As we have covered in previous posts, VMware virtual machine encryption requires an external key manager. There has been work done to allow testing this feature out by way of a cool docker container key manager. However for those really wanting to test out a production ready key management server, Hytrust KeyControl is a production ready solution that provides a powerful means of instituting VMware virtual machine encryption. Let’s take a look at Hytrust VMware Virtual Machine Encryption, its installation and features.
Hytrust VMware Virtual Machine Encryption Installation
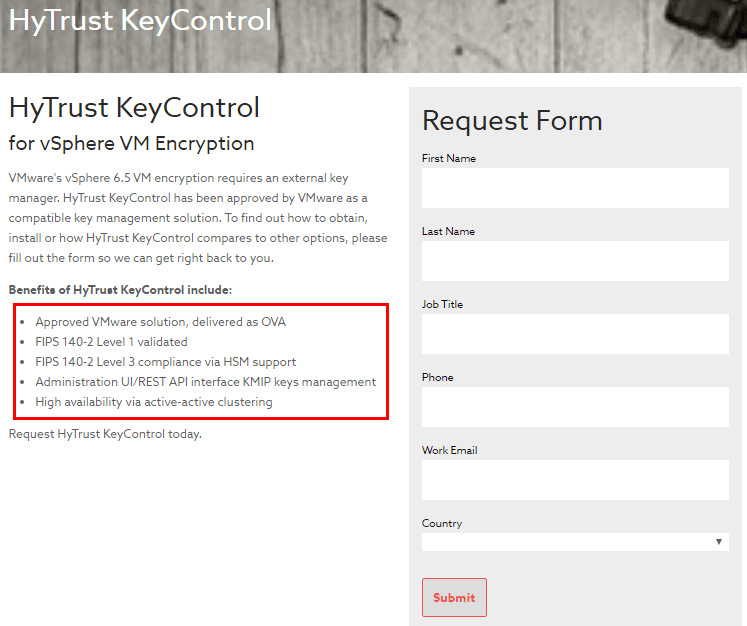
One of the really nice things about Hytrust KeyControl is you can request KeyControl for no license fees from Hytrust. Simply fill out the form located here and sales will reach out to you shortly with a license key. Hytrust KeyControl provides really great features for those looking to institute VMware Encryption such as:
- Easy provisioning via an OVA appliance
- FIPS 140-2 Level 1 validated
