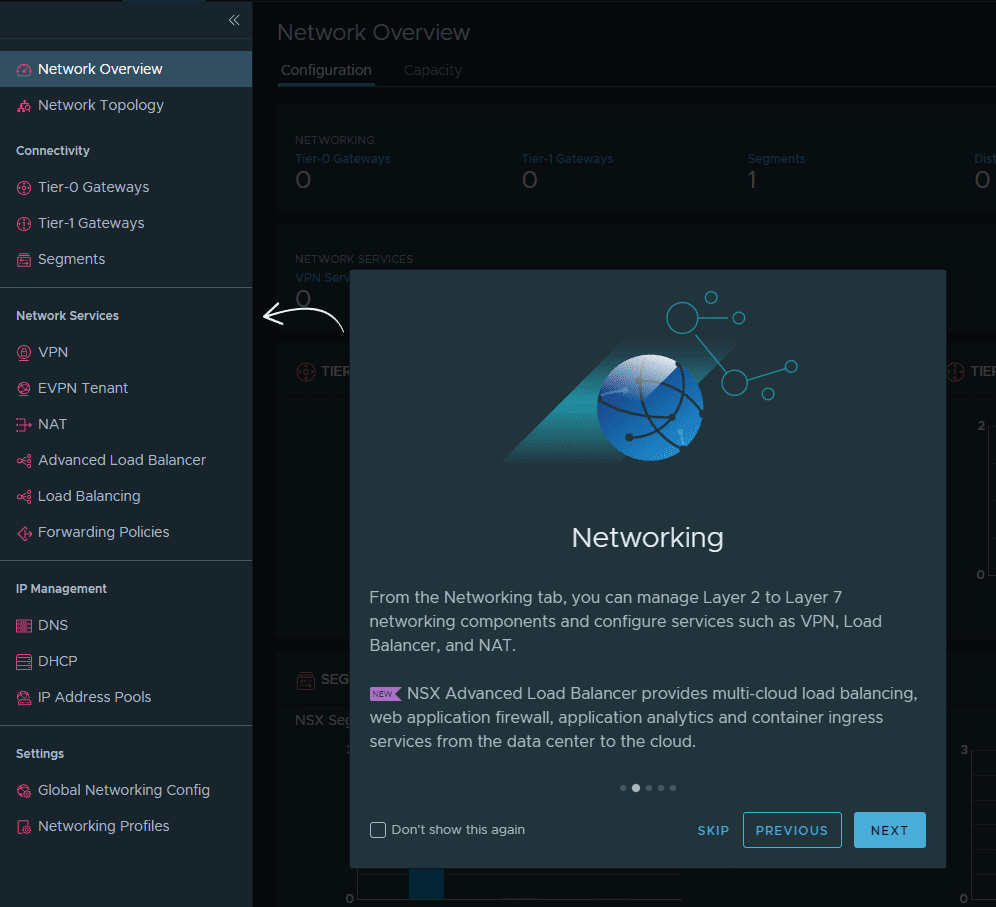
VMware NSX provides powerful insight into network traffic and it allows administrators to handle traffic based on very powerful criteria, including the user that is logged into a resource. Now in VMware NSX 6.4, this insight has even been turned up a notch with the identity firewall. It can now distinguish between various network flows and the users that are behind those network flows. This provides some really interesting use cases such as being able to correctly implement microsegmentation on an RDSH server. One of the mechanisms behind the powerful network abilities provided by VMware NSX is called guest introspection. What is VMware NSX guest introspection and how is it configured? What are some of the requirements of the new capabilities with the identity firewall?
What is VMware NSX Guest Introspection and how is it configured?
