Having the right tools to implement security and security best practices in your VMware vSphere environment is critical to a successful security posture. The recent release of Runecast 4.1 adds an additional powerful compliance check called the CIS Benchmark. What is this? Let’s take a look at CIS Critical Security Controls VMware scan with Runecast 4.1 and see how this new release helps you to align your vSphere environment with the CIS benchmark.
Why VMware Security is Important
Security couldn’t be a more relevant topic in today’s infrastructure. In fact, it seems like it becomes more and more important with each passing quarter and each passing year in IT and across the landscape of IT infrastructure. Especially, after the Spectre and Meltdown scare of 2018, hypervisors have been under even more scrutiny for side-channel type attacks as well as general security best practices.
More is simply at stake when it comes to hypervisors since multiple workloads are running on top of your hypervisor instead of just one. The “blast radius” is much larger with any kind of security compromise in a virtualized environment.
What is the CIS Benchmark?
CIS stands for Center for Internet Security. It is a nonprofit organization that sets out to identify, develop, validate, promote, and sustain best practice solutions for cyber defense. The CIS Benchmark is developed from the expertise of industry professionals including cyber security and IT pros from a wide range of industries.
The “Benchmarks” portion of the CIS Benchmarks include configuration baselines and best practices for securely configuring a system. Each of the recommendations point to one or more CIS controls to help improve overall cybersecurity defenses. The CIS controls in themselves map to well known security standards such as NIST, ISO 27000, PCI DSS, HIPAA, etC.
CIS CSC benchmarks provide two levels of security settings:
- Level 1 recommends essential basic security requirements that can be configured on any system and should cause little or no interruption of service or reduced functionality.
- Level 2 recommends security settings for environments requiring greater security that could result in some reduced functionality.
CIS Critical Security Controls VMware Scan with Runecast 4.1
With the latest release of Runecast, Runecast Analyzer 4.1, it now gives you the ability to flag on the CIS Benchmark as part of the compliance checks that are ran against your VMware vSphere environment.
This helps to give even more visibility to potential security issues found in your VMware vSphere environment based on the findings of the CIS benchmark framework.
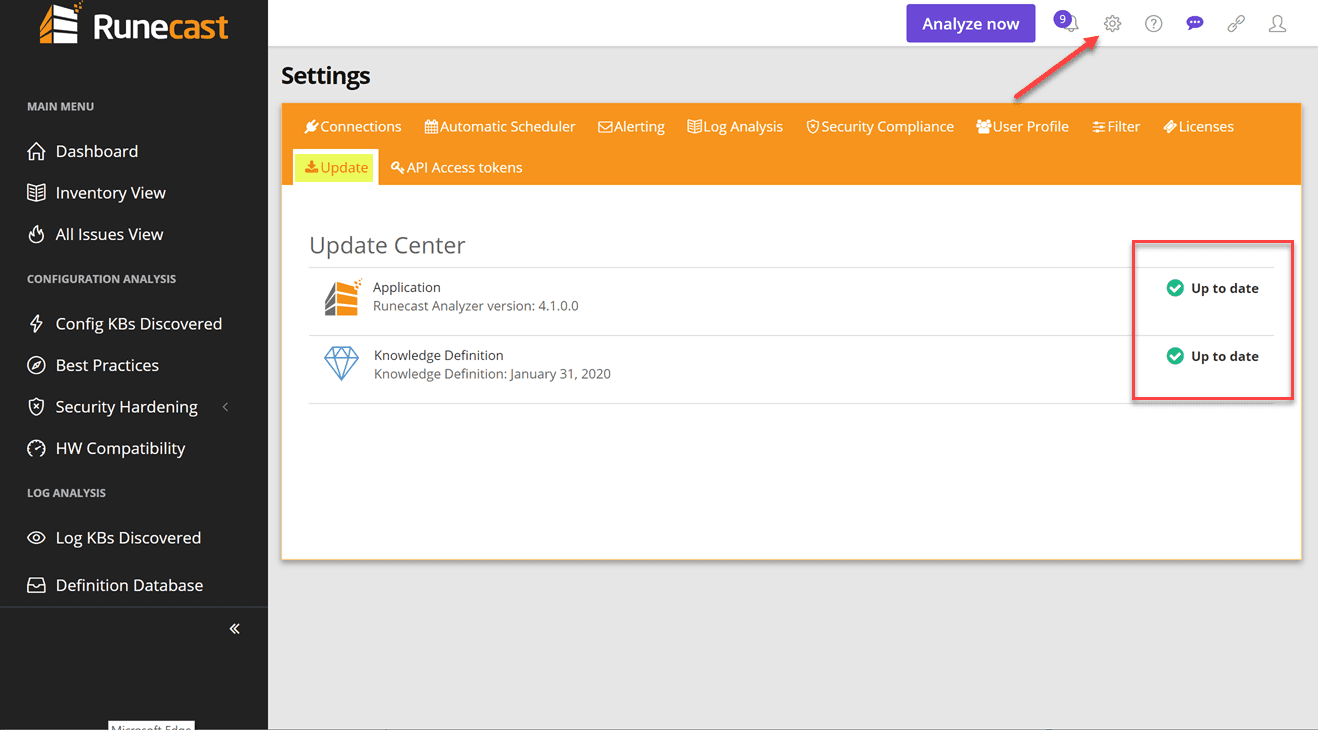
Let’s take a look at how to setup the new CIS Benchmark scans against your vSphere environment. First things first. Verify that your appliance is running the Runecast Analyzer 4.1 version.
