Security is a top priority among businesses and in the enterprise today. Additionally, it is a growing concern for home users. Windows environments have long been a target for malicious software and the like with malware and specifically ransomware topping the list of threats to security and data among others. Microsoft has been making strides to continually improve the security stance of the Windows operating system and have made some really great strides considering recent functionality added such as virtualization-based security or VBS that helps to protect credentials from theft and ensure application integrity. Today, Microsoft has announced the addition of a new Security Sandbox functionality in an upcoming release of Microsoft Windows 10 Professional and Enterprise versions. Let’s take a look at the Windows 10 Security Sandbox Announced for Upcoming Windows release to see how this new feature will benefit end users and enterprises alike.
What is a Security Sandbox?
The idea of “sandboxing” is not new, and is quite an effective means to thoroughly test untrusted or unknown software before installing it on an end user system. Malware can easily be installed without even knowing it if the software is installed without testing or any determination being made as to the intent of the software’s behavior.
A sandbox environment effectively creates this type of isolated environment to install untrusted or potentially dangerous software so that it cannot affect the host or production system. Depending on the underlying technology being used, the sandbox environment can easily be reset to a pristine state prior to installing the software. In other words, it is a disposable environment that can easily be used to install questionable software.
A security sandbox provides an “air-gapped” environment that cannot touch the production system or the host system and is usually implemented by way of some sort of isolated, virtualized environment. With the prevalence today of powerful hypervisor technologies built right into the operating system, as is the case with Windows 10, it has been really interesting seeing the creative ways that Microsoft is making use of virtualization in the realm of security. The recent Virtualization-based Security or VBS that was released was a really great step forward in this initiative as it creates an isolated environment for which very sensitive information such as credential hashes are stored that are protected from the general system memory address spaces, so that malware and other malicious software can’t easily access these protected information stores.
Microsoft is further building on these concepts with the announcement of the Windows 10 Sandbox app that will be released in a future build of the Windows 10 Pro and Enterprise operating systems.
Windows 10 Security Sandbox Announced for Upcoming Windows Release
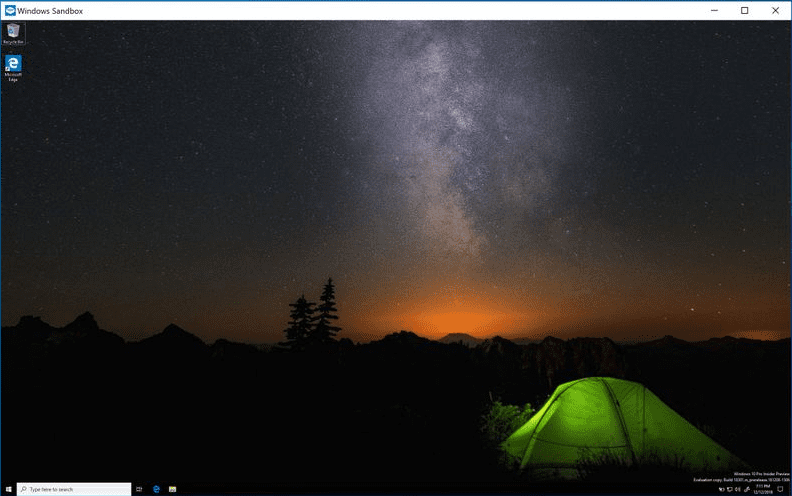
The Windows Sandbox is an isolated, temporary, desktop environment that allows creating this “sandbox” environment that is isolated and safe to run untrusted or other potentially malicious applications. The Windows Sandbox is not persistent, meaning as soon as it is closed, all the software that is installed within the Windows Sandbox and its files and state are deleted.
The great thing about the Windows Sandbox is that it is part of Windows and utilizes the existing Windows files found in Windows 10 Pro and Enterprise, so you don’t have to download a special VHD file to create the Windows Sandbox. Each time it is launched, it creates a new, pristine Windows environment from which you can run new applications. The same hardware-based virtualization that makes other features and security mechanisms possible are also used for the Windows Sandbox to create this separate, isolated kernel which protects the host from the Windows Sandbox environment.
