Modernizing the way IT operations is able to provision, manage, and provide the needed resources for development necessitates the need to automate processes. This is especially true in cloud environments like Microsoft Azure. Terraform is gaining wide adoption as the tool of choice across cloud platforms. It allows being able to automate cloud infrastructure in a declarative way. In other words, you describe how you want the cloud infrastructure to look and Terraform automates the process to get to that end result. While there is a learning curve with Terraform, it is not difficult to get started. In this terraform for Azure tutorial, we will take a look at how to get started with Terraform in Azure and see how you can easily access the tools, connect to your environment, and provision resources.
Accessing the Terraform for Azure Tools
The first thing you will probably want to know is how you can access the Terraform tool to start interacting with your Azure environment. There are a couple of ways that I will describe there:
- Azure Cloud Shell – Allows you to access Terraform from your Azure Portal once you are logged in
- Azure CLI in PowerShell – After installing Azure CLI you can gain the information you need to interact with your Azure environment with Terraform
Terraform with Azure Cloud Shell
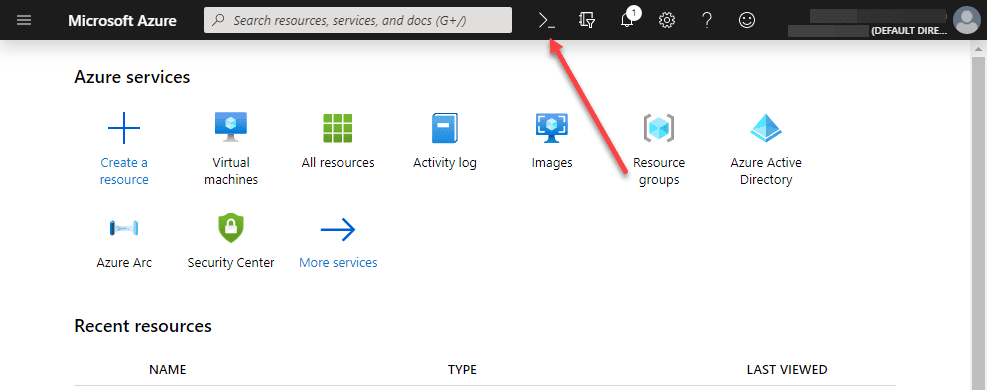
