Businesses today are making the most of what the cloud has to offer. Arguably, the businesses who are not using cloud SaaS for at least some function in their organization are few and far between. Cloud adoption has been accelerated over the past couple of years due to the tremendous shift to a hybrid workforce. Microsofts M365 environment has seen a tremendous uptick in adoption, especially due to Microsoft Teams. In addition to Teams, Microsoft 365 customers can take advantage of the myriad of apps available in the marketplace of cloud SaaS apps. Third-party cloud SaaS apps are a double-edged sword that can expose businesses to tremendous risk due to the risk of ransomware, data leak, and other threats. Spin Technology has announced a new SpinOne Risk Assessment for Office 365. What is it?
What danger is posed by third-party cloud SaaS apps?
First of all, is there a risk associated with cloud SaaS apps? One of the big features of cloud SaaS environments is the ability for organizations to take advantage of cloud SaaS applications available in the various cloud marketplaces. For Microsoft Office 365 environments, this is the Microsoft AppSource marketplace.
On the Microsoft AppSource, you will find a proverbial buffet of apps available for consumption in the environment. These include a wide range of apps allowing businesses to enhance or extend the features, capabilities, and functionality of an Office 365/Microsoft 365 environment. The wide selection of cloud-based apps helps businesses get the most out of the capabilities in the cloud.
However, when businesses open their walls to third-party applications, it can introduce many risks to the environment. What are these?
- Malicious apps
- Shadow IT
- Data Leak
- Compliance violations
Malicious apps
By allowing third-party applications in the environment, there is the risk of malicious apps being introduced in the environment. By default, users can install any third-party applications in Office 365. Users can install apps that may not be fully vetted from a security perspective. The apps may contain undesirable security issues. Also, attackers are increasingly looking at ways to compromise cloud environments as they realize these are increasingly used by businesses today.
Using a phishing email attack, cybercriminals may persuade users to click a malicious link that asks the user to grant cloud permissions to a malicious cloud SaaS app. The app may appear to be legitimate. However, once the app is integrated into the environment, it has full permission to act on behalf of the user installing the application.
Using OAuth permissions authorization can inadvertently grant malicious cloud SaaS apps the permissions needed to steal or encrypt data, leading to cloud ransomware variants already seen in the wild.
Shadow IT
Cloud SaaS apps can also lead to something known as Shadow IT. Shadow IT defines any software or other solutions not sanctioned or authorized by IT. Cloud SaaS third-party apps make carrying out shadow IT operations extremely easy due to the simplicity they can be installed and integrated into the cloud SaaS environment.
Due to the easy consumption model, a department or other business entity can simply provide a credit card in the marketplace portal and integrate cloud SaaS solutions into the environment without the consent of IT or SecOps.
Without the proper controls in place, users have free reign to install apps at their leisure. Businesses need to ensure they have the governance guardrails in place to restrict users’ ability to install apps outside the cybersecurity and other governance restrictions of the business.
Data Leak
Third-party apps may have “leaky” data. While they may not be all-out malicious, they may be written so that data gets inadvertently exposed. Due to compliance reasons, it may include sharing the data inappropriately or accessing data that shouldn’t be accessed by a third-party vendor.

Data leak issues are a huge problem for organizations that now have more stringent compliance requirements overall and compliance requirements that can lead to fines that are not insignificant (GPDR fines as a case in point).
Compliance violations
