Starting with IIS 7, Microsoft made major changes to IIS. The look and feel of the entire interface is way different than what administrators were used to with IIS6. All in all most of the changes have been a good thing. Managing certificates in IIS7 + 7.5 is actually pretty intuitive and easy to do. Most everything is wizard and menu based which makes managing certificate details much easier when you aren’t having to worry about syntax. When it comes to running multiple SSL or port 443 enabled sites in IIS7 and above, we do have to break out the command line for some configuration when it comes to host headers and the use of this port. Before we get into the particulars of enabling SSL for a site, we need to understand how IIS7 + deals with ports.
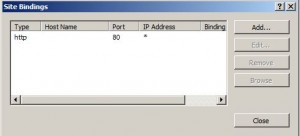
IIS 7+ does this by the use of “bindings” which refers to which ports and configurations are “bound” to a certain website.
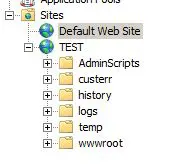
We find the above menu, by simply clicking on a particular website found in our management tree on the left. Once we click on “Bindings” we see a very minimalistic box that allows us to see and modify bindings to a particular site.
As you can see above, we only have port 80 bound and have the option to “Add” a binding. If we click on one of the listed bindings, we then have the option to “Edit” and “Browse.” Remove is only available if you have more than one binding.
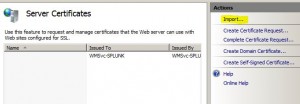
Now that we understand how ports are bound to certain websites, let’s look and see how certificates are managed in IIS7+. Before port 443 can be bound to a website, we must have a valid certificate in place to use. In order to manage the certificates for our server, we simply click on the server name in our management tree in IIS and then we have the option in the right hand pane to manage “Server Certificates.”
In our case here, we are using a Godaddy Wildcard certificate for our webservers, so we need to Import this certificate so that our server will be able to use it to bind to port 443.
Prerequisite Steps
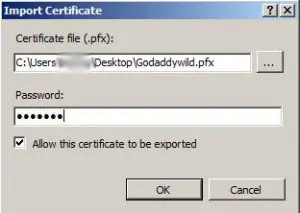
For our example in this post, we have already imported the Godaddy wildcard certificate to another IIS7 box in our environment. The process to import this certificate into our other server involves exporting the certificate along with the private key to a .pfx file and having our password that we used available and ready as we will be prompted for this during the import.
So once we have clicked the “Import” button, we have the “Import Certificate” box:
We have copied the .pfx file certificate to our desktop to be available for import.
So after the import process, we see the server certificate available to us in our “Server Certificates” screen:
Adding the SSL Binding to the website:
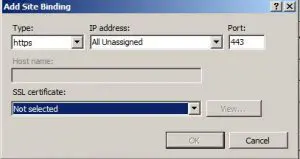
After we have the certificate in place, we can then add the 443 SSL binding to our websites. Navigate back to the Site bindings menu that we detailed earlier and view your bindings. We will be “Adding” a binding to the site.
Notice in the “SSL Certificate:” box, it is still “Not selected.” You will need to pull down the drop down box and select your SSL certificate that you imported using the process above.
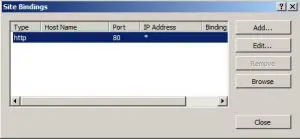
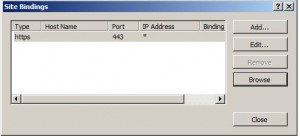
After adding the SSL binding, we went ahead and removed the port 80 HTTP binding from our site as we only want it to respond to port 443. Your bindings at this point should look something like this:
Starting the Websites and multiple Bindings:
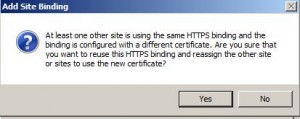
After you have gone through the above process on at least one website and run through it on another site, you will receive the following message when trying to bind 443 to another website, IIS lets you know that there is another website using this binding and certificate. Simply answer Yes to the message box.
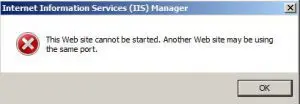
At this point if you attempt to start an additional port 443 website you will receive the following error
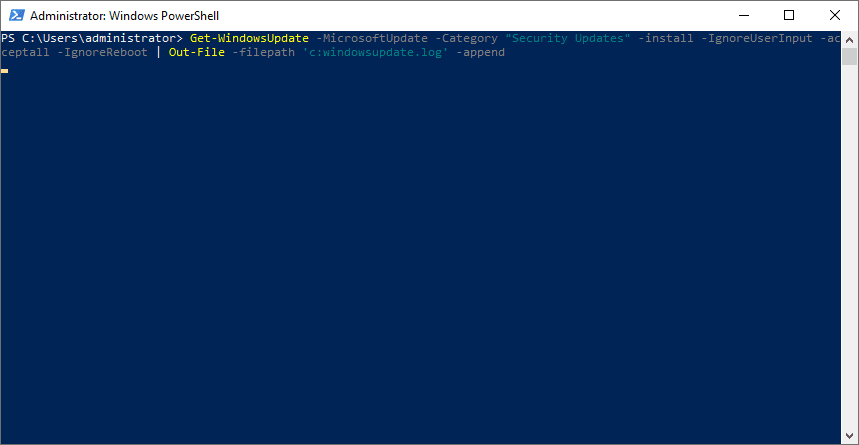
Using the command line to set the host information for the binding:
Here is where we need to employ the command line, as you cannot edit the host information for the binding if it is an HTTPS port binding.