- FIPS 140-2 Level 3 compliance via HSM support
- Administration via snappy UI and REST API interface for KMIP keys management
- Ability to cluster KeyControl servers
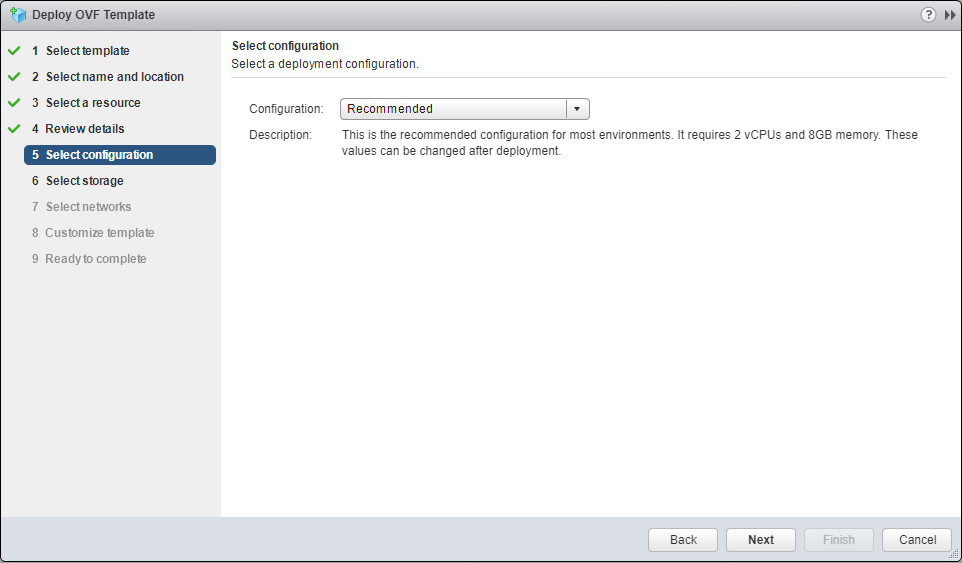
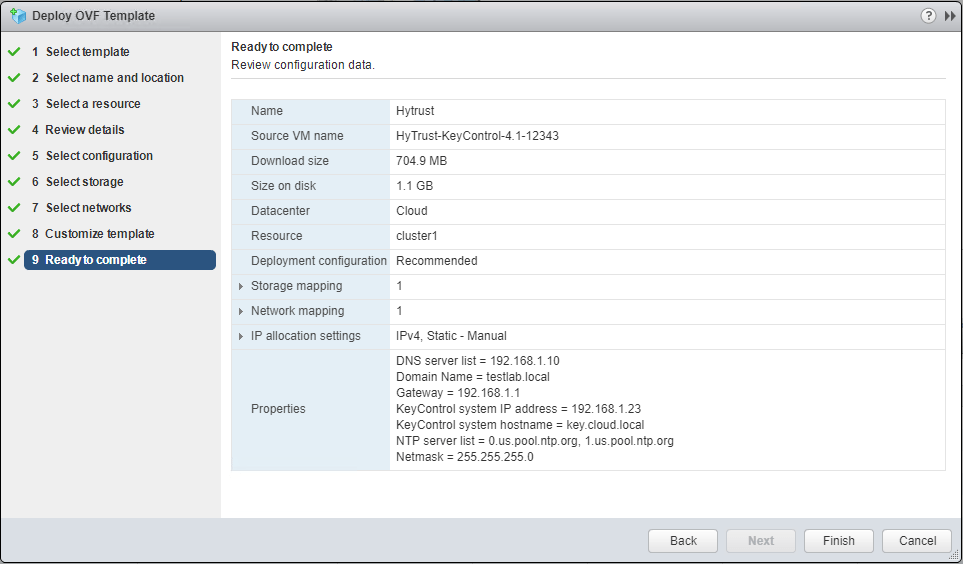
Let’s take a look at the installation process including deploying the Hytrust KeyControl OVA appliance and initial setup steps. The OVA deployment process follows the usual “next, next, finish” approach. Below, let’s just highlight a few of the notables. On step 5 we have the Configuration option that basically sizes the appliance. Here I am accepting the default configuration which is Recommended. it includes 2 vCPUs and 8GB of memory.
The other configuration to note is the Customize Template configuration where we specify the Network Properties of the appliance configuration.
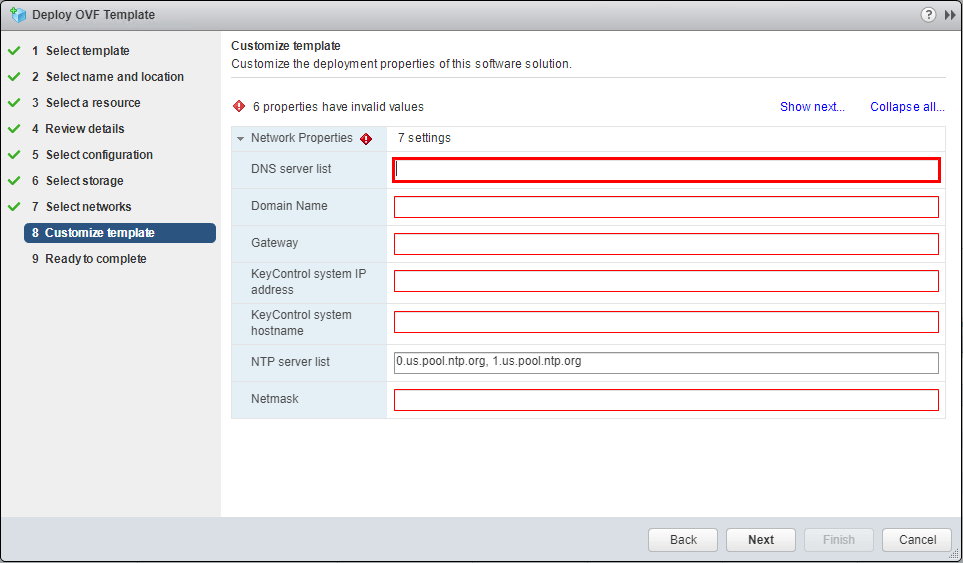
Note how I configured the KeyControl system hostname with the FQDN. This causes issues as you will see in the following screenshots.
