One of the new exciting features that was introduced with vSphere 6.5 is the encrypted VMs feature. Security these days is on everyone’s mind and encryption provides a solution to many security concerns. What happens if someone gets a copy of the raw VMDKs of a sensitive VM? They can then take those files and mount it on their on VMware server and have access to the data. Also, not just data at rest, but data in motion, vMotion that is. In steps encrypted VMs. Those files are worthless without the encryption key provided by the encryption key server. Also, the encrypted VMs feature allows for encrypted vMotion. Let’s look at VMware vSphere 6.5 configure encrypted VMs.
VMware vSphere 6.5 Configure Encrypted VMs
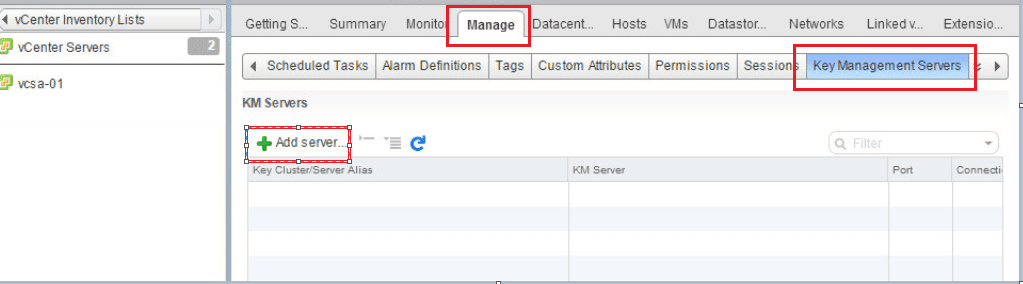
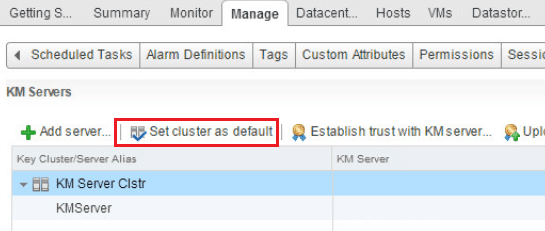
The first step in deploying Encrypted VMs is to point vCenter to a Key Management Server. In your vCenter server inventory list, click Manage >> Key Management Servers >> Add Server.
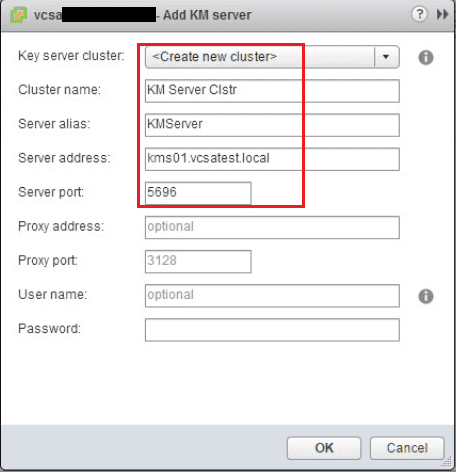
Fill in the information for your cluster name, server alias, server address, and server port.
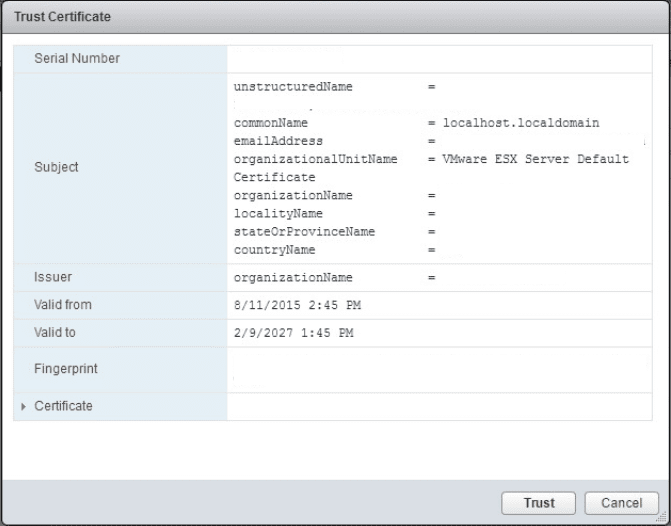
Once you click OK you will see a security dialog asking you to trust the certificate.
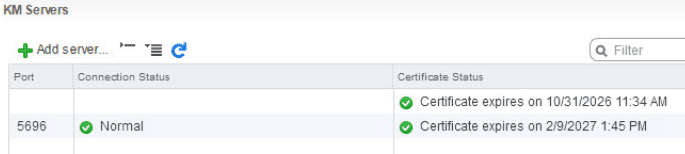
Once added, you should have green checkboxes next to the Certificate status.
Now under KM Servers we set a default cluster.