Azure Cloud Shell is the built-in shell environment that you can access inside your Azure Portal. It is designated at the top of the screen by what looks to be a PowerShell icon.
You will want to make sure you are in the Bash shell in the
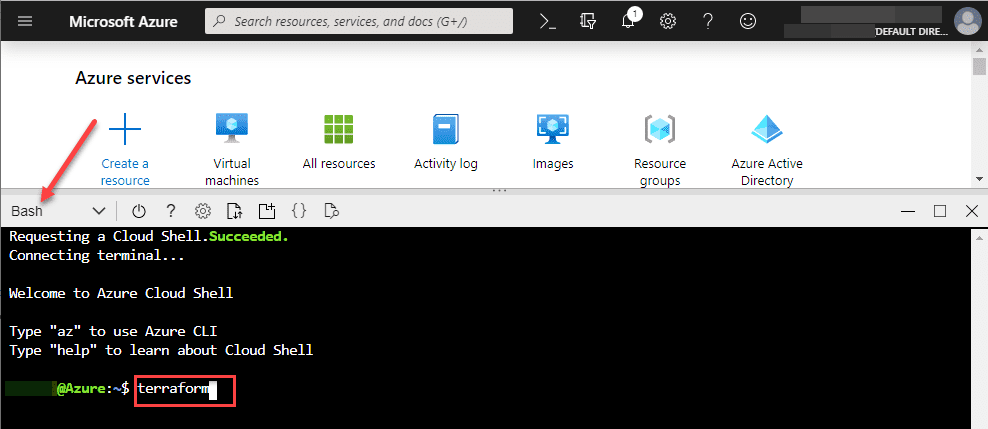
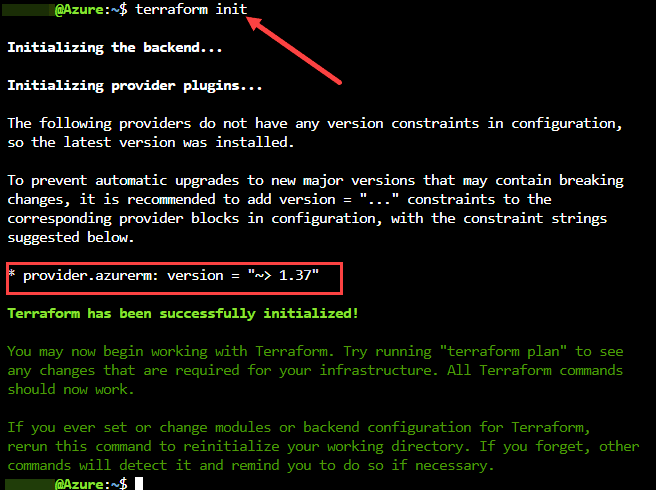
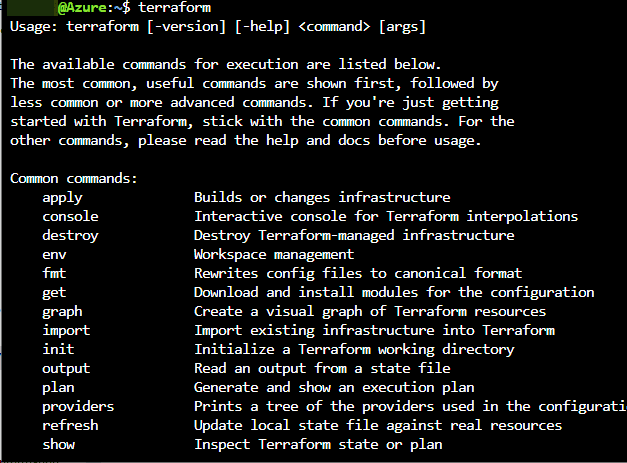
As you can see, you don’t have to download the Terraform executable or install anything. Terraform is there by default. You can see the various parameters of the Terraform executable by simply typing terraform and hitting enter.
The Azure Cloud Shell creates a storage environment for you from which you can create and edit Terraform template files from which you can declare and provision your infrastructure.
Terraform generally follows the workflow:
- terraform init
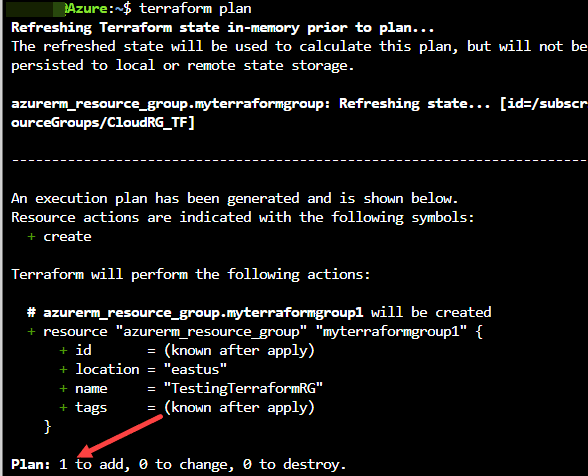
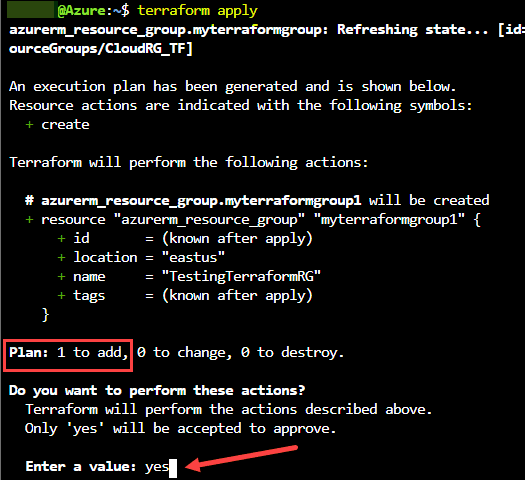
- terraform plan
- terraform apply
The init phase downloads the azure provider which is the terraform piece that interacts with the Azure APIs. The plan parameter is not required, however, it is like a “what if” type parameter that actually checks the code and validates that it will do what you think it will do. Nothing is changed during the plan stage. The apply parameter actually does the work. When you run terraform apply, you are making changes to your Azure infrastructure.
