We have covered this situation before with malware and profiles in a different post. However, we thought it good to cover this topic again since in a roaming profile environment, this issue is likely to pop up again and and again. When you have a user who has a malware infection and they also are utilizing a roaming profile, oftentimes, the infection gets copied to the server side location which is an issue because even if you clean the infection off at the local profile/machine location, there is a good chance, the infection will be copied right back down to the local machine when the user logs in again because of the way roaming profiles work. There are definitely considerations that must be made when this is the case.
First things first, you need to get the computer itself clean. The best way to do this is to have another local administrative user that has admin rights to the files and the machine itself. This will allow you to have control over the rest of the process without having to use the infected user. All malware is different and oftentimes there are different procedures for eliminating different variants. So Google is your best friend here. Determine which variant of malware you are infected with and then go about finding the specific steps to eliminate it. In general terms, most malware infections can be eliminated by booting into safe mode and then running a malware eliminating program such as Malwarebytes to get rid of the infection(s).
After you have run a program to eliminate the infection, we are now ready to start dealing with the profile issue. Often, you can determine if there is damage to the profile itself pretty quickly. Many times you can get rid of the malware infection, but if the profile is damaged, you will see residual effects such as file associations being lost. I had a user the other day that once we removed the infection, all .exe files and such would not open and were asking to be associated with a program – so on and so forth. You CAN spend the time to repair all of the file associations and try to make sure there aren’t any additional issues after the fact. However, I have found that in lieu of time, as our time is valuable as admins, it is often easiest to back up their old profile so that pics, documents, etc, are not lost and then start over. Many times, Windows is fine, it is just the profile that is hosed.
Profile backup and cleanup
Starting with Windows Vista, the profile location is found at c:\users\%username% so this is where you want to start your process of getting the computer cleaned up. What I like to do is log in as the local admin as mentioned earlier that is separate from the user with problems, make a backup copy of the profile. This can simply be done by copying their profile folder and pasting it back down in the c:\users folder. Also, login to the server location and rename the roaming profile folder to something like %username%_backup or %username_old or whatever you might choose.
Note, in order to do this on the server side, you most likely will have to take ownership of the profile folder since Windows sets these up with explicit permissions given only to the user and system in most cases. After you take ownership, then you can rename the folder.
After the folder has been renamed on the server side AND you have made a backup copy of the local profile, you can then delete the profile off the local machine via the standard method. You can easily get to the system properties to delete your profile by:
- Typing in sysdm.cpl at a run menu and then clicking the Advanced tab
- Right-clicking on “Computer” and choosing properties. and then going to the Advanced tab
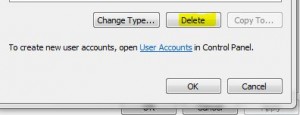
You can then select the username in question and select Delete which will delete the local copy of the profile.
Once the user logs back in, you should have a new profile which is created on the user’s behalf. After this point, you can copy any items from the local backup copy that the user may be missing. This will ensure no data is lost during the process. When the new profile is created, a new registry copy for the user is created which restores any file association problems, etc, the user may have been left with after the initial malware infection.
Google is updating how articles are shown. Don’t miss our leading home lab and tech content, written by humans, by setting Virtualization Howto as a preferred source.