I wanted to pose this question to the community. How many of you are doing outbound filtering in addition to inbound filtering at home?
I believe that outbound filtering is more critical than inbound filtering. Data exfiltration / theft, telemetry, spyware and malware connecting to command and control servers is the more likely attack vector. The mobile app industry has normalized very unsavoury practices and business models and unfortunately this has started to also become the norm in desktop/server OSes and software.
Even tools like the Hashicorp suite have telemetry enabled by default. I'm sure it's benign but I feel it erodes trust to feel entitled to help yourself to somebody else's data.
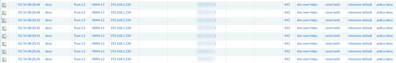
I have process-level default deny outbound filtering on my Windows workstations and mobile devices. I also make use of DNS filtering on my network and homelab. Unfortunately DNS filtering is compromised now that software can trivially bypass the system resolver and use DNS-over-HTTPS to disguise DNS lookups and prevent inspection.
i'm not doing any outbound filtering, however i am using Security Onion to monitor all outbound traffic. it generates reports and alerts on suspicious traffic. i haven't tuned it much (there's a lot of noise i need to filter out), and i also need to set up actual email/push alerts. it's been an interesting tool to check out.