Creating an Encryption Storage Policy
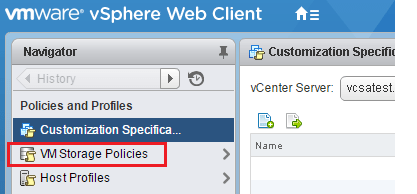
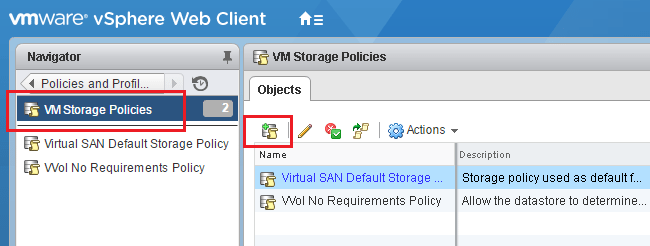
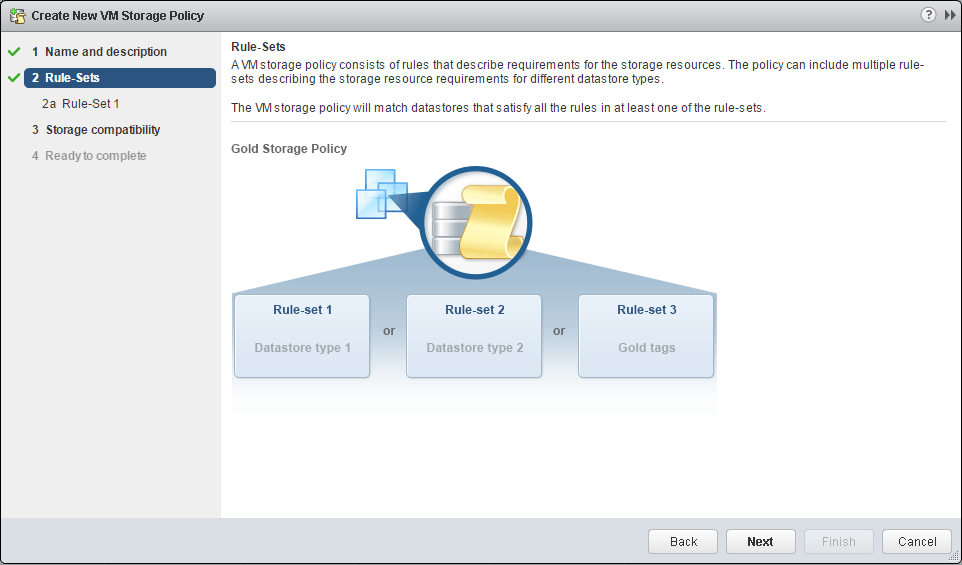
The next step in the process is to setup an encryption storage policy.
Add a storage policy.
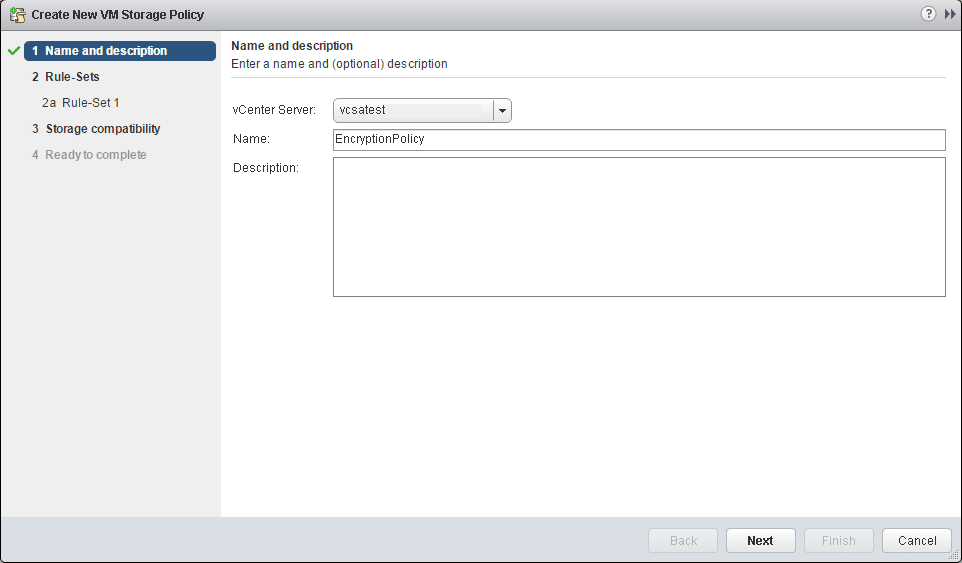
Name the policy.
Simply next through the next informational page.
