One of the cool things about having a home lab is being able to reach it from anywhere. Of course, when thinking about how you are going to make your lab accessible from the Internet, we always have to think about security and the implications of poking holes in firewalls and such. I wanted to share a few tips and tricks and software I have come upon over the course of time in securing RDP access to Home lab.
Securing RDP access to Home Lab
Ideally, arguably the most secure means to access your home lab would be to create a VPN tunnel to your network. With VPN you don’t have to leave an “always on” hole from the outside to inside your network. You simply establish the secure tunnel when you need. Also by doing this, malicious users from outside won’t be able to port scan and see that port 3389 or another port you have changed to is open from the outside. This is perhaps not possible in certain home lab environments or maybe not desirable. You may not want the requirement of having VPN software or VPN connections setup to make connections back to your home lab.
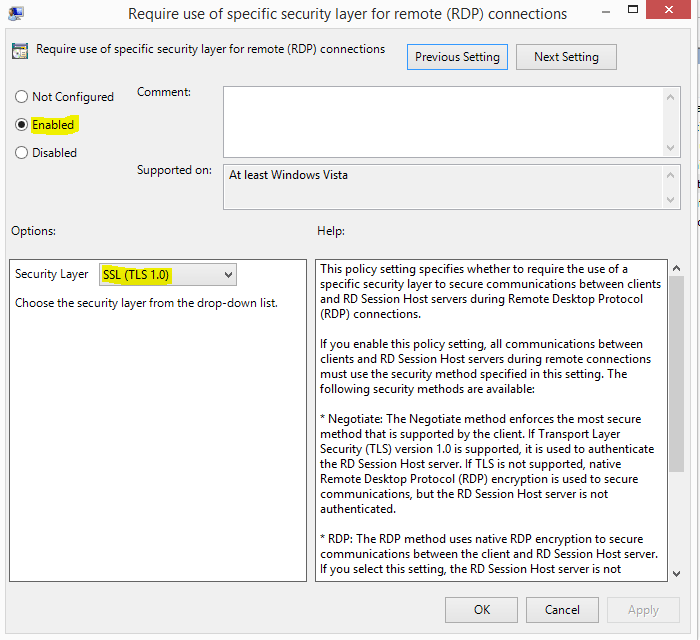
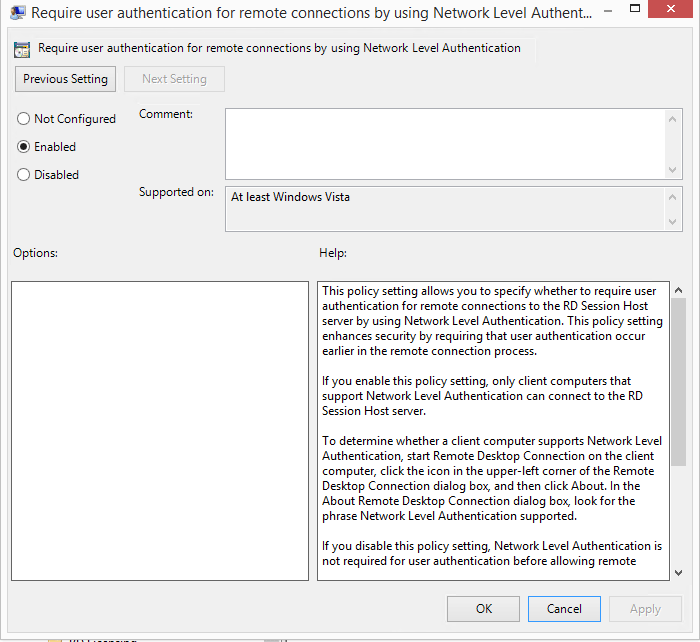
If this is the case, let’s take a look at securing RDP access to Home Lab connections that are always on. First things first, let’s look at securing RDP in general on a server/workstation. We want to set it to SSL/TLS and network level authentication to set the highest possible security right out of the gate.