After finalizing the configuration, we boot the appliance. Also, since I was deploying this in a home lab, I adjusted the configured memory on the Recommended configuration down to 4 gigs of memory and didn’t see a problem doing that.

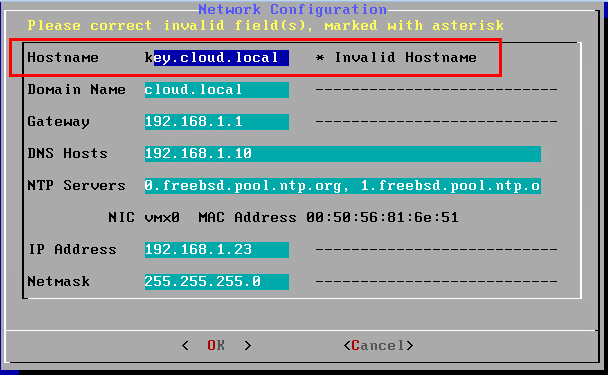
After the appliance booted, I saw the following. The network configuration does not like an FQDN for the Hostname. Once I changed this to simply a “NETBIOS” name, it accepted it and finalized the configuration.
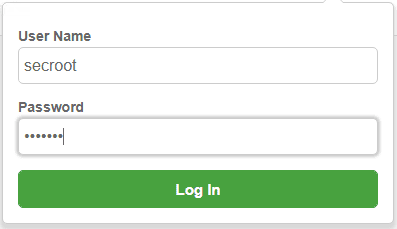
After the appliance finishes configuring and booting, browse out to the hostname of the appliance.
The default username and password for the appliance is secroot/secroot.
Configuring Hytrust KeyControl for VMware Virtual Machine Encryption
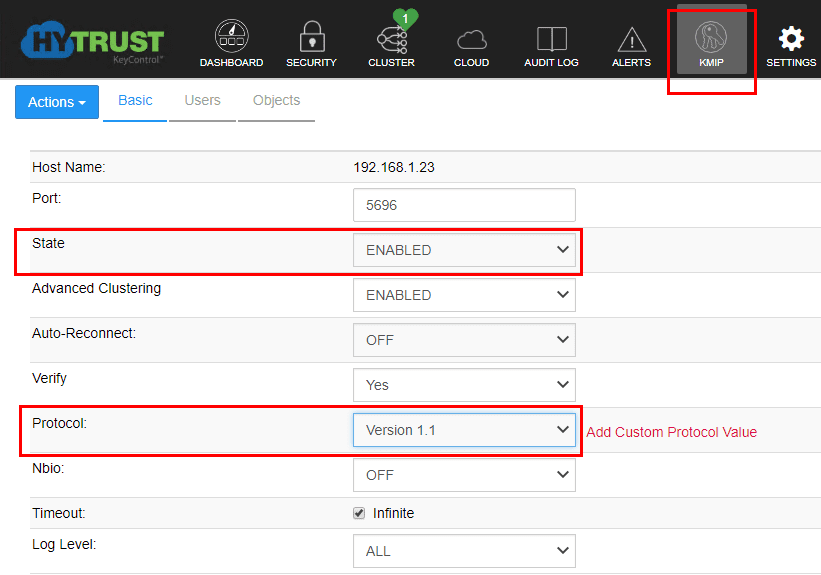
To configure Hytrust KeyControl for VMware virtual machine encryption, we simply need to flag on a couple of options, setup a user account, and download a certificate bundle for the user. The configuration we need to make to setup Hytrust for VMware virtual machine configuration, we navigate to the KMIP tab and make the following changes.
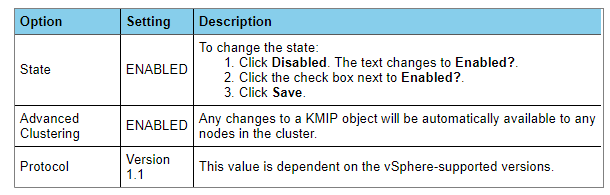
For me, the Advanced Clustering option was already set to ENABLED. So, I only made the other two changes and documented, setting the State to Enabled and the Protocol to Version 1.1.
