Amazon AWS has a wide range of services that many organizations today are making use of. One of those is Amazon RDS. Amazon provides a customized external Amazon DNS name for connecting to RDS databases. What though if you need to connect to your AWS RDS instance using the internal IPs? How do you find those? Let’s take a look at how to find AWS RDS internal IP address with PowerShell and see how you can use the AWS PowerShell cmdlets to accomplish this.
RDS Network configurations
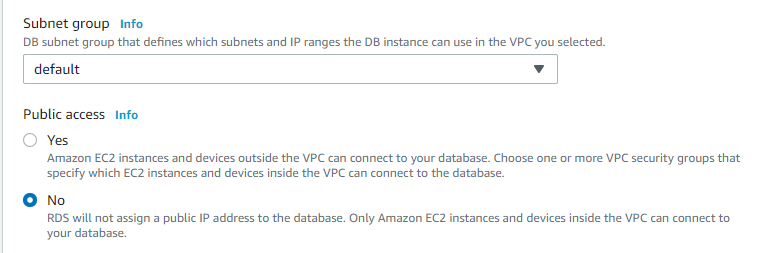
There are many different aspects of your RDS network configuration settings that determine the internal IPs configured for your RDS instance. First of all, when setting up RDS, you have the choice of whether or not you want the RDS instance to be publicly accessible. As you can see below, under the Public access configuration, you can choose the configuration as:
- Yes – Amazon EC2 instances and devices outside the VPC can connect to your database. Choose one or more VPC security groups that specify which EC2 instances and devices inside the VPC can connect to the database
- No – RDS will no assign a public IP address to the database. Only Amazon EC2 instances and devices inside the VPC can connect to your database.
AWS RDS internal IP network connections found in EC2
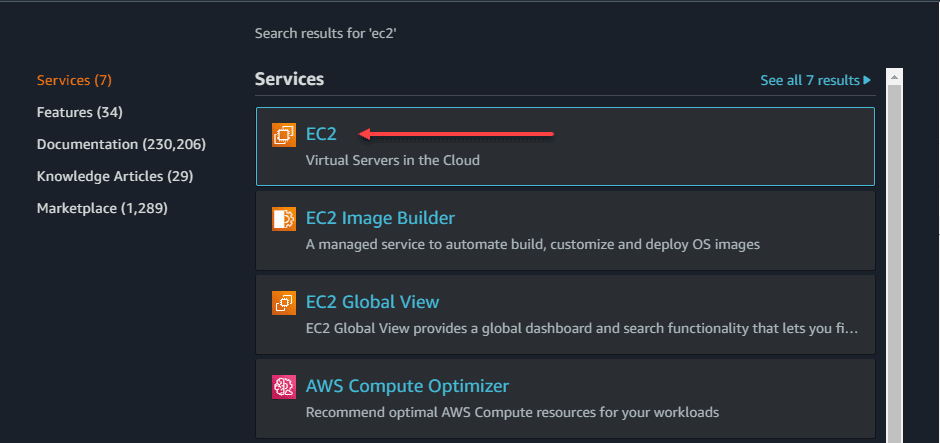
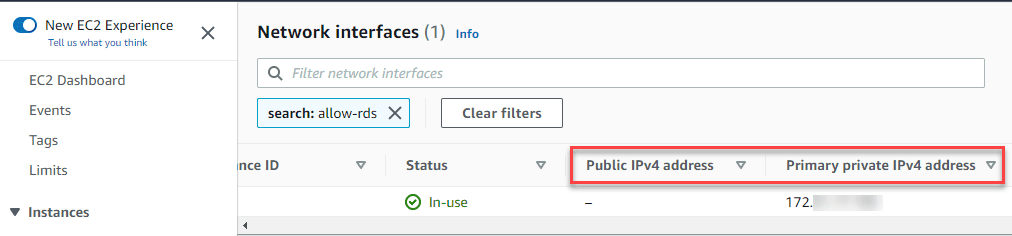
Amazon AWS RDS internal IP addresses are connected to the RDS databases using the EC2 network interfaces. Yes, that is correct, EC2, not RDS. In fact to find the information you are looking for to see which IP addresses are assigned to AWS RDS instances, you need to navigate, not to RDS, but to the EC2 dashboard.
