So I wanted to throw a quick blog post out there on Powershell script signing the easy way. This is a little bit tongue and cheek on the post as I don’t want to detail how to sign powershell scripts but rather how not to have to do this. Let’s see how we can run scripts that you need automatically, and still maintain the powershell security on your box that you need. If you have looked into powershell script or code signing, you will see that it is fairly involved even if you use a self signed certificate. So how can we “sign” a script so that we can run it?
Powershell script signing the easy way
Well, the answer is that we don’t sign it. By using a scheduled task, we can essentially do what we need to do, bypass the executionpolicy for a particular script and leave security in place – all without signing the script. This is especially helpful if we are running this as part of an automatic job, etc that we want to run without user intervention.
Many forget when they need to automatically run powershell code that with a scheduled task you can pass the appropriate flags without having to call the script from a batch file, or some other means which often doesn’t work correctly. In the batch/cmd file of your choosing, you literally set the execution policy, run your script, and set the policy back. However, this can get messy.
Scheduled Task
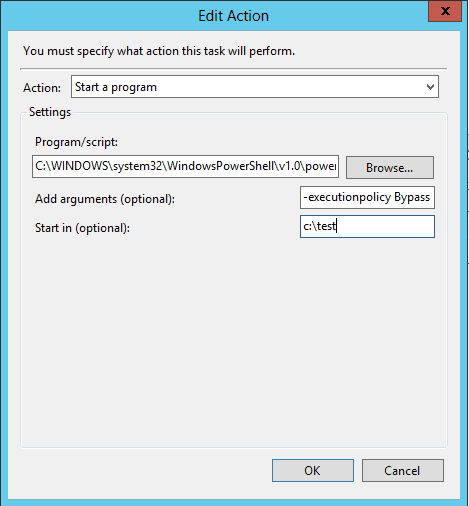
By utilizing a scheduled task and the arguments field, we can pass the appropriate flags to bypass the execution policy on a particular script. The scheduled task Action properties will look something like the following. Notice the Program/script section is calling the powershell executable.
C:WINDOWSsystem32WindowsPowerShellv1.0powershell.exe
Next let’s look at the Add arguments (optional): field. This is where we do all the heavy lifting. Note below, we set the executionpolicy to Bypass and then feed it the .ps1 file.
-executionpolicy Bypass -file c:myfoldermy.ps1
The scheduled task action will look similar to this:
Final Thoughts
Signing scripts is certainly a good idea when thinking about the total security implementation with Powershell. However, we can do “powershell script signing the easy way” by simply bypassing the powershell executionpolicy as we call the script.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.