Create a Test Terraform File
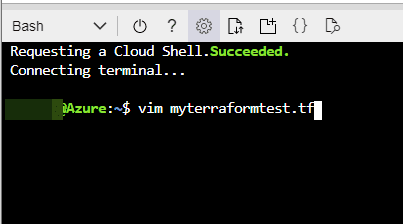
To get your feet wet with Terraform for Azure, you can create a quick little terraform file that will perform an action to demonstrate what it can do. Create a new terraform file in your Bash Azure Cloud Shell using the vim command.
Edit the file and place the following code inside:
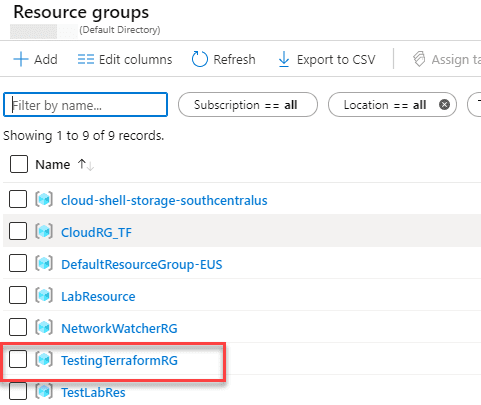
resource "azurerm_resource_group" "myterraformgroup" {
name = "TestingTerraformRG"
location = "East US"
}
You can modify the names as you want as well as the Azure region.
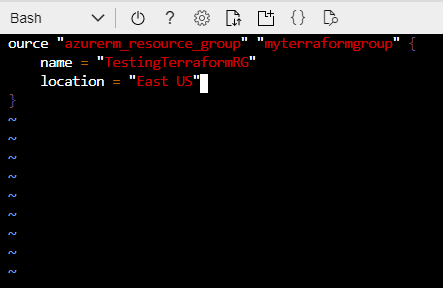
In the Bash Azure Cloud Shell, you can use CTRL+C to get out of insert mode. Then type the normal :wq to write the file and save it.
Azure CLI in PowerShell
In our Terraform for Azure Tutorial, there is another means to interact we want to cover – the Azure CLI/PowerShell. The Azure CLI in PowerShell is not really required for Terraform itself, however, the Azure CLI allows you to interact with your Azure environment and get needed information to interact with Azure using Terraform.
Once you have downloaded and installed the Azure CLI, you can use it from within PowerShell.
Setup Access to Azure with Terraform
One of the benefits of running Terraform from the Azure Cloud Shell is that it has authentication automatically implied for accessing your environment. However, if you are accessing Azure remotely from your administrative workstation to use Terraform, you will have to setup access to your Azure environment for using Terraform.
Microsoft has a document that describes how to setup Terraform access to Azure. However, there is a slight error in the documentation. If you have only one Azure subscription, you will receive an error on one of the commands.
Use the following commands get the needed information and RBAC configuration in place for accessing Azure with Terraform. The second command setting the variable for the $subscription_id is the additional step needed. You get the subscription ID from the first command ran. Once you have set the variable, you can proceed with the other commands.
az account list --query "[].{name:name, subscriptionId:id, tenantId:tenantId}"
$subscription_id="xxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx"
az account set --subscription="${SUBSCRIPTION_ID}"
az ad sp create-for-rbac --role="Contributor" --scopes="/subscriptions/${SUBSCRIPTION_ID}"
Once you have the above information created and obtained, you can place the following code block in your Terraform HCL files:
provider "azurerm" {
subscription_id = "xxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx"
client_id = "xxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx"
client_secret = "xxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx"
tenant_id = "xxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx"
}
Wrapping Up
Hopefully this Terraform for Azure Tutorial will help any who may be struggling with the basics of using Terraform with Azure. Terraform is a great way to quickly and easily get started automating your cloud environments.
There are tons of Terraform templates out on the net that you can recycle, customize, and quickly put to use. Check out these resources as well:
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.