Compliance requirements are an essential consideration for businesses today that must meet a wide range of compliance regulations, including PCI-DSS, HIPAA, GDPR, and others. GDPR fines alone can amount to millions of dollars in fines with severe penalties.
Businesses must consider how apps meet regulatory compliance requirements when accessing data. Without vetting approved applications first, organizations are “rolling the dice” by allowing users to install apps freely.
New SpinOne Risk Assessment for Office 365
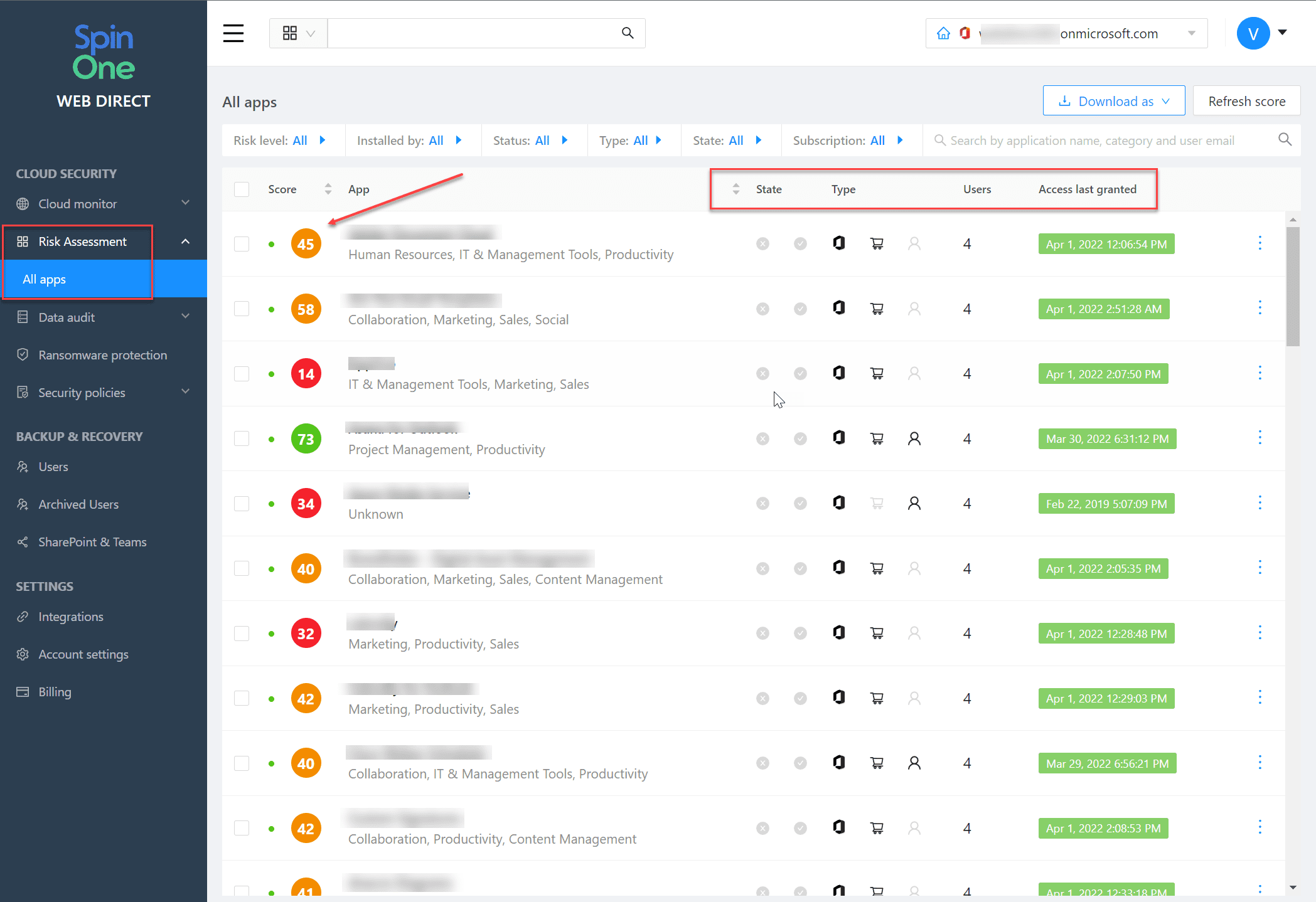
For organizations using Microsoft Office 365/M365, Spin Technology has announced a new Risk Assessment for Office 365. The new tool provides automated risk assessments for Office 365 environments to automatically provide a risk score for cloud SaaS apps in the Microsoft AppSource marketplace.
Scoring cloud SaaS apps is a huge undertaking performed manually and may require thousands of man-hours. However, SpinOne’s new risk assessment takes the heavy lifting out of the process. SpinOne’s new risk assessment for Office 365 automatically scores cloud SaaS apps based on several risk factors and continuously scores cloud SaaS apps. There is the chance that is trusted with one version may begin to display undesirable traits with future releases. SpinOne continues to score apps and adjusts the risk score accordingly.
In addition, you have the ability with SpinOne to create policies that allow or disallow cloud SaaS apps based on the risk score. These policies can be defined granularly, allowing businesses to decide which apps are allowed or disallowed for installation. Note the following features:
- See a list of apps with access to business-critical or sensitive SaaS data
- See which SaaS users have access to the application in the environment
- You can gain insights into the app’s usage, including when the Office 365 cloud SaaS app was last accessed and when the OAuth token was last used
- Run an assessment based on over twenty different categories, including factors related to possible business, security, or compliance risks for an app
- Have visibility to the full scope of permissions the cloud SaaS application requests upon installation
- Allow or Block specific cloud SaaS apps granularly, including for everyone in the organization or certain users/security groups
- View users who have access and are using the cloud SaaS app
- Interactive workflow for feedback on a specific cloud SaaS app’s risk assessment score
SpinOne Risk Assessment for Office 365 FAQs
- What is SpinOne Risk Assessment for Office 365? It is a new offering as part of SpinOne’s solution for Office 365/Microsoft 365, allowing customers to perform automated risk assessments of cloud-based and integrated apps using OAuth authentication.
- Can ransomware affect the cloud? Yes. There are several demonstrations in the wild of ransomware using cloud OAuth credentials to encrypt users’ files, emails, and other resources. It is becoming growing problem organizations must protect against.
- What is shadow IT? Shadow IT is the unsanctioned use of software, hardware, or cloud solutions without the consent or approval of IT or SecOps.
- How can cloud SaaS apps leak data? Cloud SaaS applications can inadvertently expose data to users who are not authorized to view the data or transmit the data in ways that do not align with compliance requirements for a business.
Wrapping Up
The new SpinOne risk assessment for Office 365 provides an effective way that organizations can ensure cloud SaaS apps do not introduce risk into their Microsoft cloud SaaS environment. It takes the heavy lifting out of performing risk assessments for individual cloud SaaS apps in the Microsoft Appsource marketplace and allows having an automated means to continuously evaluate the risk of cloud SaaS apps in the organization. It also allows creating policies to target different business units and allow or deny apps based on their risk score.
Learn more about SpinOne’s new risk assessment for Office 365 here: Microsoft Office 365 Data Protection Platform | Security & Privacy (spin.ai)
Read my other posts covering SpinOne solutions:
- SpinOne Salesforce Backup Announced – Features
- Office 365 Ransomware protection with SpinOne New Features
- Spin.ai cloud cybersecurity and ransomware protection new features
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.