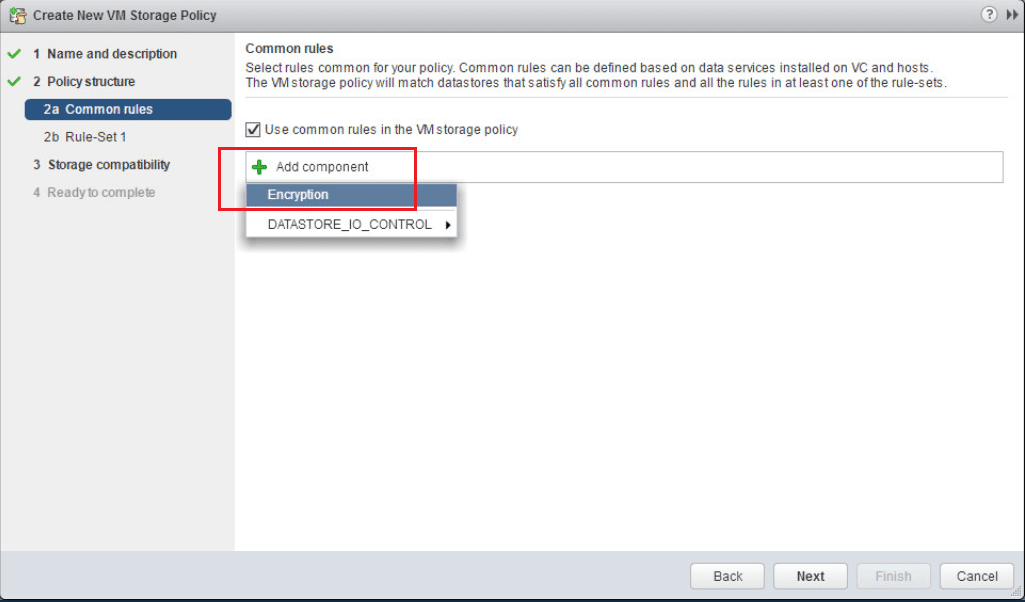
Under common rules, click the Use common rules in the VM storage policy. Then select to Add Component. Then select the Encryption option from the dropdown, but don’t click next yet.
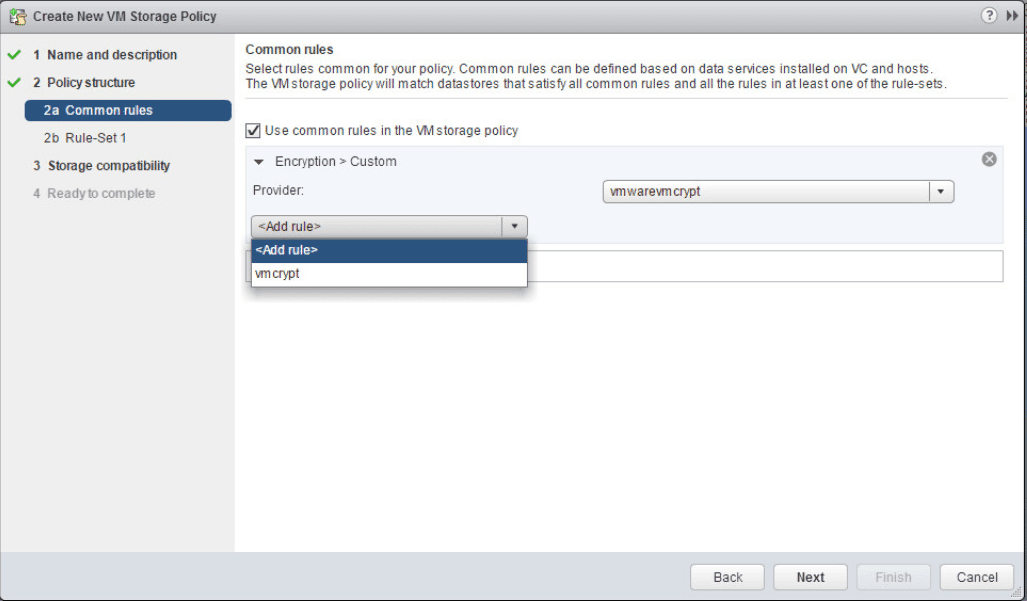
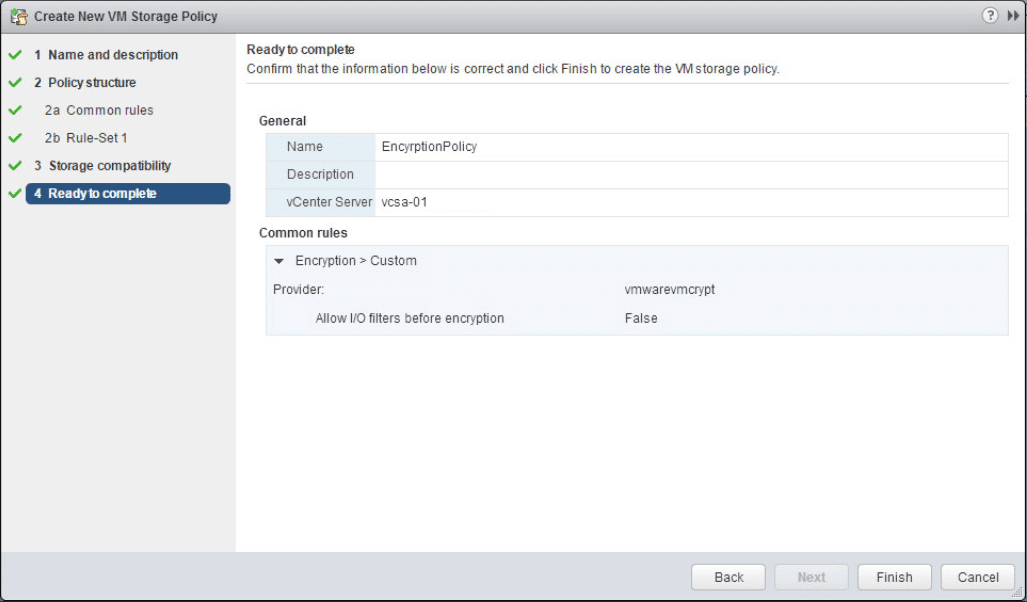
Under the Add Rule select the vmcrypt option.
