Not long ago, we covered the release of NAKIVO Backup & Replication v10.4 Beta which contained great new features in the realm of cybersecurity for your backups. NAKIVO has now released v10.4 as GA which means the features are now fully supported as a general release. It means that customers can now upgrade their production systems to include the new features and the trial version is now v10.4 as well. Let’s take a quick overview of NAKIVO Backup and Replication v10.4 GA released for download.
Why Cybersecurity features are important with backups
Cybersecurity is a major topic all the way around when it comes to business-critical data. Major ransomware attacks, such as the one that hit Colonial Pipeline, are making headlines and companies should be noticing. Ransomware can quickly infect your business-critical data, both on-premises and in the cloud.
Attackers realize that if they can target backup files along with normal data, they have a much better chance of businesses paying the ransoms demanded. Backup vendors have had to take the threat to backup data seriously and figure out ways to ensure that production backups are protected from malicious processes that may try to either delete the backups or encrypt them along with the other data.
There is no question that ensuring both the backup solution itself is secure and only authorized individuals have access and also the backup repositories themselves are protected.
With Amazon AWS S3 storage, a special type of attributed was introduced called object lock. Note the description from Amazon regarding object lock:
Amazon S3 Object Lock is an Amazon S3 feature that allows you to store objects using a write once, read many (WORM) model. You can use WORM protection for scenarios where it is imperative that data is not changed or deleted after it has been written. Whether your business has a requirement to satisfy compliance regulations in the financial or healthcare sector, or you simply want to capture a golden copy of business records for later auditing and reconciliation, S3 Object Lock is the right tool for you.
This idea of immutable storage has now carried over to backup solutions as it provides the perfect use case for protecting your business-critical backups. Even if someone has the permissions to delete the backups, the immutable flag prevents this from happening until the date specified.
NAKIVO Backup and Replication v10.4 GA Released for Download
After a few weeks of the beta release of NAKIVO Backup & Replication v10.4, NAKIVO has now released v10.4 as a GA release ready for production. It provides
Three new features are found in the v10.4 release of NAKIVO Backup & Replication that primary focus on protecting your backups from ransomware. There is an additional feature released regarding Nutanix AHV to note as well that was not covered in the previous v10.4 Beta release post. Those features include the following:
- Immutable repository
- Two-factor authentication
- Instant granular recovery for Nutanix AHV
Let’s briefy get an overview of these new features to understand what is offered in NBR v10.4.
Immutable Repository
Tying into the description earlier of immutable cloud storage, NAKIVO has integrated immutability for backups and backup copies sent to a Linux-based repository. The immutable repositories that are now a part of NAKIVO Backup & Replication v10.4 allow setting the immutability flag on the retention settings of a particular backup or copy job.
Using the Immutability flag, you specify the number of days the recovery points cannot be deleted.
Two-factor authentication
Compromised credentials are often the culprit of widespread data breach and ransomware events. When an attacker compromises credentials of a legitimate user, they do not have to “hack” their way in. Instead, they simply walk through the front door of the system with legitimate credentials.
In the Colonial Pipeline attack, a set of compromised VPN credentials was the vehicle used by attackers to launch the ransomware attack that brought down 45% of the U.S. fuel supply to the Eastern Seaboard. It is scary to think that a simple username and password could have such an effect. However, this is often the reality of cyberbreach events today.
Compromised credentials containing known passwords are fairly easy to come by. The one that may have led to the breach of Colonial Pipeline could have been a recent database of some 8.4 billion passwords.
Multi-factor authentication and specifically two-factor authentication is a great way to bolster the security of business-critical systems, including backups. With two-factor authentication, a user has to prove their identity by “two factors.” This includes both a password AND another identification method that is generally a one time passcode generated by a mobile app or sent via a text message.
It means that even if an attacker has stolen legitimate credentials with the correct username and password, they still do not have the full authentication components needed to successfully authenticate.
Nutanix AHV Instant Granular Recovery
Additionally, with this release, one additional major feature has been added that Nutanix customers will be happy about. With NAKIVO Backup & Replication v10.4, Nutanix AHV environments can instantly recover files and application objects for
- Microsoft SQL Server
- Microsoft Exchange
- Active Directory
This allows performing granular recoveries of application data as needed, greatly reducing the time to recovery. Additionally with the backups of Nutanix AHV provided, customers can recover immediately to the original VM or a different VM altogether. Exporting the data is also possible with the feature set provided by NAKIVO.