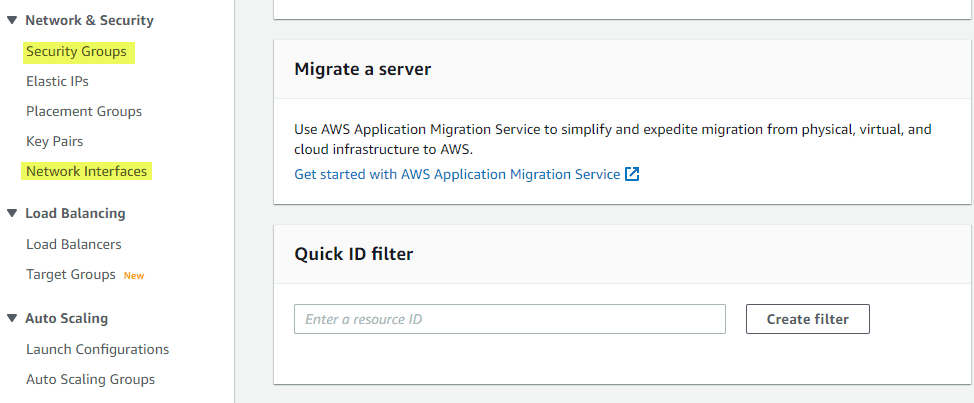
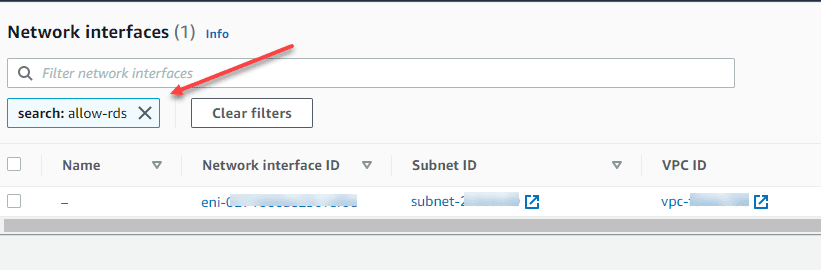
Before looking at the network interfaces dashboard, if you have many network interfaces associated with many different types of resources in AWS, it may be difficult to find your RDS instance internal network connection. However, an easy way to still find your RDS network interfaces is to filter them based on your security group name associated with the RDS connection.
In the network interfaces dashboard, you will see that you can filter the view using your security group name. In the filter network interfaces search box, just type the name of your security group connected to your RDS instance.
Once you are filtered, you can scroll the box of information over and you will see the Public IPv4 address and Primary private IPv4 address. It is important to understand that you may see multiple IP addresses assigned to RDS if you chose the default settings for high availability. Amazon spins up a secondary IP address endpoint for RDS if you leave the defaults. The image below is taken from a DEV/Test instance without high availability turned on for simplicity.
Find AWS RDS Internal IP Address with PowerShell
Now that we have an idea of how to find this information from the AWS EC2 dashboard, let’s see if we can do this in PowerShell. As many automated processes start out, it is a good idea to understand where everything “lives” in the GUI dashboard before you begin to automate as it makes it easier to understand what your logic should be when you begin the process to automate or use a script to find various pieces of information.
You will need a couple of things installed for working with Amazon AWS via PowerShell. Those include:
I have the AWS CLI v2 installed to create profiles and work with those as it is easier for that purpose. Then I have the AWSPowerShell module installed to use PowerShell to work with and gather information programmatically from EC2, RDS, etc.