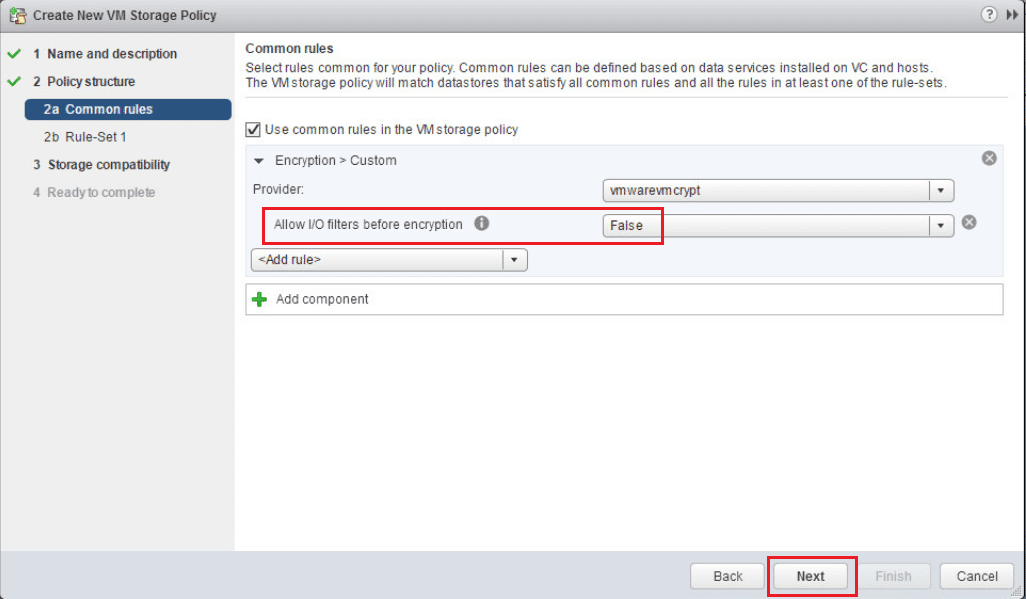
Leave the Allow I/O filters before encryption set to false.
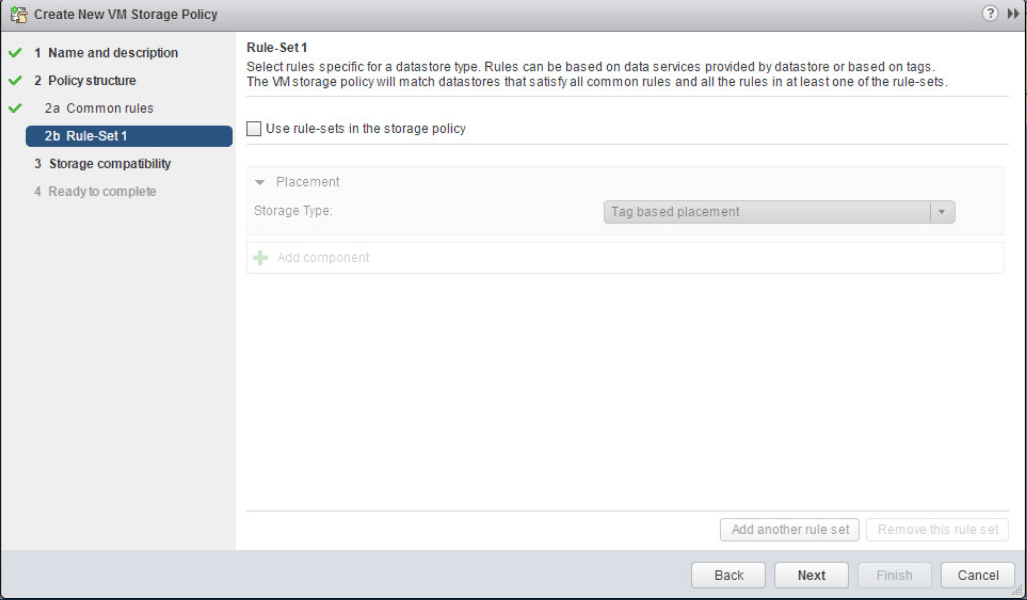
Uncheck the Use rule-sets in the storage policy.
