The advantages of a cloud computing system are many, but so are the risks associated with it. When a cloud system is used, all or most of a company’s data, usually containing vital and private information, is essentially being handed over to a third-party. Larger companies may overcome this by creating their own, company run, cloud system, but most companies will contract with a separate entity solely responsible for maintaining cloud systems.
What does it take to create a cloud system?
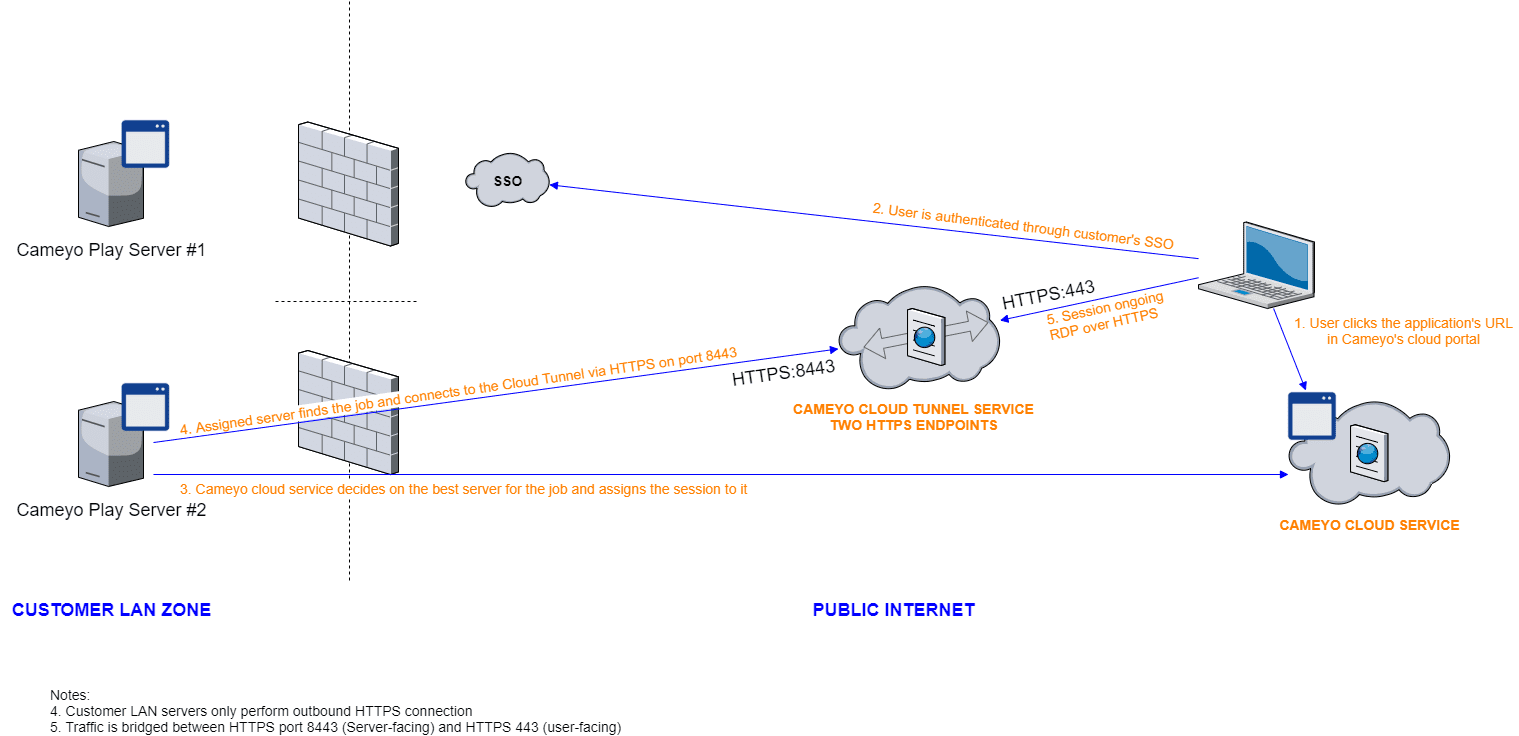
The exact requirements of a cloud system are highly variable and directly related to what one would expect that cloud system to do. Just like a more advanced individual computer is needed for more complex or larger tasks, a larger cloud system would be needed to handle more advanced or more numerous programs or larger amounts of data. On the most basic level, a cloud system must consist of one master computer that would manage the cloud system, a storage databank, and a server control node that would link the cloud system to client computers. From there, it is all about adding hardware. Additional computer processors would increase the raw computing power of the cloud system. More storage databases would increase the amount of data that could be kept on the cloud system. Adding more server nodes would increase the number of client computers that can access the cloud system at one time.
There is one additional caveat. A fully reliable cloud system would actually need double its maximum amount of hardware. All hardware breaks down overtime or has the chance to spontaneously fail. Also, maintenance tasks usually require that some or all of a system be temporarily shut down. In order to keep the cloud system running constantly, additional hardware would need to be ready in case of failures. This is nowhere more important than in terms of data storage. A firm would maintain a duplicate databank and then keep a copy of all data stored on the cloud totally separate in case of hardware failure, data corruption, or infiltration.
Concerns about utilizing cloud systems:
Security is a common concern when discussing the use of cloud systems. On one hand, a company is surrendering its data security duties to a third-party. If this separate entity’s security procedures are not top notch, the cloud system could be compromised. Also, data must pass continuously between a client and the cloud system. This requires careful attention to data encryption and e-signature procedures to ensure data is not compromised during the process. However, dedicated cloud system operators have a strong vested interest in the security of their clients, and may actually be able to keep their systems more secure for much less expense than a large corporation could since this is all they would be focused on.
Data ownership is also hotly debated. Since the cloud company is actually storing the data does it belong to them or the client? This possible legal issue is still in the works.
For more on these issues and cloud computing visit dell.com.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.