Adding a User Account for Virtual Machine Encryption
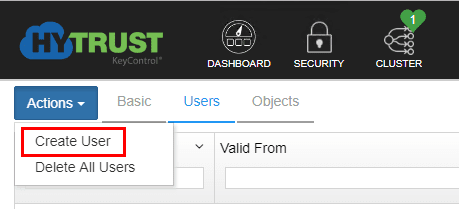
After flagging on the appropriate options in the KMIP configuration, we need to add a user account to use with establishing trust with vCenter. This is configuring on the KMIP tab, Users page. Select the Actions menu and choose to Create User.
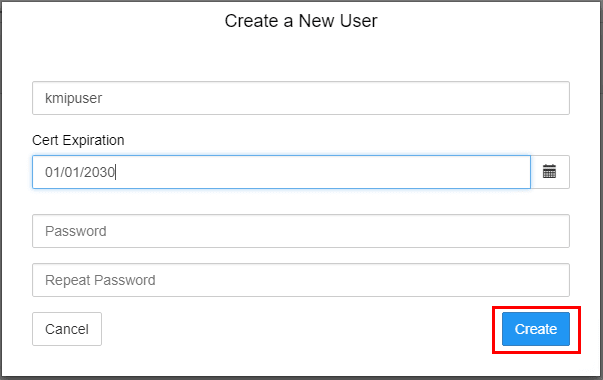
To create a new user, we simply set the username and the Cert Expiration date. DO NOT set the Password. Click the Create button.
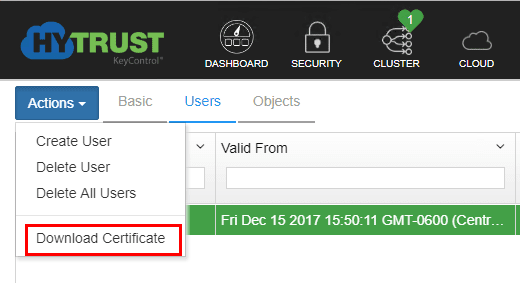
Click on the user you just created and then choose the Actions menu again and select the Download Certificate option.
Establishing Trust between Hytrust KeyControl and vCenter Server
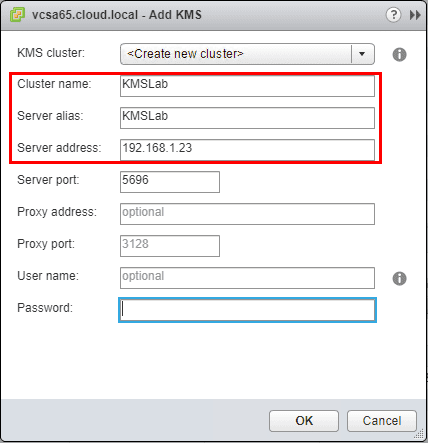
To get started adding a KMS server in vCenter, in the Web client, click on your vCenter server >> Configure >> Key Management Servers. Then click the Add KMS button. Create a name and add the address for the Hytrust KeyControl server.
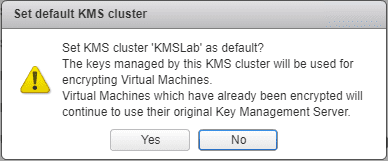
vCenter will ask if you want it to be the default.
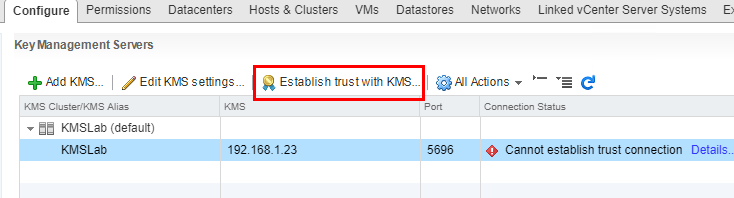
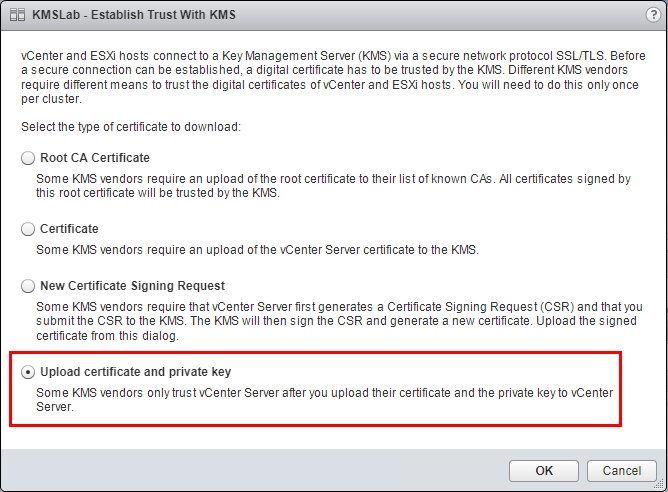
After adding, we need to Establish trust with KMS server we have added by clicking the button.