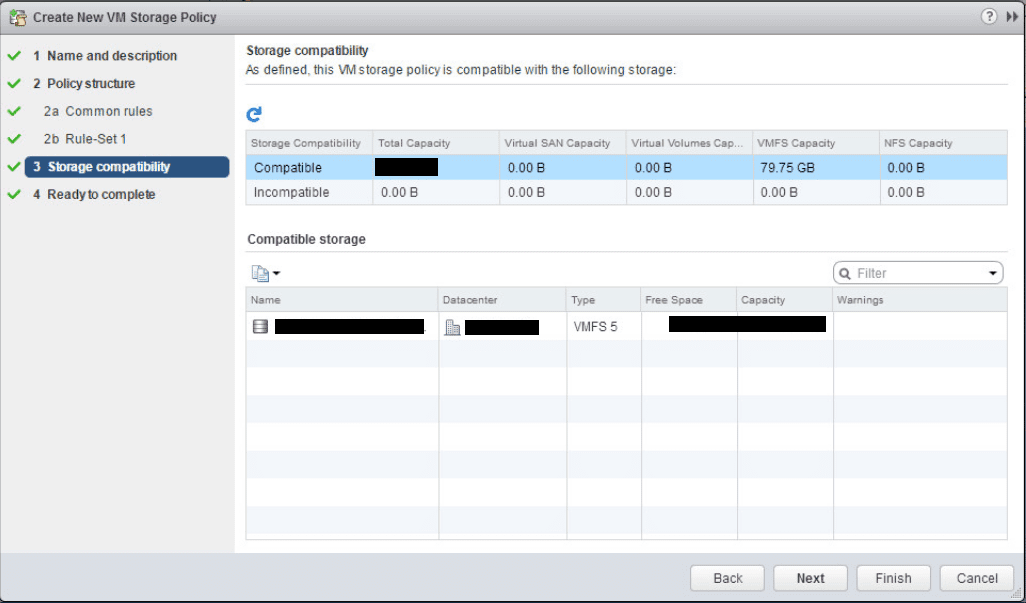
The next screen shows the storage compatibility check.
Click Finish to create the encryption storage policy.
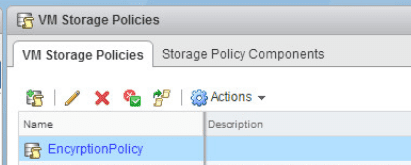
We can now see our EncryptionPolicy listed in the available VM storage policies.
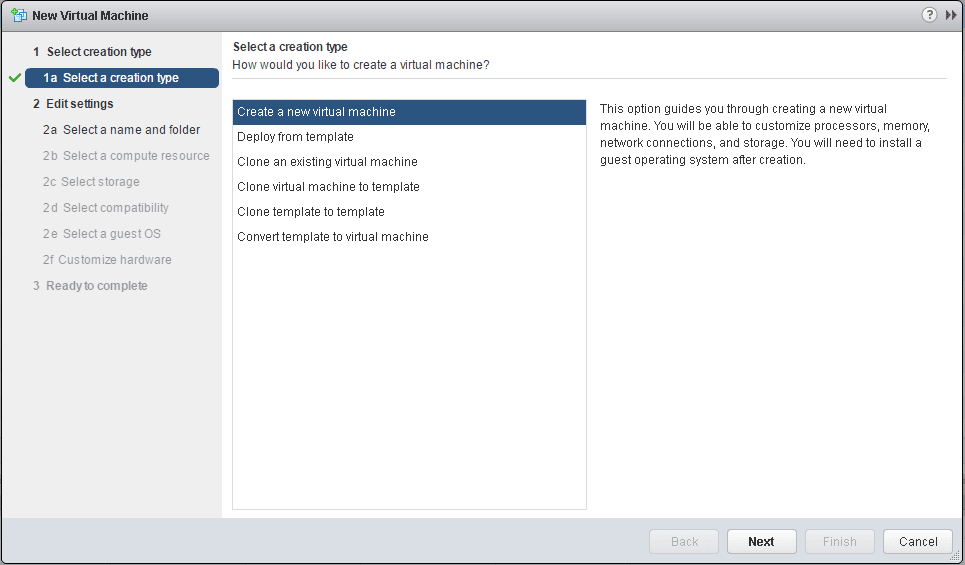
Create an Encrypted VM
The last step is to actually create an encrypted VM.