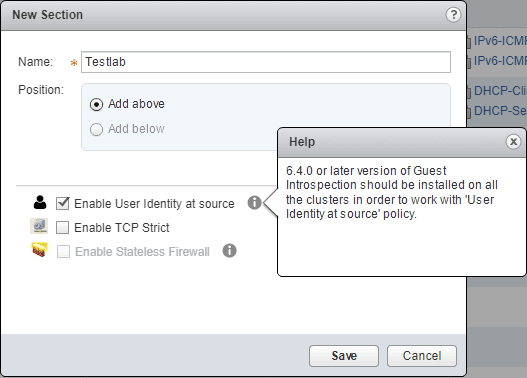
In general, VMware NSX Guest Introspection offloads antivirus and anti-malware agent processing to a dedicated secure virtual appliance that is configured when Guest Introspection service is enabled at the cluster level. However, it is also required when enabling the “identity at source” firewall functionality of the identity firewall.
The process to install the Guest Introspection service on an ESXi cluster involves the following:
- Installing Guest Introspection on Host Clusters
- Installing the Guest Introspection Thin agent on Windows Virtual Machines
- Additionally, if using Linux Virtual Machines, installing the guest introspection thin agent on Linux Virtual Machines.
- The thin agent plays the role of detective and allows detecting the logon user id and IP address of the logon session coming from the user ID in question that we want to build the firewall policy around. This information is relayed to the NSX manager.
This is accomplished with guest introspection infrastructure. After the user logs in, VMware Tools Guest Introspection sees the login and sends the IP and user ID to the Service Virtual Machine (SVM). The SVM updates the NSX Manager with the IP and user ID details as well as the directory groups the user is a member of. The NSX Manager then applies the correct firewall policy based on these details.
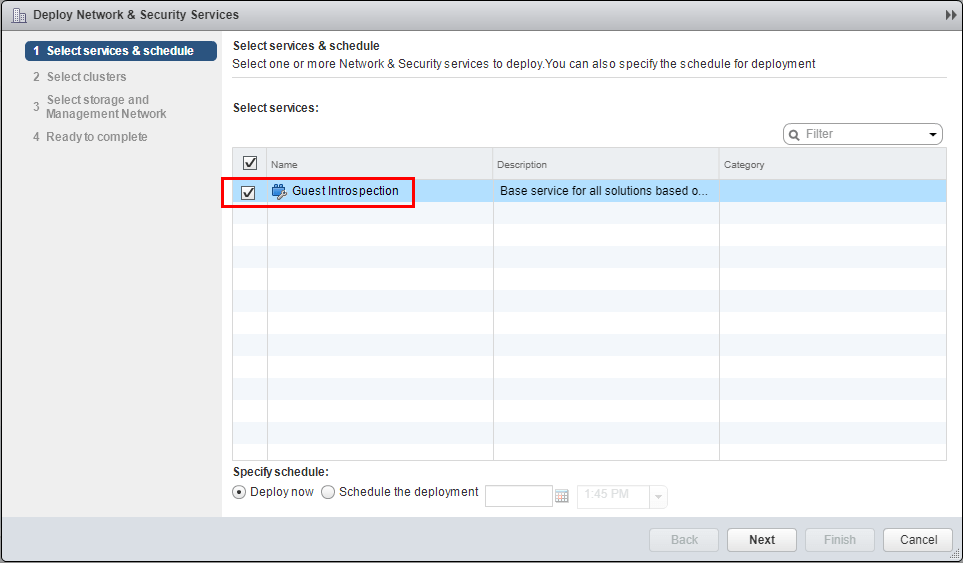
To begin the installation of the guest introspection service deployment, navigate to Installation and Upgrade >> Service Deployments and click the green “+” sign.
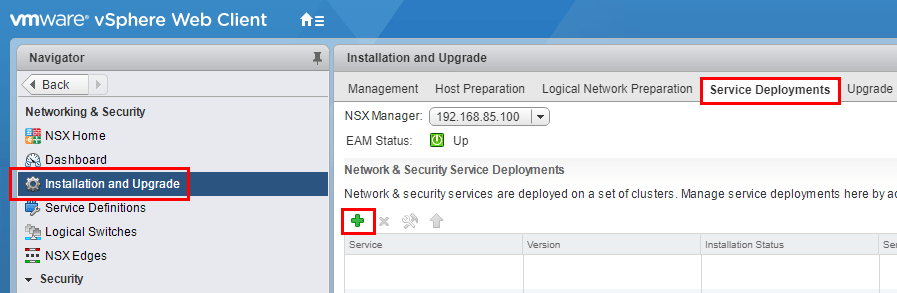
Select the Guest Introspection option.
