Backup Microsoft Office 365 for Remote Workers with NAKIVO
There is no question that organizations have been tasked with protecting new types of data this year. With the global pandemic, businesses have had to shift their operations to the cloud in many cases, and cloud migration strategies have certainly accelerated as a result. Backing up cloud data is extremely important and must be at the top of the priority list of cloud initiatives. Remote workers are now storing more data than ever in cloud storage and cloud SaaS services. Microsoft Office 365 is one of the top cloud SaaS environments and has huge momentum following the major shift to remote work. Are you responsible for your data? Is backing up your Microsoft 365 environment really necessary? How can this be done effectively? In this sponsored post, we will look at how to backup Microsoft Office 365 for remote workers using NAKIVO Backup & Replication.
Your Microsoft Office 365 data is your responsibility
Is it really your responsibility to back up the data you have housed in the Microsoft Office 365 cloud? Yes, it is. Cloud service providers such as Microsoft operate on the premise of a “shared responsibility model.” With the shared responsibility model, you are ultimately responsible for the protection of your data.
The cloud service provider (Microsoft) is responsible for providing reasonable protection for the cloud SaaS environment’s underlying infrastructure. However, they protect your data at best effort, so ultimately, it is on your business to ensure your data is safe.
Cloud Data is at Risk
One of the grave mistakes that can be made when migrating data to the cloud and cloud SaaS environments is failing to back up your data. Aren’t the hyperscale cloud providers that back cloud SaaS environments ultra-resilient with several “9’s” of durability and availability? Yes, they are. However, data loss can still occur in cloud environments. How?
Actually cloud environments are susceptible to many of the same risks to business-critical data, including:
- Accidental Deletions
- External and Internal Security Threats
- Legal and compliance penalties
- Gaps in retention policy
- Infrastructure failure
Let’s take a closer look at these reasons one-by-one and see how these apply to cloud environments.
1. Accidental Deletions
The story of data loss at the hands of an end-user is not new. After all, IT staff hasve been dealing with accidental or intentional data loss by end-users since the client-server architecture became mainstream in the enterprise. End-users often accidentally delete data they did not intend to delete. It might be that an end-user accidentally performed a “Save” instead of a “Save As” operation, overwriting data.
They may intentionally delete files, however, misidentifying the files they wanted to delete. All of these same types of data loss scenarios can play out in cloud SaaS storage environments. Microsoft Office 365 OneDrive for Business storage is a powerful cloud data storage platform. Data loss can still happen with cloud storage in a very similar way to on-premises file server storage.
Microsoft has introduced needed features such as file versioning that allows restoring a different copy of a file than the one that exists currently. There are limitations to this functionality, one of which is a time limitation on the number of versions that may be recovered. This currently is 30 days. While this may be enough time for most to recover a different version, it could lead to data loss in some cases.
2. External and Internal Security Threats
Security threats can present themselves in the form of both external and internal threats. These may be at the hands of cybercriminals who use things such as ransomware to affect your Microsoft Office 365 environment, as well as internal threats that come from disgruntled or otherwise unscrupulous internal employees.
External security threats can come from any number of sources. Hackers and other cybercriminals use any number of tools to steal, compromise, or otherwise destroy your data. Ransomware is one of the most destructive and problematic cybersecurity issues for your data today. In very little time, ransomware can encrypt and lock access to your data, both on-premises and in the cloud. Many businesses, especially SMBs, may not think of cloud data as being vulnerable to ransomware. However, this can lead to data loss that could even, in extreme cases, lead to lasting effects that a business may not be able to recover from.
Cybercriminals realize that organizations now are using cloud environments more than ever before. This leads to attackers looking for new ways to target cloud environments and cloud SaaS environments specifically. New-age ransomware, or ransomware 2.0, as some have described it, is cloud-aware and capable of encrypting data that exist in cloud SaaS services like online email and data storage.
Cloud environments use OAuth permissions delegation that easily allows third-party software applications to be granted access to cloud SaaS environments. Most of these are legitimate applications that bring much value and benefit to cloud SaaS environments. However, malicious third-party applications that look to steal data, introduce ransomware, or otherwise perform malicious operations are a new risk that organizations must deal with.
Ransomware can easily be introduced into a cloud SaaS service by one of these malicious applications. The application may be introduced using a phishing email that an end-user receives. The email may be from a seemingly legitimate sender or organization and ask the user to install an add-on or “update” to their cloud SaaS environment. Unknowingly, the end-user is granting the OAuth permissions needed for the malicious application such as ransomware to do damage. Kevin Mitnick demonstrated this type of attack and how an attacker can easily encrypt Exchange Online email using this method.
Another traditional way that ransomware can infect cloud SaaS storage like Microsoft Office 365 OneDrive for Business is by way of file synchronization. With file synchronization, files placed in the OneDrive folder on the local machine are automatically synchronized to the cloud. If an end-user computer is infected with ransomware, the locally stored copies are synchronized to the cloud copy of OneDrive for Business. Anyone connected to the online copy of the OneDrive shared drive in the organization will only see the ransomware-infected files.
Internal threats can be equally destructive when data is threatened by a disgruntled or unscrupulous employee who intentionally deletes data to cause financial or other harm to the business. This can be especially destructive in the case of a rogue administrator with high levels of access, which causes intentional damage to data stored either on-premises or in the Microsoft Office 365 cloud.