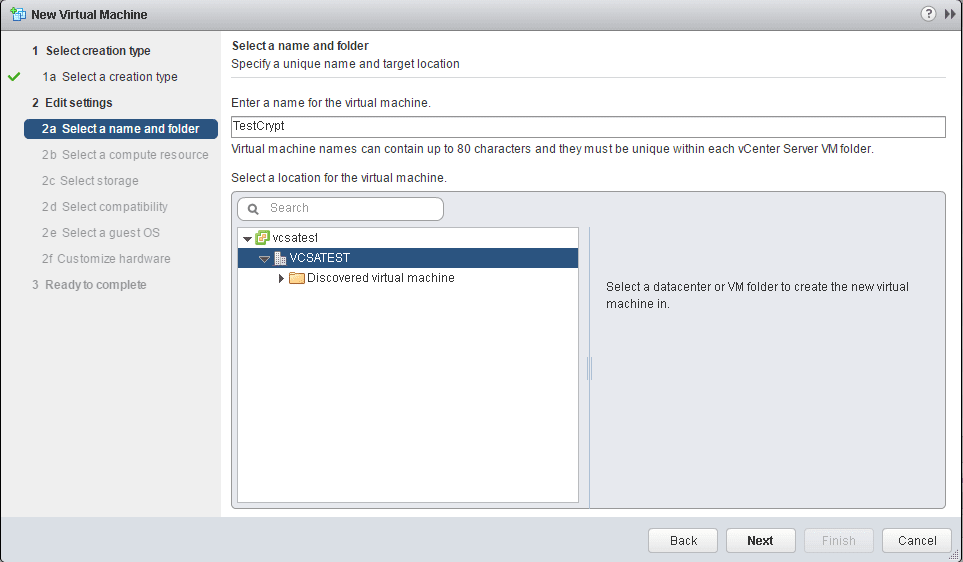
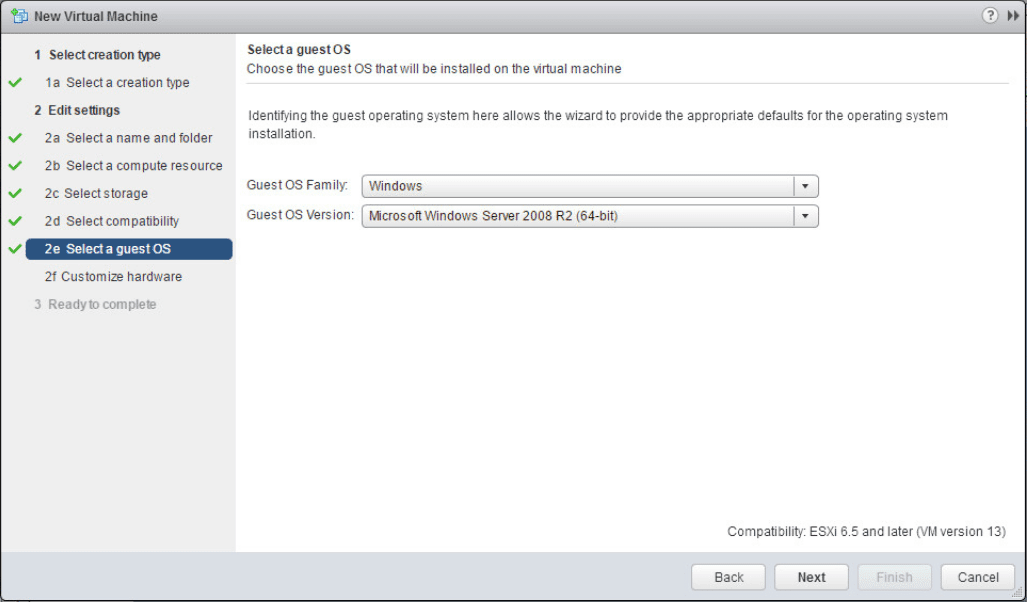
Select the name and folder.
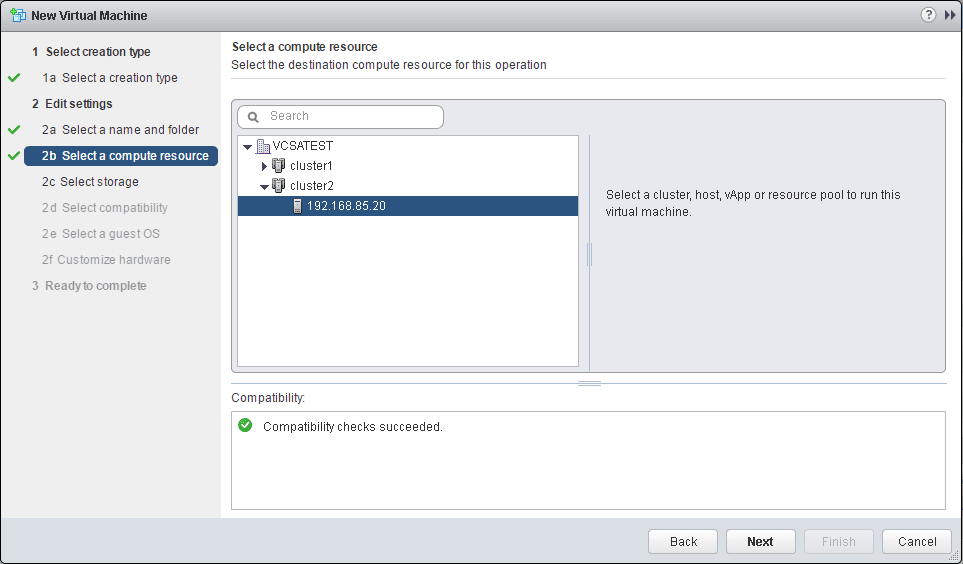
Select a compute resource.