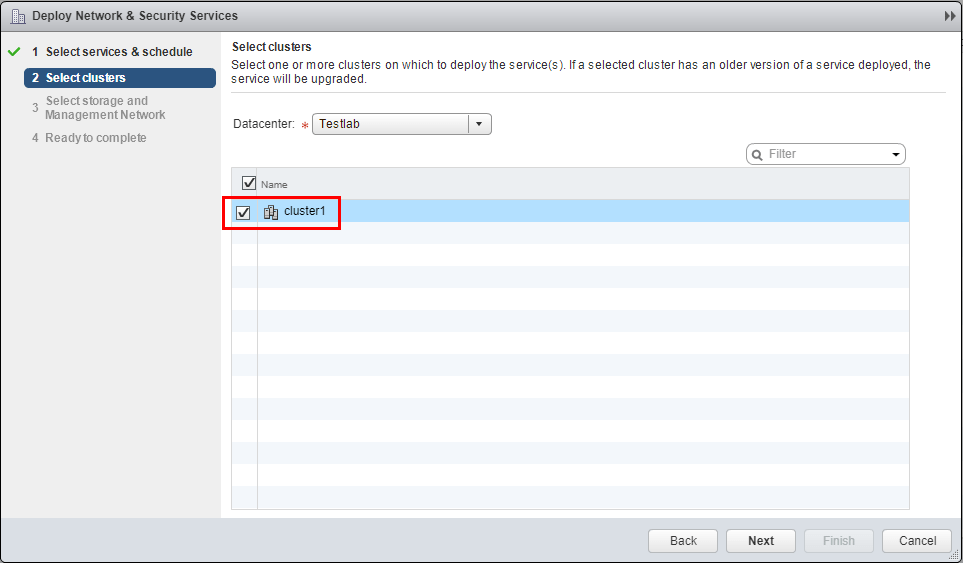
Next, we select the cluster name of the cluster for which we want to enable the guest introspection service.
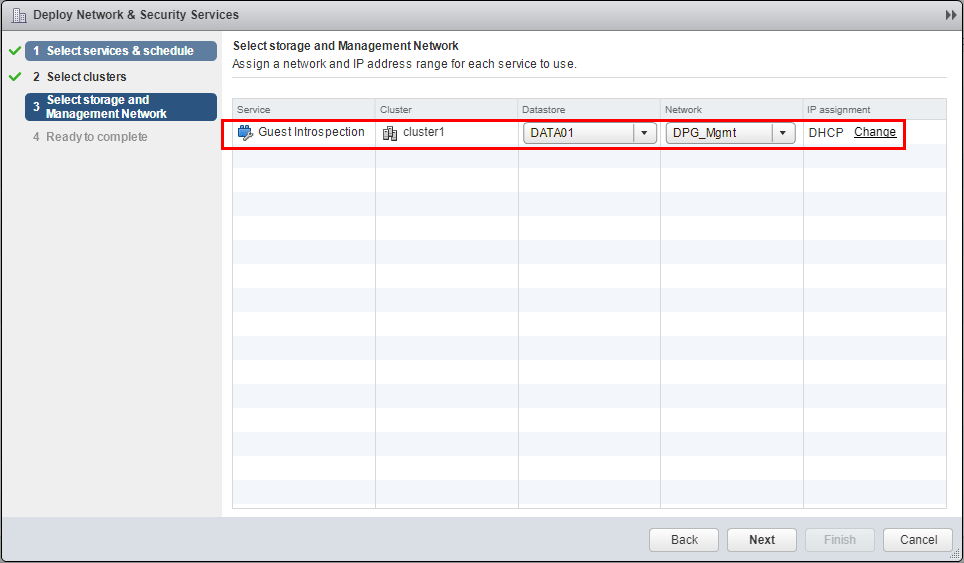
We need to select storage and management network configuration for the SVM virtual machines that will be created to enable the guest introspection service.