Updating your NAKIVO virtual appliance to v10.4
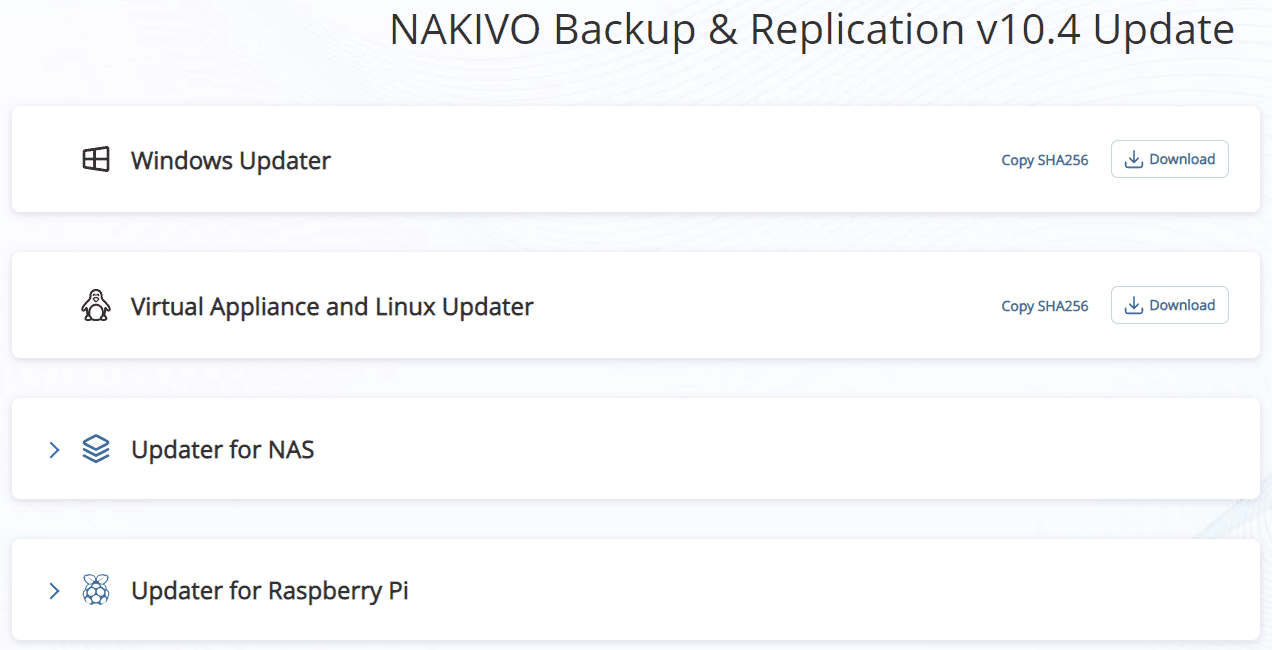
The process to update your NAKIVO appliance is straightforward. Note, when you update your appliance, make sure you have all jobs quiesced before started. The NAKIVO services will be restarted in the process. Download the appliance update script from NAKIVO here:
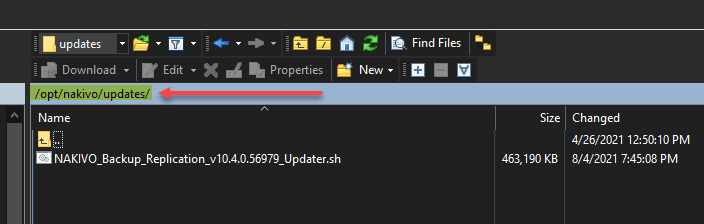
Copy the file to:
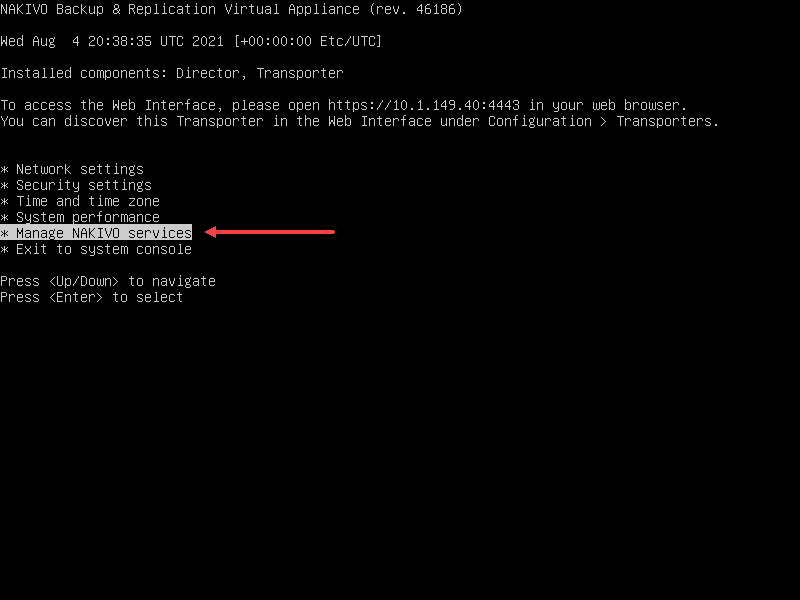
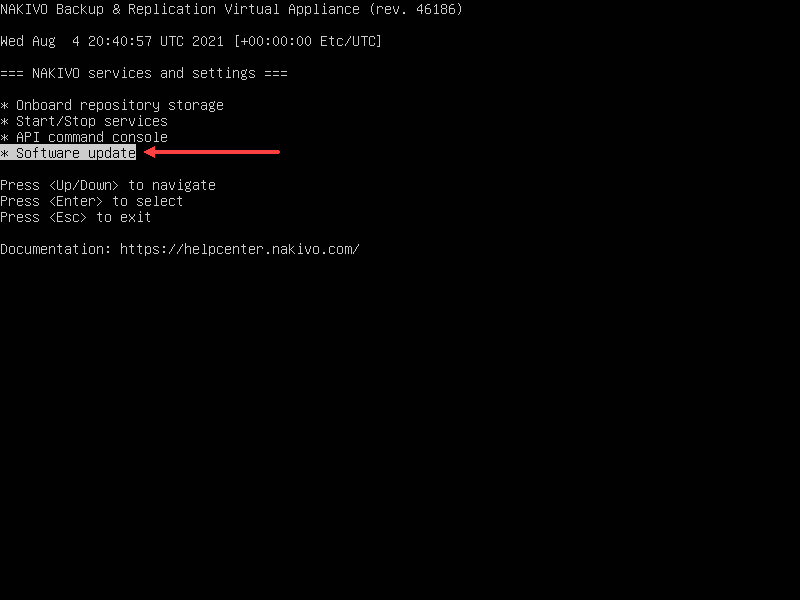
/opt/nakivo/updatesLaunch the console session in your hypervisor environment. Here I am using vSphere. So, open the Remote Console connection and select the Manage NAKIVO services option.
Select Software update.
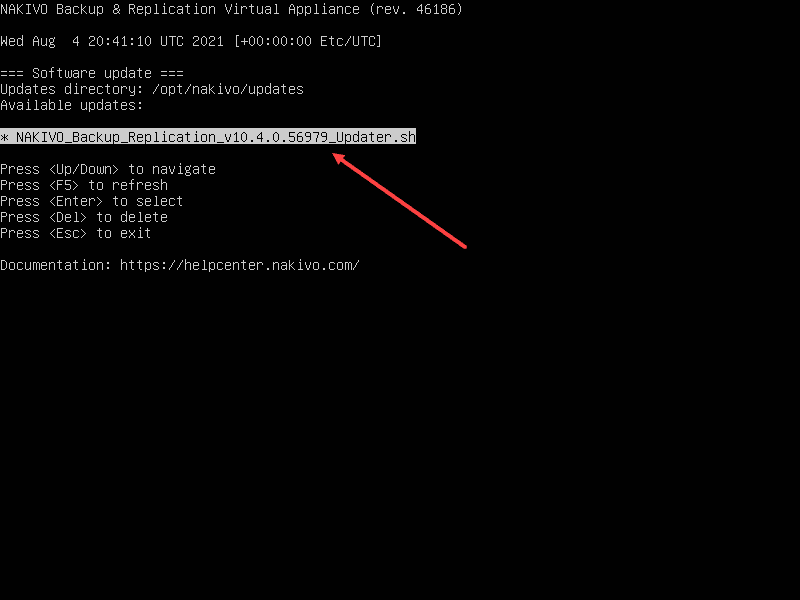
Select the software update script that you uploaded earlier.