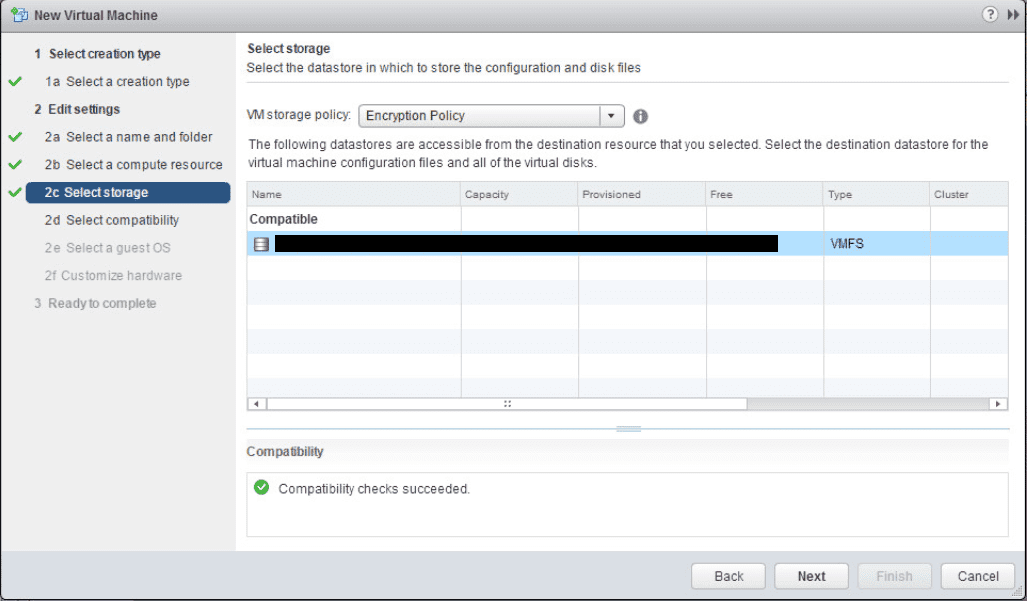
Here is where the new options come into play. We can now select our Encryption Policy from the VM storage policy dropdown.
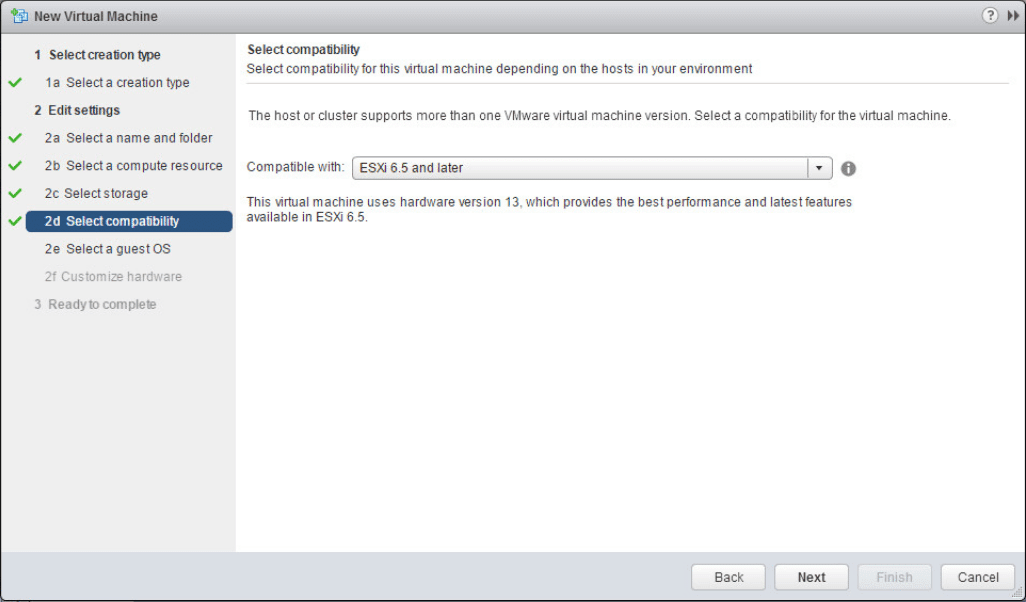
Leave the compatible with setting set to ESXi 6.5 and later.