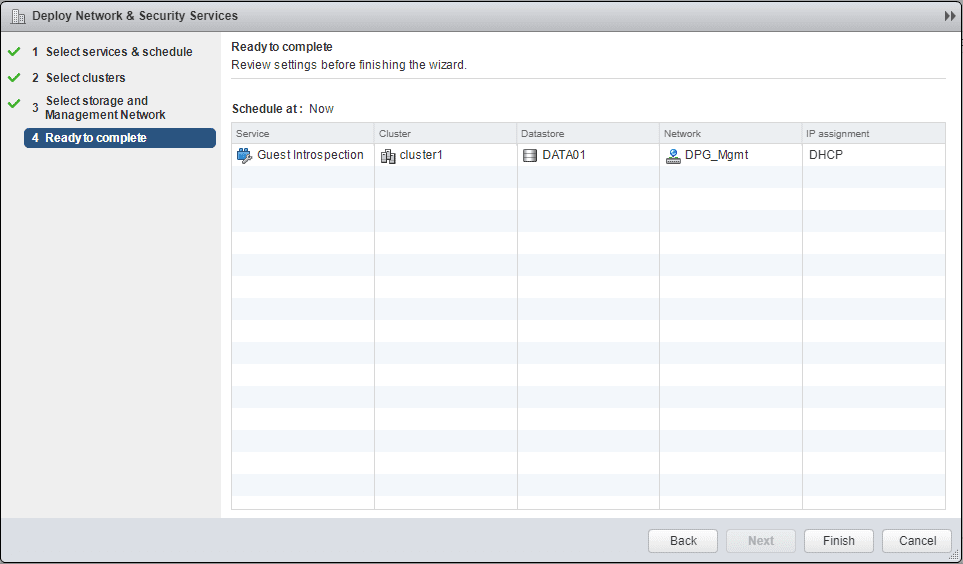
Finally, review the options for the guest introspection service deployment.
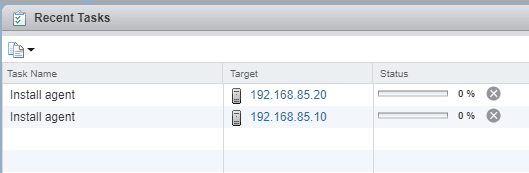
We will note several tasks that begin kicking off. The Install agent task will begin on both hosts.
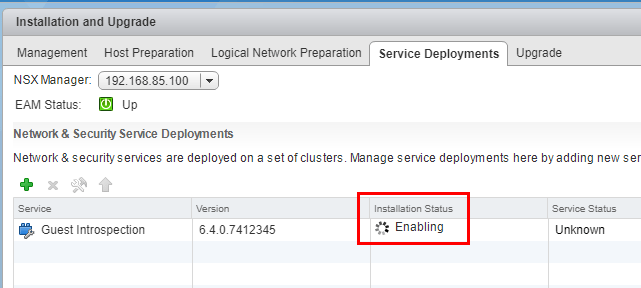
In the Installation Status you will see the Enabling status listed while the service is deployed.
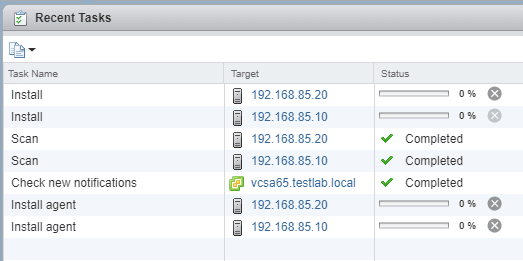
Installation continues…
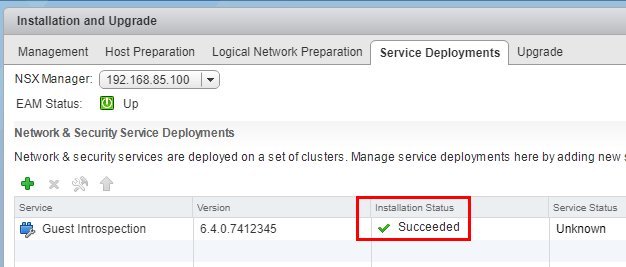
After a couple of minutes, the Guest Introspection installation will show as Succeeded.
