security
-
Networking
Install Pi-Hole in Ubuntu 24.04 LTS
Pi-Hole is arguably one of the most popular ad-blocking solutions for home networks and home labs. Likewise, Ubuntu is one of the most popular Linux distros around. While Ubuntu 24.04 LTS is still in beta, let’s look at installing Pi-Hole…
-
Security

Windows 11 Security Ebook Download
Windows 11 has many security features built into its OS architecture, which helps to provide multiple layers of security. It relies on a structured approach that covers hardware security, operating system security, application security, identity, privacy, and cloud services. Take…
-
Containers

10 Best Docker Containers for Security in 2024
Many are embracing running containers as opposed to running a virtual machines instance for workloads. There are so many great Docker containers users can look at for many different use cases and applications. However, there are also excellent container security…
-
home lab

Firewalla Gold SE Review for Home Lab
I was recently sent one of the new Firewalla Gold SE devices to test out in the home lab. However, other than the unit being sent to me for my thoughts, this is not a paid review, and I only…
-
DevOps

Terrascan: Cloud Compliance and Security Scanner for IaC
The world is moving towards cloud-native infrastructure, making infrastructure as code (IaC) a critical part of modern software development pipelines. As businesses increasingly use cloud-native infrastructure, compliance and security violations can emerge as challenges. This is where Terrascan, a comprehensive…
-
Self hosted

Vaultwarden Setup with Traefik Self hosted deployment
With high-profile breaches in cloud-based password managers, many are looking to self-host their password solutions. While Bitwarden is an extremely popular solution, Vaultwarden is an alternative implementation to the official resource-heavy service of Bitwarden. Let’s look at Vaultwarden setup with…
-
Security

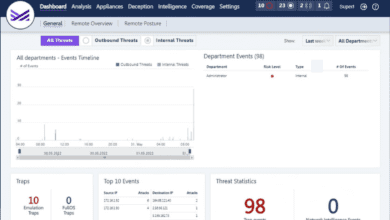
Commvault Metallic ThreatWise Early Threat Detection with Deception Technology
There is no question that cybersecurity is at the top of the minds of businesses in 2022 and beyond. High-profile ransomware attacks and data breach events continue to plague businesses worldwide with no end in sight. Threat actors continue to…
-
Security

I created ESXi ransomware its scary easy and why you need proper security
As I am sure you have been reading about a lot lately, ESXi ransomware is gaining momentum and is becoming widespread. It means we, as VI admins, must stay sharp and fully understand the risks of ESXi ransomware and just…
-
Security

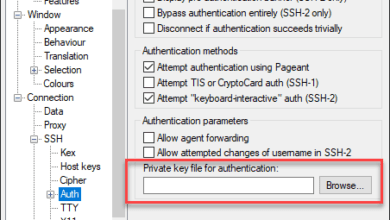
RDP vs SSH – Which should you choose?
Remote access is one of the most powerful tools in the toolbelt of an IT admin or helpdesk technician as it allows an IT worker to remotely access, configure, and administrate systems, regardless of whether they are physically near the…
-
VDI

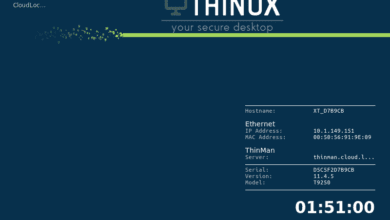
Securing Virtual Workspaces with Praim ThinOX
No longer are the majority of workers driving into the office. The remote workforce has taken shape and is a trend that will undoubtedly continue. As a result, businesses have had to shift their infrastructure to support a largely remote…