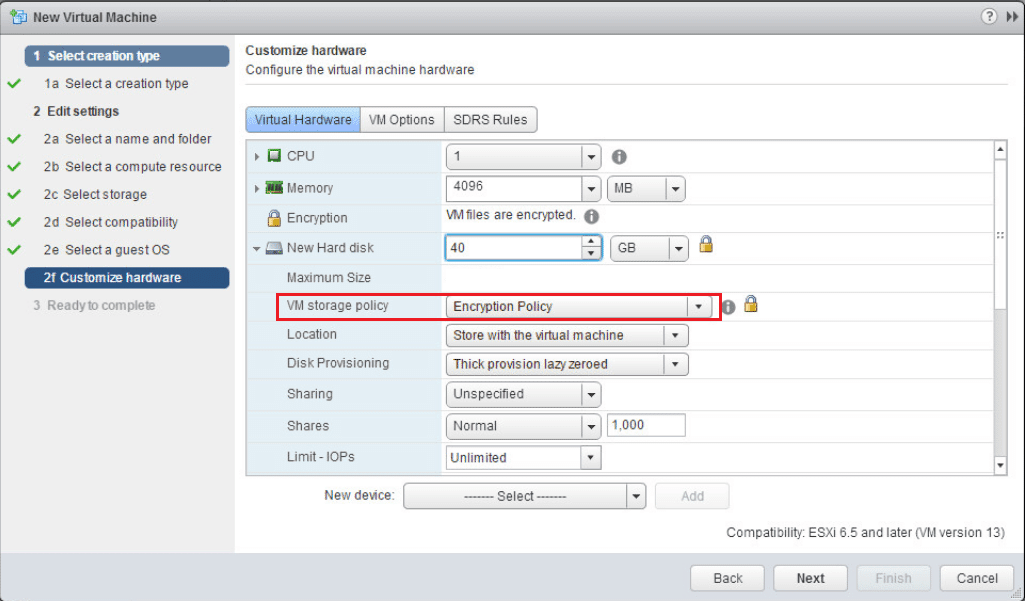
When you expand the hard disk for the VM, notice how the VM storage policy shows the Encryption Policy.
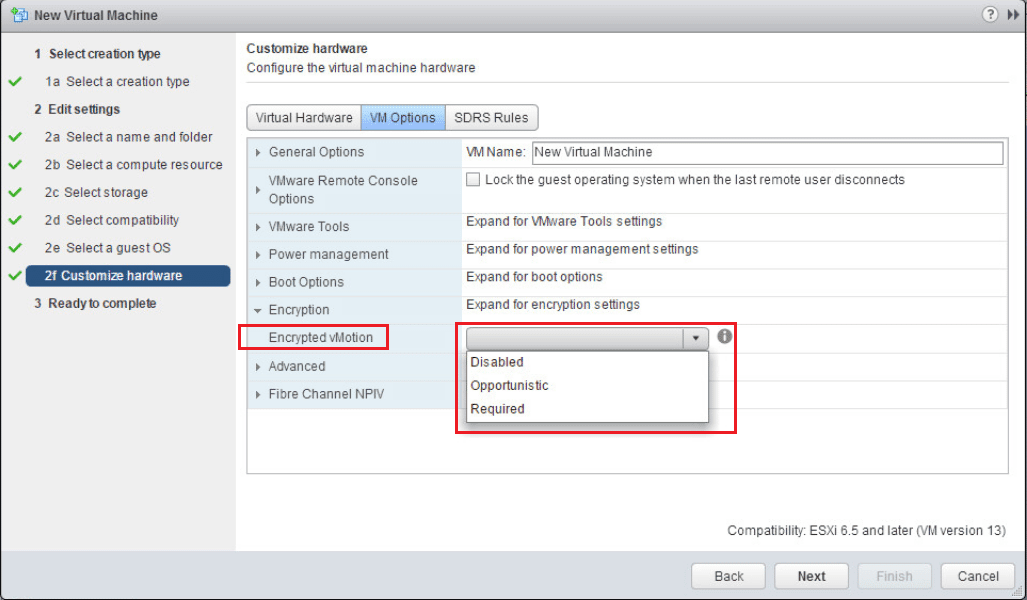
Also, a really cool feature is Encrypted vMotion. We can set the setting here to determine how the VM handles vMotion to another host. There are three options here:
- Disabled – Do not use encrypted vMotion
- Opportunistic – Use encrypted vMotion if the destination host supports it, otherwise use normal vMotion
- Required – The vMotion process with this VM must use encrypted vMotion. If the vMotion operation doesn’t support encryption on the destination host, the vMotion operation will fail.
After the above configuration screen, simply hit Next and Finish at the Summary screen.
Thoughts
The process for vSphere 6.5 Configure Encrypted VMs is very straightforward within vCenter. This is an exciting feature that will give administrators the ability to provide an additional layer of security to their data and the VMs themselves. The new vSphere 6.5 release is looking like a very worthy upgrade in terms of features and functionality.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.