What other technologies are utilized in creating the Windows Sandbox environment? While it is referred to by Microsoft as a “Windows Sandbox VM”, it is obvious that Windows Sandbox utilizes technologies used in Windows Containers. Microsoft has customized these technologies into an application that allows running this containerized environment without much additional hardware if any. As mentioned, it uses files and components that are already part of the Windows 10 Pro or Enterprise operating system. With this being the case, there is no additional VHD that must be downloaded or any additional installation or image files of any kind.
A “dynamic base image” is constructed by using the Windows image that is already on the host. This dynamic base image has clean copies of these file that can change, but the links do not change. So when the Windows Sandbox is closed, these changes do not persist. Microsoft does some slick provisioning here as when the Windows Sandbox feature is not installed, it is kept as a compressed package on disk (around 25MB). This package is then extracted to around 100MB when Windows Sandbox is installed.
Another bit of interesting tidbits around Windows Sandbox is that Microsoft says they are using Snapshot and clone functionality to speed up the performance of launching the Windows Sandbox by using the snapshot and clone functionality. Once it is booted once, the environment’s memory, CPU, and device state can be saved to disk and then restored from disk directly to memory instead of having to boot the containerized operating system each time.
Other interesting facets to the Windows Sandbox include the fact that Windows Sandbox can take advantage of hardware accelerated graphics as well as is aware of the battery state of the host. This allows optimizing battery usage so that power consumption is minimized. This allows Windows Sandbox to also be a viable solution for laptops.
Installing Windows Sandox
What will installing Windows Sandbox entail?
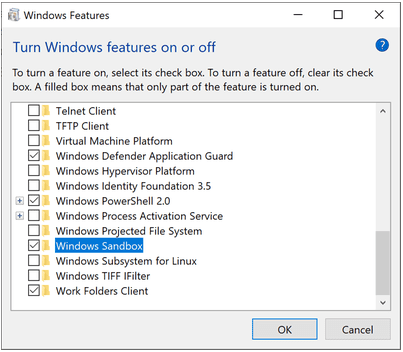
Windows Sandbox Prerequisites
- Windows 10 Pro or Enterprise build 18305 or later
- AMD64 architecture
- Virtualization capabilities enabled in BIOS
- At least 4GB of RAM (8GB recommended)
- At least 1 GB of free disk space (SSD recommended)
- At least 2 CPU cores (4 cores with hyperthreading recommended)
Since Windows Sandbox makes use of virtualization technology, you must enable virtualization in the BIOS if installed on a physical host, or enable nested virtualization if installed inside a virtual machine.
Hyper-V – Set-VMProcessor -VMName <VMName> -ExposeVirtualizationExtensions $true
After this, it is a matter of installing the Windows feature.
After installing the new Windows feature, simply launch the Windows Sandbox application. It is now ready to safely test applications, etc.
Windows Sandbox Use Cases and Integrations
There are many great use cases including the obvious that come to the fore when thinking about how this new Windows Sandbox can be used for ensuring end user client security. Aside from running potentially malicious programs to see what they do in the Windows Sandbox, what are some other potential uses?
For me personally, I think this could also be a great mechanism for safely browsing the Internet. For many such as myself, I have a full-blown virtual machine for doing just this task for security reasons. However, with the Windows Sandbox environment, this may no longer be needed as the Windows Sandbox will be viable to perform theses kinds of tasks.
Also, I think about the potential for endpoint security solutions that can hook into this functionality and use the Windows Sandbox feature as a local means to test executables and see what their intent and behavior are before allowing it to run on the host operating system.
There are many great use cases from a security standpoint that come to mind for this type of local sandbox technology. Microsoft promises this new functionality will be available in an up and coming release of Windows 10 such as Preview build 18305.
Thoughts
I think this is great that Windows 10 Security Sandbox Announced for Upcoming Windows Release by Microsoft. There are so many great use cases for this functionality. The great thing is Microsoft is empowering users with better security tools and applications than ever before which will certainly help to sway the odds back towards the good guys a bit. However, there is still much room for advancement in the area of security for the Windows operating system. With the Windows Sandbox and other great features that are no doubt on the drawing board, Microsoft is helping to bring security back to the forefront of features. Be sure to read more about the features in the official blog link from Microsoft here.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.