Well, if you thought that Spectre and Meltdown (security nightmare blasts from the past) were dead, think again. There is a new data-leaking Retbleed Spectre variant that is yet another Spectre-based speculative-execution attack that allows attackers to expose secrets within the kernel memory despite protections already in place. VMware has released a VMSA security advisory, VMSA-2022-0020, which addresses Retbleed and several other speculative execution vulnerabilities. Let’s look at VMware affected by Retbleed Spectre variant and look closely at the VMSA that addresses this new vulnerability.
VMware ESXi 7.0 Update 3f Security fixes
The new vCenter Server 7.0 Update 3f and ESXi 7.0 Update 3f releases dropped just a couple of days ago. Among other fixes and enhancements, these releases contain fixes for new security vulnerabilities. One of these is the new Retbleed vulnerability. I wrote up a blog post covering the fixes found in the new ESXi 7.0 Update 3f, however, note the following:
- This release resolves CVE-2022-23816, CVE-2022-23825, CVE-2022-28693, and CVE-2022-29901. For more information on these vulnerabilities and their impact on VMware products, see VMSA-2022-0020.
VMware affected by Retbleed Spectre variant – VMSA-2022-0020
Note the following official statement from VMware regarding the new Retbleed vulnerability addressed in VMSA-2022-0020:
On July 12, 2022, several CPU manufacturers, along with security researchers, announced security advisories addressing side-channel vulnerabilities in CPU hardware. VMware has issued a VMware Security Advisory (VMSA) covering these issues as they affect VMware software and customers.
These issues are vulnerabilities in CPU hardware and not with VMware software. However, VMware can use the flexibility of the vSphere platforms to help affected customers mitigate the issues. Those mitigations are what we detail in the VMSA and in this list of questions and answers.
VMSA-2022-0020: Questions & Answers | VMware
VMware affected by Retbleed Spectre variant – VMSA-2022-0020 FAQs
What CVE numbers are involved with this particular VMSA?
- CVE-2022-23816, CVE-2022-23825, CVE-2022-28693, CVE-2022-29901
Is Retbleed a vulnerability in VMware software?
- No, this is a hardware vulnerability found in CPUs
Can you wait to apply patches to your VMware environment?
- Yes you can wait, but it isn’t necessarily advised to do so, especially when it involves security matters. VMware updates are cumulative when it comes to security. Applying the latest updates will also apply all earlier security updates. So, if you do wait and then decide to apply all the patches later, the newer patches will include the Retbleed remediations.
Which VMware systems are affected by the new Retbleed vulnerability?
- Really any VMware environment running vSphere on top of AMD or Intel-based server platforms.
What is the severity of this new Spectre-related vulnerability?
- it is a CVSS 5.6 rating which is classified as Moderate.
How can an attacker exploit this vulnerability?
- The attacker needs priviledged access on a virtual machine, either root or administrator access.
What are the names for the vulnerabilities documented in VMSA-2022-0020?
- Security researchers have named these attacks “RetBleed.” AMD refers to these as “Branch Type Confusion” vulnerabilities. Intel has dubbed them “Return-Stack-Buffer-Underflow” vulnerabilities.
What do you need to do besides patch? Are there other configurations that need to be introduced?
- Once you patch, the mitigation is on by default. You don’t have to flag on any other configuration settings, or parameters
Is there a way to mitigate this vulnerability without patching, like using a firewall?
- Since the vulnerability is a hardware vulnerability in the CPU hardware itself, you can’t filter a type of traffic with a firewall to successfully mitigate the vulnerability.
What is VMware saying about performance impacts of mitigating this new Spectre-related vulnerability?
- These ESXi patches have no meaningful performance impacts based on VMware testing. The mitigation in ESXi controls how the virtual machine runtime environment is allowed to talk to ESXi, which is communication outside of how the workload and guest OS are executed and uses well-tested mechanisms already present — and highly optimized — in vSphere.
Resources regarding VMware and RetBleed and VMSA-2022-0020
- VMware ESXi 7.0 Update 3f Release Notes
- VMSA-2022-0020: Questions & Answers | VMware
- Older AMD, Intel chips vulnerable to data-leaking ‘Retbleed’ Spectre variant • The Register
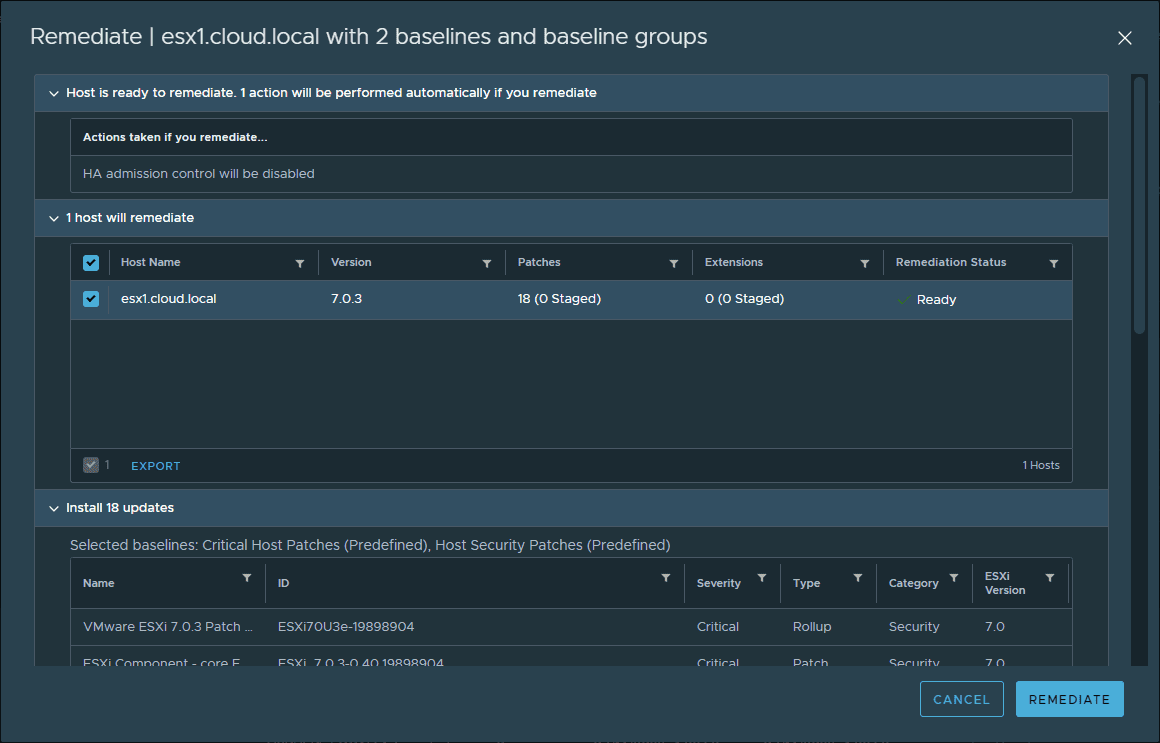
Watch my video covering how to upgrade your ESXi hosts using vSphere Lifecycle Manager:
Wrapping Up
I think many of us, when we were dealing with Spectre and Meltdown a few years back, were thinking to ourselves, this is probably not the last time we will hear of these vulnerabilities. Unfortunately, that time is now. This is yet another vulnerability as part of additional “shades” of the Spectre attacks as VMware affected by Retbleed. Customers still need to be vigilant when keeping the latest patches applied to their VMware environments to ensure the latest protections against these and other vulnerabilities.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.