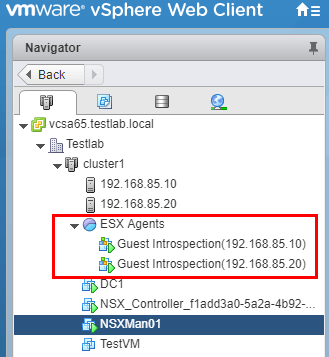
The special SVM virtual machine (security virtual machines) are created for every host in the cluster.
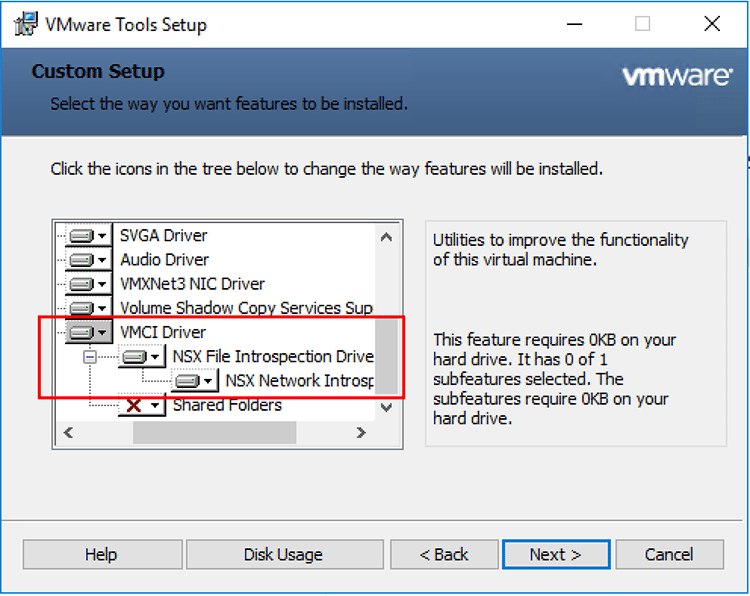
In addition to installing the guest introspection service deployment on the vSphere ESXi cluster, we also need to make sure the guest introspection services are enabled within the virtual machines we want to work with guest introspection. This is part of the VMware Tools package and is an option that needs to be configured as it is not turned on by default. If VMware Tools is already install, we can modify the installation and include the VMCI Driver including the NSX File Introspection Driver and NSX Network Introspection Driver.
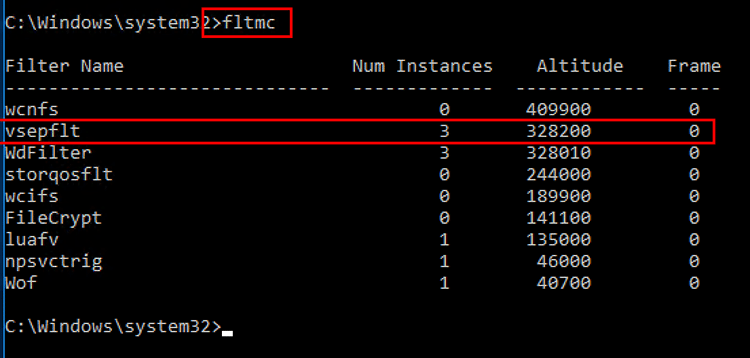
You can verify the driver is loaded by typing fltmc at an administrator command prompt. You should be able to see the vsepflt filter driver loaded.
Concluding Thoughts
The guest introspection service is an extremely important service that allows special insight into the network flows and other functionality of a virtual machine. Hopefully this post – What is VMware NSX Guest Introspection and how is it configured? will help any who may have wondered what the service is and what it is used for. The new NSX 6.4 identity firewall features depend on the guest introspection services running.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.