patch_windows.ymlMake sure to replace inventory.ini with your inventory file that lists your Linux and Windows servers.
Ansible Software Patching FAQs
Make sure of update and patching windows
You can schedule your Ansible playbooks to run at set times tool like cron for Linux or Task Scheduler for Windows or you can use something like Ansible Semaphore. Here’s an example of a cron entry that runs a playbook at 2 AM every Sunday:
0 2 0 /usr/bin/ansible-playbook -i /path/to/inventory.ini /path/to/patch_playbook.ymlRemember to replace the paths with the actual locations of your inventory file and patch playbook.
Make sure of update status
Gathering info about installed packages and their versions can help you verify that your systems are up-to-date. For example, on a Linux system using the apt module, you could use the following task:
- name: Get the list of installed packages and their versions
apt:
list: installed
register: apt_packagesThen, you can use the debug module to display the list of installed packages and their versions:
- name: Display installed packages and their versions
debug:
var: apt_packages.stdout_linesCan I use Ansible to apply patches only to specific systems or packages?
Yes, you can use Ansible to patch specific systems or packages selectively. To target specific systems, you can define groups in your inventory file and then specify the group name in the hosts field of your playbook. For example:
[web_servers]
web1.example.com
web2.example.comIn your playbook, use hosts: web_servers to apply the patch only to the systems in the web_servers group.
To apply patches only to specific packages, you can modify the name parameter in the appropriate Ansible module (e.g., yum, apt, or win_updates). For instance, using the apt module, you could update only the ‘nginx’ package by setting name: nginx:
- name: Update the nginx package
apt:
name: nginx
state: latest
force_apt_get: yesWrapping up
Ansible software patching is a great way to keep your critical systems or home lab servers up-to-date. It streamlines this process and takes the possibilities of errors or just simply missing things out of the question. It is a great skill and tool to learn.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.