Once you have the modules listed above configured:
- Configure your AWS profiles using the aws configure –profile command if you are working with multiple profiles
- Run the import-awspowershell module after installing or add this to your PowerShell profile to add automatically
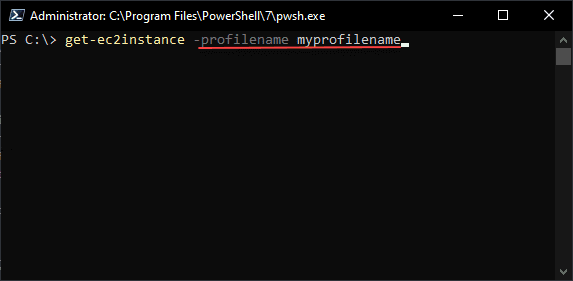
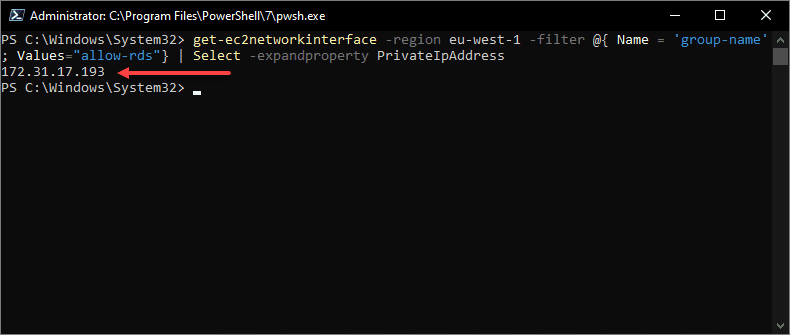
Use the get-ec2networkinterface cmdlet
Like we had to visit the EC2 dashboard to see visually in the GUI the network interface address, we need to use the get-ec2networkinterface cmdlet to see the internal IP addresses of the RDS interface(s). To perform a similar action as we did in the GUI by filtering based on the security group, you can use the following cmdlet
get-ec2networkinterface -profilename myprofile -region us-east-1 -filter @{ Name = 'group-name'; Values="allow-rds"} | Select -expandproperty PrivateIpAddressNote the internal IP address returned as a result of the PowerShell cmdlet query.
Note that if you want to use a different type of filter for the get-ec2networkinterfaces cmdlet, there are many to choose from. The following is taken directly from the official Amazon get-ec2networkinterface reference:
addresses.private-ip-address– The private IPv4 addresses associated with the network interface.addresses.primary– Whether the private IPv4 address is the primary IP address associated with the network interface.addresses.association.public-ip– The association ID returned when the network interface was associated with the Elastic IP address (IPv4).addresses.association.owner-id– The owner ID of the addresses associated with the network interface.association.association-id– The association ID returned when the network interface was associated with an IPv4 address.association.allocation-id– The allocation ID returned when you allocated the Elastic IP address (IPv4) for your network interface.association.ip-owner-id– The owner of the Elastic IP address (IPv4) associated with the network interface.association.public-ip– The address of the Elastic IP address (IPv4) bound to the network interface.association.public-dns-name– The public DNS name for the network interface (IPv4).attachment.attachment-id– The ID of the interface attachment.attachment.attach-time– The time that the network interface was attached to an instance.attachment.delete-on-termination– Indicates whether the attachment is deleted when an instance is terminated.attachment.device-index– The device index to which the network interface is attached.attachment.instance-id– The ID of the instance to which the network interface is attached.attachment.instance-owner-id– The owner ID of the instance to which the network interface is attached.attachment.status– The status of the attachment (attaching|attached|detaching|detached).availability-zone– The Availability Zone of the network interface.description– The description of the network interface.group-id– The ID of a security group associated with the network interface.group-name– The name of a security group associated with the network interface.ipv6-addresses.ipv6-address– An IPv6 address associated with the network interface.mac-address– The MAC address of the network interface.network-interface-id– The ID of the network interface.owner-id– The account ID of the network interface owner.private-ip-address– The private IPv4 address or addresses of the network interface.private-dns-name– The private DNS name of the network interface (IPv4).requester-id– The alias or account ID of the principal or service that created the network interface.requester-managed– Indicates whether the network interface is being managed by an Amazon Web Service (for example, Management Console, Auto Scaling, and so on).source-dest-check– Indicates whether the network interface performs source/destination checking. A value oftruemeans checking is enabled, andfalsemeans checking is disabled. The value must befalsefor the network interface to perform network address translation (NAT) in your VPC.status– The status of the network interface. If the network interface is not attached to an instance, the status isavailable; if a network interface is attached to an instance the status isin-use.subnet-id– The ID of the subnet for the network interface.tag:<key> – The key/value combination of a tag assigned to the resource. Use the tag key in the filter name and the tag value as the filter value. For example, to find all resources that have a tag with the keyOwnerand the valueTeamA, specifytag:Ownerfor the filter name andTeamAfor the filter value.tag-key– The key of a tag assigned to the resource. Use this filter to find all resources assigned a tag with a specific key, regardless of the tag value.vpc-id– The ID of the VPC for the network interface.
Wrapping it up
Hopefully this quick walkthrough on how to find AWS RDS internal IP Address with PowerShell will help any who are struggling to find the private IP address associated with their RDS instance. Using the AWS PowerShell module, you have access to many great cmdlets that can help automate and find information much more quickly than using the AWS console.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.