- Open a command prompt and change to the directory: %WINDIR%\system32\inetsrv
- Using the “appcmd” utility we can add the 443 binding and host information to all the websites we need….replace the information below with your site details and host information
- appcmd set site /site.name: “Test1” /bindings.[protocol=’https’,bindingInformation=’*:443:’].bindingInformation:*:443:test1.test.local
- Repeat the command for every website that you want to add host information to the 443 binding
Along with the command above, DNS host records will need to be added that point to all the hostnames we create using the command above. Once the sites are configured with the host information, IIS will not complain about starting all the websites that are pointed to the same port.
Final Thoughts:
All in all the process is straightforward to add the SSL binding to a website in IIS7 or 7.5. Knowing the tricks of how to add the additional bindings makes life easy for an administrator needing to run multiple sites using the same SSL binding.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.







Great!! This worked for me!
Maybe you/reader can help me. I have 3 websites: aaa.my-domain.com, bbb.my-domain.com and ccc.my-domain.com all using a single wildcard certificate *.my-domain.com. That certificate expires in a month and I have a new wildcard certificate *.my-domain.com on my server ready.nnI want all those domains to use the new wildcard certificate without noticeable downtime.nnIt posted this as a question on StackExchange too. If you can help me, you could answer there and earn points. http://serverfault.com/questions/610841/replace-wildcard-certificate-on-multiple-sites-at-once-using-command-line-on-i
This does not work for me. I have 2 websites (separate domains) running under IIS 7.5 and I have 2 SSL certificates, one for each of them. I followed these instructions and IIS has no problem starting both sites, but when you go to one of them it throws an error saying there is something wrong with the certificate and the other just isn’t secure.
My question is this. Are these instructions good for single SSL certificates, or are they good for only wildcard certificates and SAN certificates.
Most places say what I am trying to do is not possible (networksolutions.com says it is possible), but I find it difficult to believe that I can run as many websites as I want but only one can be secure. I have already purchased the 2 SSL certificates, I cannot use wildcard certificates and I do not want to spend the money for a SAN certificate for only 2 domains.
Any ideas?
David,
Are you using a single IP address for both sites? If so, I believe your issue is the multiple domains in this case. IIS 7.5 doesn’t support SNI or server name indication. SNI is a TLS extension to include a virtual domain as a part of SSL negotiation. This means the hostname for each website can be used to identify the network endpoint if you are using a single ip address. This wasn’t supported until Server 2012 with IIS 8.
A workaround would be to bind another IP address to your server and split off the sites between the two which should allow the SSL negotiation to work properly. Hope this helps.
Thanks Brandon. I suppose that could be more clear in the article, but it isn’t just this one article. There seems to be quite a bit of ambiguity on this subject.
Anyway, I have begun to do as you suggested. I have 2 ip addresses now on my server. however I do not know how to get the web traffic through my router to the correct ip address.
I have 2 domains that are mapped via DNS to one public IP address. All that traffic goes through my ATT router and on to my NetGear router which then forwards both port 80 and 443 to my webserver which now has 2 ip addresses. The problem is that I have don’t know how to get one domain to go to one server and the other domain to go to the other server.
The ATT router on GigaPower service is of no use. It is proprietary and does not do port forwarding well at all so all traffic has to be forwarded to my NetGear as a DMZ. Any help would be greatly appreciated.
BTW, I do have more than one static IP address that I could use, but I don’t know how it could help.
David,
If I am reading your response correctly, you won’t be helped to have the 2 IP addresses internally if your outside DNS only forwards to one IP address of your router. Then the router forwards internally. The only way to distinguish PAT on a single IP address in this configuration would be to use different ports and you won’t want to do that most likely. In other words the router on the outside wouldn’t know how to distinguish between port 80/443 for one website vs the other website you are hosting internally.
It sounds like the catch here is you have a managed router from ATT that you can’t access? Is that correct? When you say you have more than one static IP address you can use, are you referring to external IP address? If so, you need to put an additional IP address in use externally, change your DNS for one site to point to one IP and the other to point to the other IP, and then port forward one address to one internal IP of the webserver, and port forward the other address to the other internal IP.
Internally, the webserver would handle the traffic correctly. However, it sounds like the challenge here is the external configuration, managed router, etc. ATT should be able to do the external work for you if this is a managed service.
Let me know if I am not reading this correctly.
Thanks David,
Brandon
Thank you Brandon. You are reading my issue correctly. I will be looking into gaining access to the ATT router to see if it supports multiple external IP addresses and then port forward them to my internal, which I may have to get a new router that does. Thanks s much for your help.