Using Untangle to Secure Home Networks
With the spread of malware and spyware across the Internet and with the ever increasing risks of identity theft while searching and browsing the Internet, many home Internet users are looking for software packages that can help provide a barrier between them and the outside world.
Many may rely on their virus scan programs and other firewall programs to help ensure they are safe while browsing. Many wish however that they could have the same kind of enterprise level firewall device sitting between them and the Internet as most companies and larger corporations do. However, genuine firewall appliances and devices are usually tremendously expensive.
There is a gem of a product out there however called Untangle. Untangle is known as a Unified Threat Management device software and the great thing about it is that it is FREE! UTM is a buzzword in the security industry when it comes to security appliances because the term firewall doesn’t really describe everything that a device these days needs to do. Most enterprise level devices now do much more than just open and close ports. They need to be able to handle SPAM, Web traffic filtering, protocol level filtering, Adware and Spyware filtering, and many other functions and roles. Even at the corporate level, many companies have several devices in line that take care of the different roles. Untangle is much like physical security devices meeting virtualization and then some. With Untangle, you have virtual network appliances that handle many different roles as if you have multiple physical security devices handling those roles. Untangle handles it all along with impressive free modules that allow for great SPAM filtering, web filtering, phishing protection, ad filtering, spyware filtering, protocol control, and even has modules you can buy that extend the capabilities to interface with Active Directory and much more.
So all of these things are well and good. However, we are talking about home users here. We are going to take you through setting up an Untangle box that you can actually use to protect your home network from malicious Internet users and sites.
First things first. We need to install Untangle on a box. The really cool thing about Untangle is that you can install it into a virtual environment. If you have a box at home that you are not using that has some decent hardware as well as multiple NIC cards, you could install VMware’s free ESXi virtualization product to house your Untangle install. However, if you don’t have a box to do this, you can simply use a “whitebox” machine with a couple of gigabit Ethernet controllers to load and run Untangle.
A great resource to get started learning about Untangle as well as its requirements for installation and beyond is the Untangle Wiki. We won’t delve into the details of the requirements in this article.
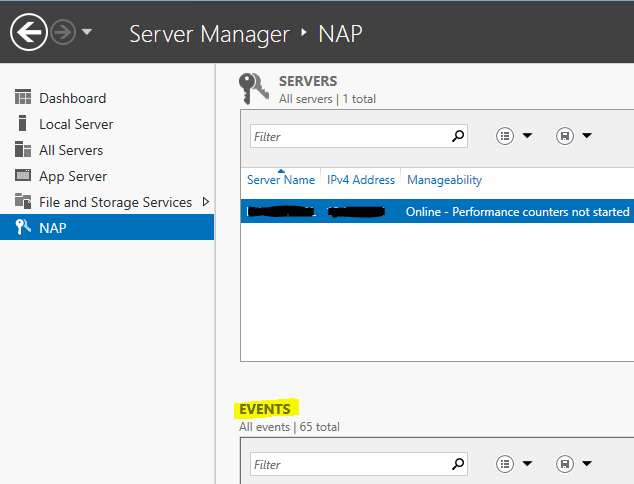
After you have installed Untangle on your machine or into a virtual environment, you need to configure the interfaces to direct traffic from your WAN connection to your LAN at home. If you are using a physical box for your Untangle installation:
- Setup your External interface with an appropriate LAN IP address. If your home network is using the Class C address space of 192.168.1.x for instance, pick an IP address out of this range for your external network adapter
- Setup your Internal interface to be a bridged interface connection to your external adapter
For our test environement here, we have Untangle loaded into a VMware virtual environment. The VMware box has two physical adapters. The virtual installation of Untangle has virtual NICs bound to each network card. With the virtual environment we staticly assigned each adapter to have its own IP address and one to be external and one to be internal. This is a slight variation of the physical install mentioned above.
After we have our interfaces setup to direct traffic through the box, we need to setup our client machines so that they send and receive traffic through the Untangle server. Most home networks run a consumer grade router that hands out IP addresses in a process known as Dynamic Host Client Protocol or DHCP. For our Untangle application, we want to disable using DHCP on our home router and enable it on the Untangle box. Use the internal adapter’s IP address for your gateway. This causes your clients to send all traffic through the internal interface and out the external and then through your router. Traffic will be able to run through the interfaces on your Untangle box which allows you to turn on filtering to protect your network.
You can supply a range that you feel comfortable with for your home network, however, most people will be fine with a handful of IP addresses in the address pool.
After your client has successfully pulled an IP address from your Untangle server, you should start to see some hits on the virtual appliances as you browse the Internet.