The Establish Trust With KMS box will launch. Click the Upload certficate and private key option at the bottom.
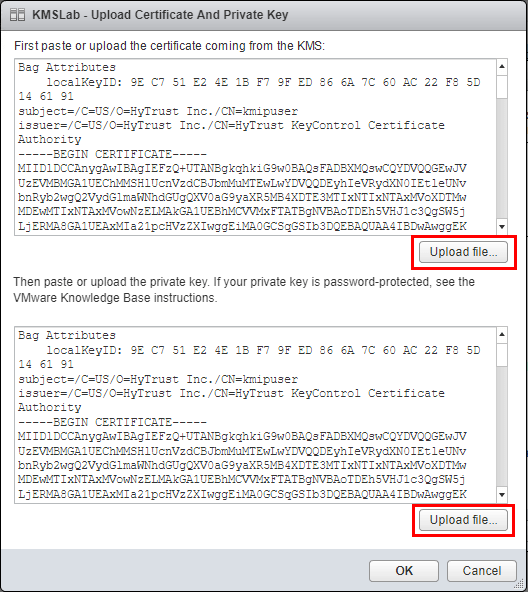
Here we will use the certificate downloaded from the Hytrust KeyControl server. Upload the .pem file for the user created to both the certificate and private key boxes.
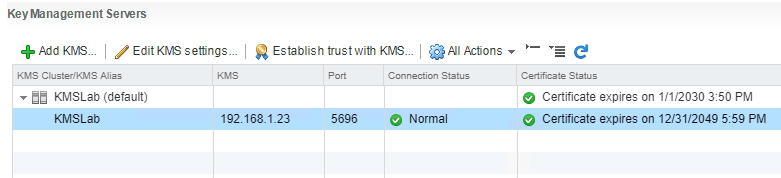
We should now see that trust has been established between the Hytrust server and vCenter with “green checks”.
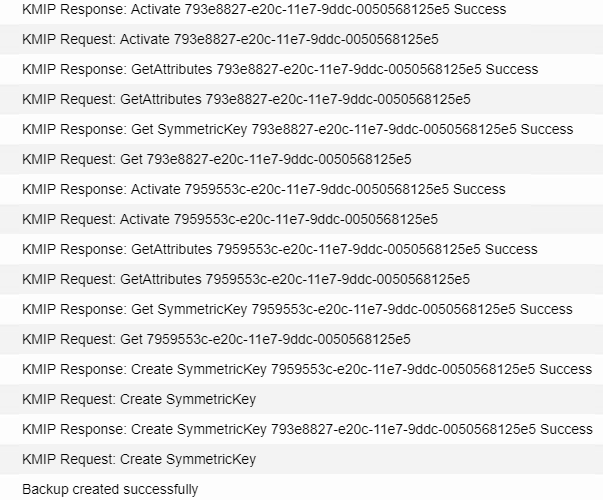
We can now follow the normal process of encrypting a virtual machine by setting the storage policy. In the Audit tab of Hytrust, after we encrypt a virtual machine, you can see in the process of encryption that happens from the Hytrust side.
Thoughts
The Hytrust VMware Virtual Machine Encryption solution is very slick. The OVA appliance deploys very quickly and is easily configurable. The web interface with KeyControl is also very intuitive and I found the documentation on the Hytrust site for configuring KeyControl for VMware virtual machine encryption to be accurate and easy to follow. Within only a few minutes I was able to get up and running with Hytrust KeyControl and had a virtual machine encrypted. This solution offers a lot of powerful features including clustering. Without support the solution is free. Support for Hytrust KeyControl is a paid for product so if using in production, support is more than likely something you will want to include. Otherwise, to have the product free of charge and be able to get up and running quickly with virtual machine encryption is very cool.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.