Go to Settings > Updates and make sure you are Up to date. The great thing about the Runecast Analyzer appliance is that it is set to auto update by default. This means most likely you will find it has already updated to the latest version of the Analyzer as well as knowledge definitions.
As you can see below, we are running the 4.1.0.0 version which is the latest at the time of this writing.
Next, we need to enable the CIS Benchmark checks. How do we do this? Navigate to Settings > Security Compliance > CIS CSC. Once you have checked off the box for CIS CSC, click the Update button.

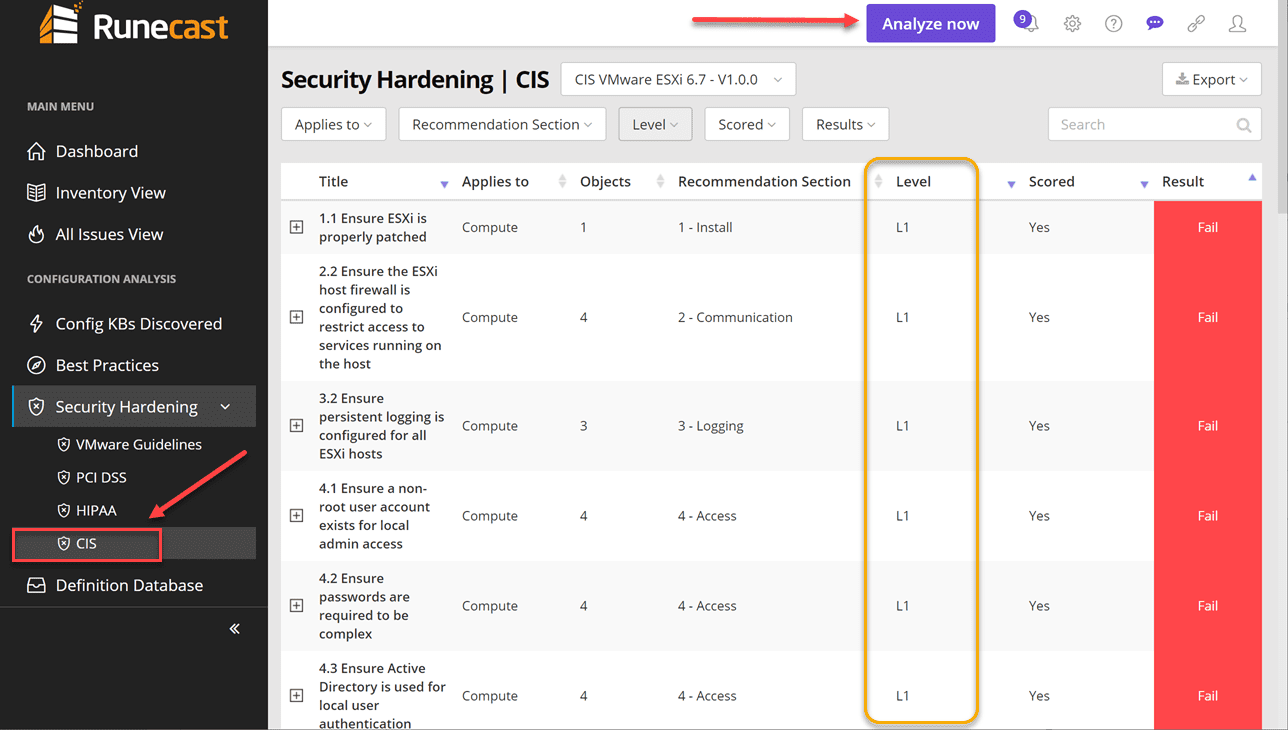
Once you have enabled the CIS CSC benchmark checks for your VMware vSphere environment, you will need to run the Analyze function against your environment. Simply click the Analyze now button to do this.