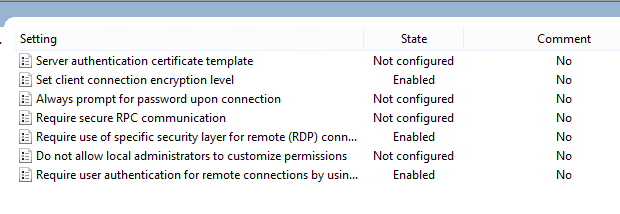
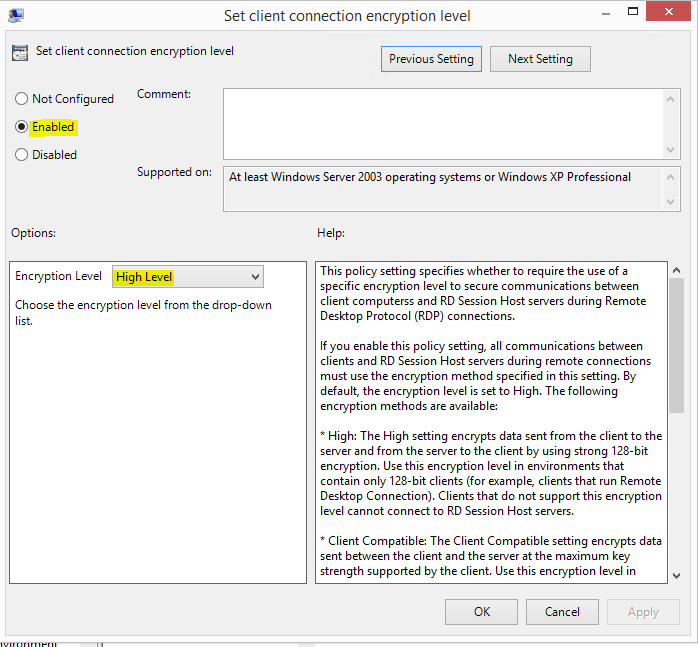
Launch the local group policy security management console. Type gpedit.msc. There will be (3) entries that you will want to set to enabled:
- Set client connection encryption level
- Require use of specific security layer for remote (RDP) connections
- Require user authentication for remote connections by Network Level Authentication
Detect and Mitigate Brute force attacks on usernames/passwords
There are several software utilities out there to help mitigate brute force attacks and secure RDP services. Most are pay for software. A couple that I have tried that work well are RDPGuard and LF Intrusion Detection. Both in the trial/freemium trim will block incoming attacks based on number of failed logins, how long to block, and even permanent blocking.
RDPguard works really well, however, is $79.95 for a license. With LF Intrusion Detection, if you are simply protecting a home lab machine, may be the one to opt for. There is a free version of the tool. The only caveat is that it only allows 20 permanent blocks in the free version. However, it will still temporarily block attackers trying to brute force your box. You can set the temporary block up to 90 minutes for a block period.
2 Factor Authentication
I use and evangelize to others just how good Duo Security is with RDP and other services. It provides a seamless integration to enable 2 factor authentication when making an RDP connection. It will send Push notifications to the phone of your choosing upon logging into Windows.
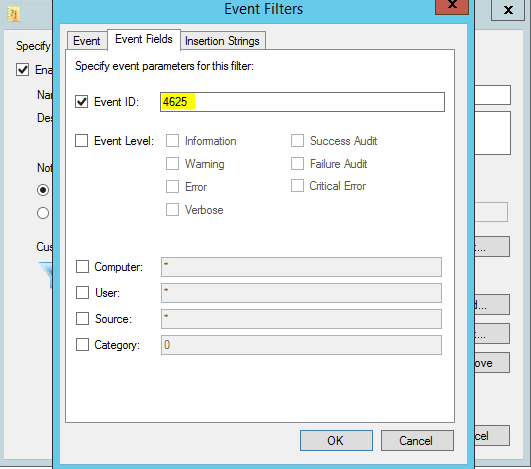
Auditing and Notifications
Netwrix provides a very nice little utility for free called Event Log Manager. You can easily setup a Log trap to trap event ID 4625’s which are failed logon events. The Event Log Manager will then email out in real time when it sees a certain event. This is really handy if you might start getting attacked and have a string of event 4625’s noting bad password attempts.
Final Thoughts
Securing RDP access to Home Lab connections is extremely important to securing the entire architecture of your lab. It needs to be thought through and monitored carefully. The last thing that anyone wants with their home lab is to have someone brute force a terminal server and wreak havoc inside the lab environment. Using the techniques and software tools mentioned above, you will go a long way in making sure your RDP access is secure.