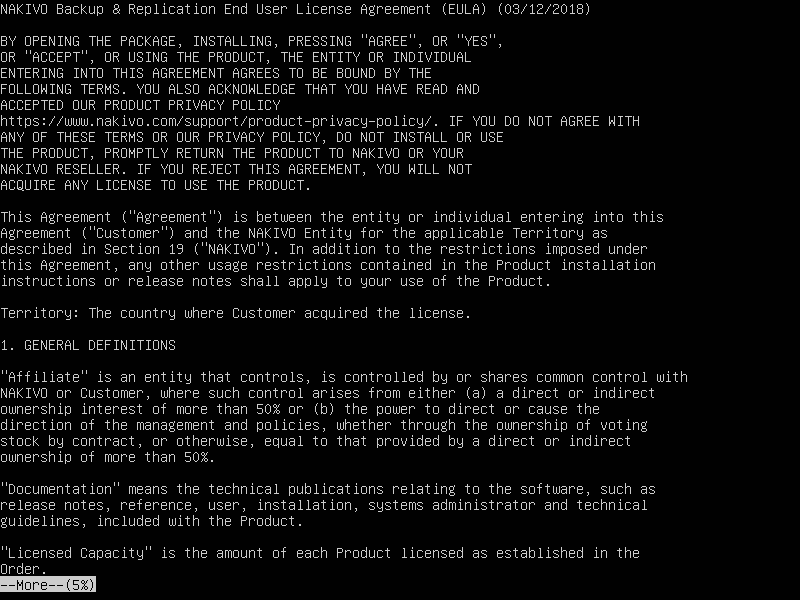
Scroll through and agree to the EULA.
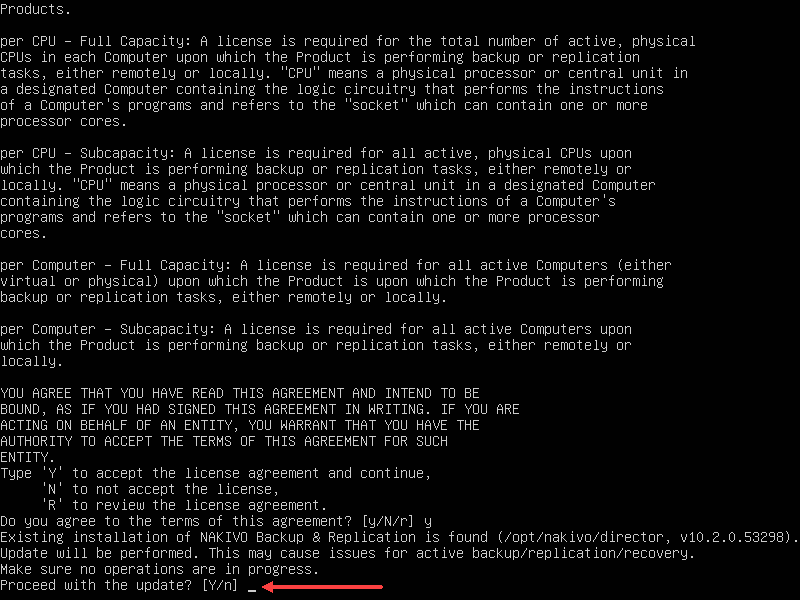
When prompted to Proceed with the update, select Y.
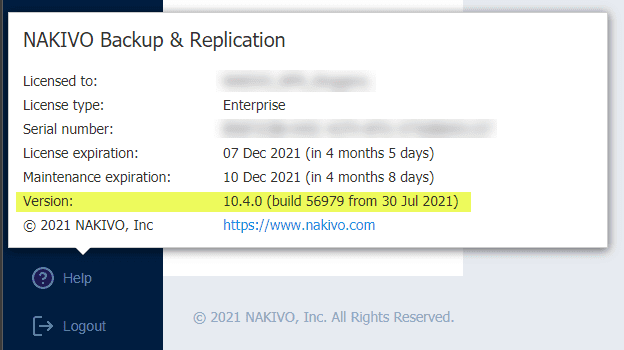
The update script will run and apply the update to your version of NAKIVO. After just a bit, your appliance will go back to the console menu. It will restart the NAKIVO services so it may take a minute for these to restart. After you can log back into the Web console, navigate to Help > About and check the Version listed. You should see 10.4.0 listed.
Wrapping Up
The news of NAKIVO Backup and Replication v10.4 GA Released for Download is great for customers to introduce the latest and greatest security features in their NAKIVO environment. The new immutable repository and two-factor authentication are great protections against ransomware infection that can destroy even your backup data. The additional Nutanix features are also a great addition to this release.
Check out more about NAKIVO and download the latest v10.4.0 release here.
Take a look at our other NAKIVO posts here:
- NAKIVO Backup and Replication v10.3 Beta New Features Download
- How to Recover from a Ransomware Attack with NAKIVO
- Backup Microsoft Office 365 for Remote Workers with NAKIVO
- Backup and Restore OneDrive for Business with NAKIVO
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.