3. Legal and Compliance Penalties
The native built-in features in Microsoft Office 365 are limited in the capabilities that help your business observe legal and other regulatory requirements. Compliance is a critically important component of how businesses operate today and must be given top priority. Many compliance regulations require businesses to preserve and submit data relevant to court cases, produce financial data, and in the case of GDPR, document consumer data use and proof of deletion.
The litigation hold as part of Microsoft Office 365 is limited in the ability to freeze data. It is currently limited to 100 GB of data. This is usually not adequate for larger businesses with a large amount of data in Microsoft Office 365.
4. Gaps in retention policy
All businesses must think about the way they use, store, and protect business-critical data. If they do not, retention policy gaps develop that can potentially expose your business to data loss and even compliance and regulatory fines.
The same types of gaps can develop within Microsoft Office 365 in many different areas. These include:
- Failing to have backups of former employee data
- Failing to meet Restore Point Objectives (RPO) in the cloud
- Losing data when during migration operations
Failing to backup former employee data can bring about critical situations where data is needed from a former employee account due to an audit or other business need. If a former employee account has been deactivated, Microsoft deletes these inactive accounts after 90 days. What if the data is needed after the 90 day period?
Microsoft Office 365 does not provide any service thus far that is a true native backup solution. Not meeting established business Restore Point Objectives (RPO) and Restore Time Objectives (RTO) can be disastrous. Your business must protect business-critical cloud data in the same manner as data on-premises. This means adding a third-party backup solution that enables meeting established RPOs and RTOs.
5. Infrastructure failure
It may seem inconceivable to think that there could be an infrastructure failure in a hyperscale cloud environment that would lead to data loss. However, it can and has happened in the past. No matter how resilient the systems and contingency plans are, there is always a chance that all of the failure scenarios will line up just right to lead to a catastrophic loss of data.
Amazon AWS suffered a catastrophic series of failures on Labor Day weekend 2019, which led to some 1 TB of customer data being lost and unrecoverable. It helps to emphasize that your data in the cloud, while certainly more resilient than on-premises data, can be affected by infrastructure failure, as in the case of the AWS event.
Backup Microsoft Office 365 for Remote Workers with NAKIVO
With the tremendous shift to cloud-stored data and services, including Microsoft Office 365, backing up your Microsoft Office 365 data is crucially important. Your business may be relying on cloud data stored in Microsoft’s cloud environment more than ever. How can you effectively backup your Microsoft Office 365 data effectively to ensure services such as Exchange Online email, OneDrive for Business, and SharePoint Online?
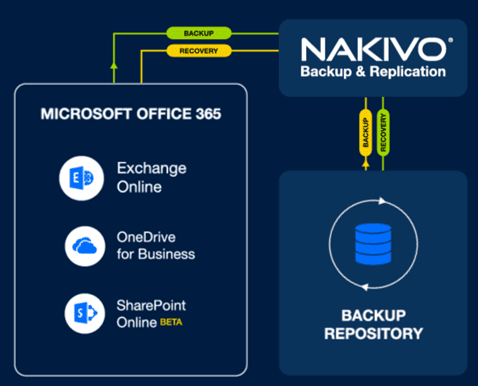
NAKIVO Backup & Replication is a powerful, fully-featured backup solution that provides a single tool to cover both on-premises workloads (physical and virtual) and cloud SaaS data located in Microsoft Office 365. It allows your business to protect valuable data found in Microsoft Office 365 core services, including Microsoft Office 365 Exchange Online, OneDrive for Business, and SharePoint Online.
Check out the official look at backing up Microsoft Office 365 with NAKIVO here:
It brings key-value capabilities to your critical data, including fast and efficient backups, replication, granular restores, and site recovery, all in the same management UI.
Exchange Online backup
With NAKIVO Backup & Replication, you can backup your Microsoft Office 365 Exchange Online accounts and individual mailboxes. This includes instant recovery of mailbox folders and emails back to the original location or specific mailbox. You can also search for specific content in your Microsoft Office 365 backups and perform granular recovery of those specific items.
OneDrive for Business backup
With NAKIVO’s OneDrive for Business backup, you have access to the following:
- Incremental backups of OneDrive for Business data
- Near-instant recovery of OneDrive files and folders
- Advanced search to find a specific file quickly
- Supports thousands of protected Office 365 users in a single software deployment
SharePoint Online backup
With the NAKIVO-provided SharePoint Online backups, you have a fully-capable backup solution for Microsoft SharePoint sites including:
- Granular restore of document libraries and lists
- Compliance searches that allow browsing backups and recovering what you need
With the protected Microsoft Office 365 backups that NAKIVO provides, your data is accessible and recoverable. This includes recovering files, almost instantly, to the original location or even another authorized account. With the ability to recover files in a granular manner and search your data, you can easily meet compliance and e-discovery requests.
NAKIVO’s new S3 object lock functionality that is now in beta also helps to add a ransomware protection layer that includes immutable backups to your data protection plan.
Check out my posts here covering NAKIVO’s Microsoft Office 365 backup functionality.
- Backup Office 365 Email with NAKIVO
- NAKIVO Backup and Replication v10.2 Beta New Features
- NAKIVO Backup and Replication v10 Beta Released New Features
- NAKIVO Backup and Replication v10.1 Released
The process to backup Microsoft Office 365 for Remote Workers with NAKIVO is super easy, straightforward, intuitive, and provides many options to protect your data.