After running the analysis against your environment, you can navigate to Security Monitoring > CIS to display the finding relevant to CIS Critical Security Controls.
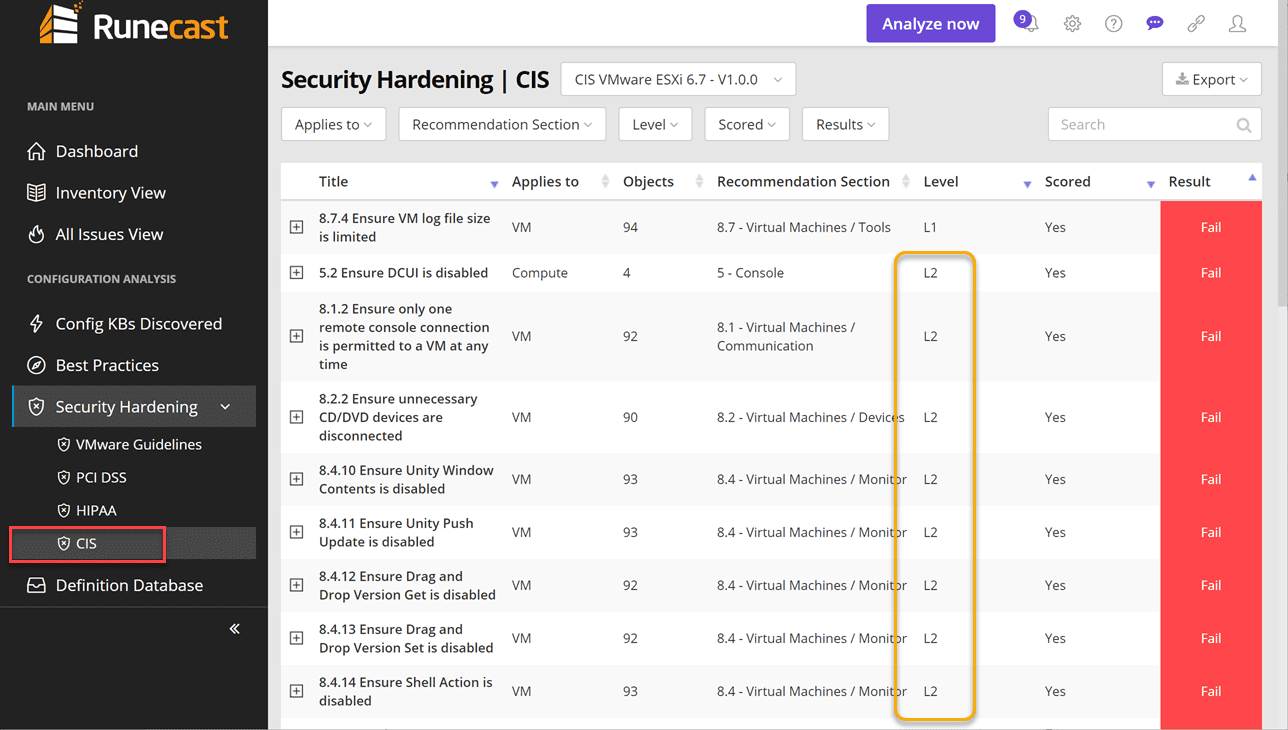
As you see below, Runecast holds true to the two levels of the CIS Benchmark. You will note which “level” of CIS CSC the finding is contained in under the Level column.
A look at a few of the findings for Level 2 under the CIS analysis.
True to the Runecast interface we all know and love, it provides tremendous detail in an easy to consume and user friendly format. I really like how Runecast presents the information in a way that is extremely easy to understand. The findings contain hyperlinks directly to the compliance framework standard for further detailing of the issue found. Additionally under the Findings tab, you will see the exact hosts that are responsible for flagging the finding. This makes it extremely easy to pinpoint and remediate.
Wrapping Up
The CIS Critical Security Controls VMware Scan with Runecast 4.1 is certainly going to be a powerful security tool in the arsenal for vSphere administrators.
Runecast takes the heavy lifting out of so many of the tedious tasks that you as a VMware administrator would be responsible for doing either manually or scripting out yourself. Runecast keeps getting better and better and Runecast Analyzer 4.1 is no exception.
Be sure to download a free trial version of Runecast Analyzer here.
Also, check out our other coverage of Runecast:
- Runecast 4.0 Released with AWS Analysis
- Runecast Analyzer 3.0 New Features
- Runecast Analyzer 2.7.3 released with editable PCI-DSS
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.